API key protection method and system based on SGX software extension instruction
A technology of key protection and extended instructions, which is applied in the field of information security, can solve the problems of high hardware cost, unsuitable automation programs, unsuitable for individual developers or small teams, etc., to achieve high mobility, high scalability, The effect of high adaptability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
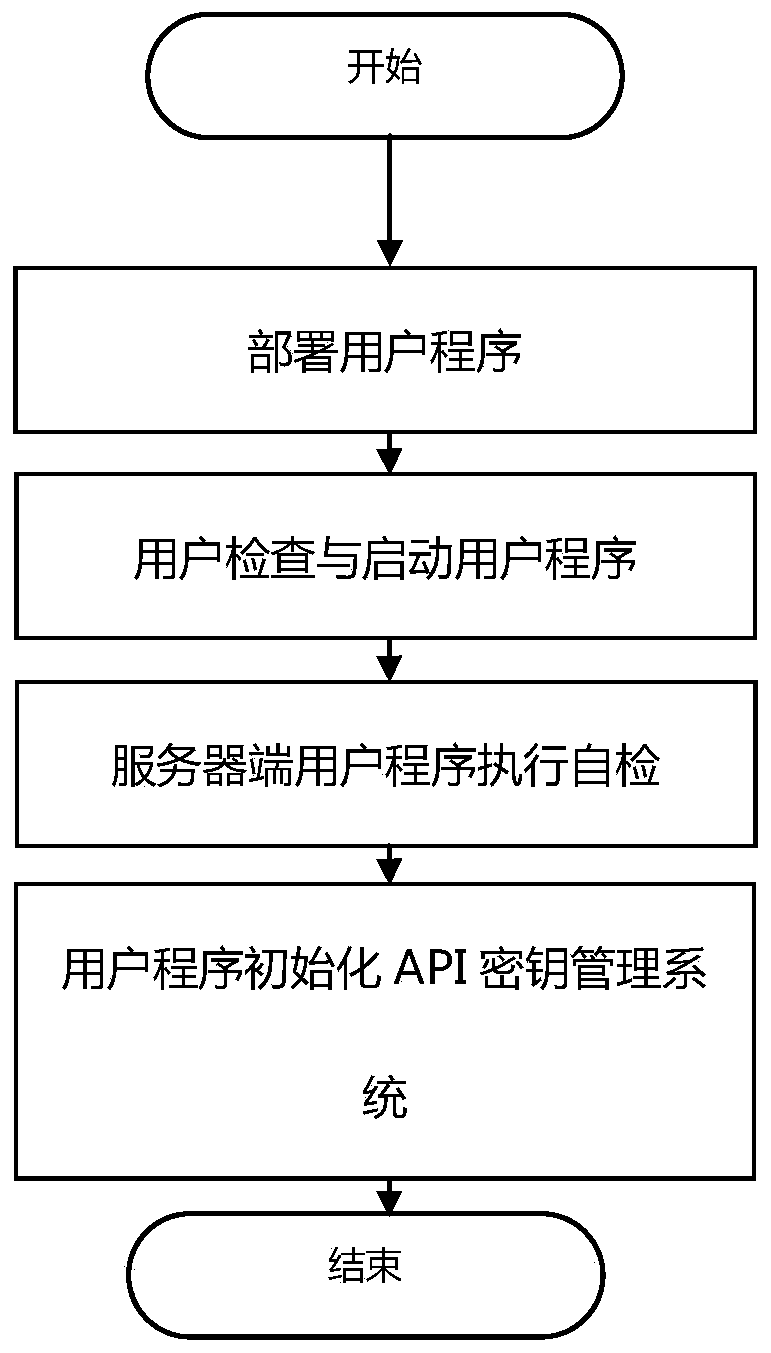
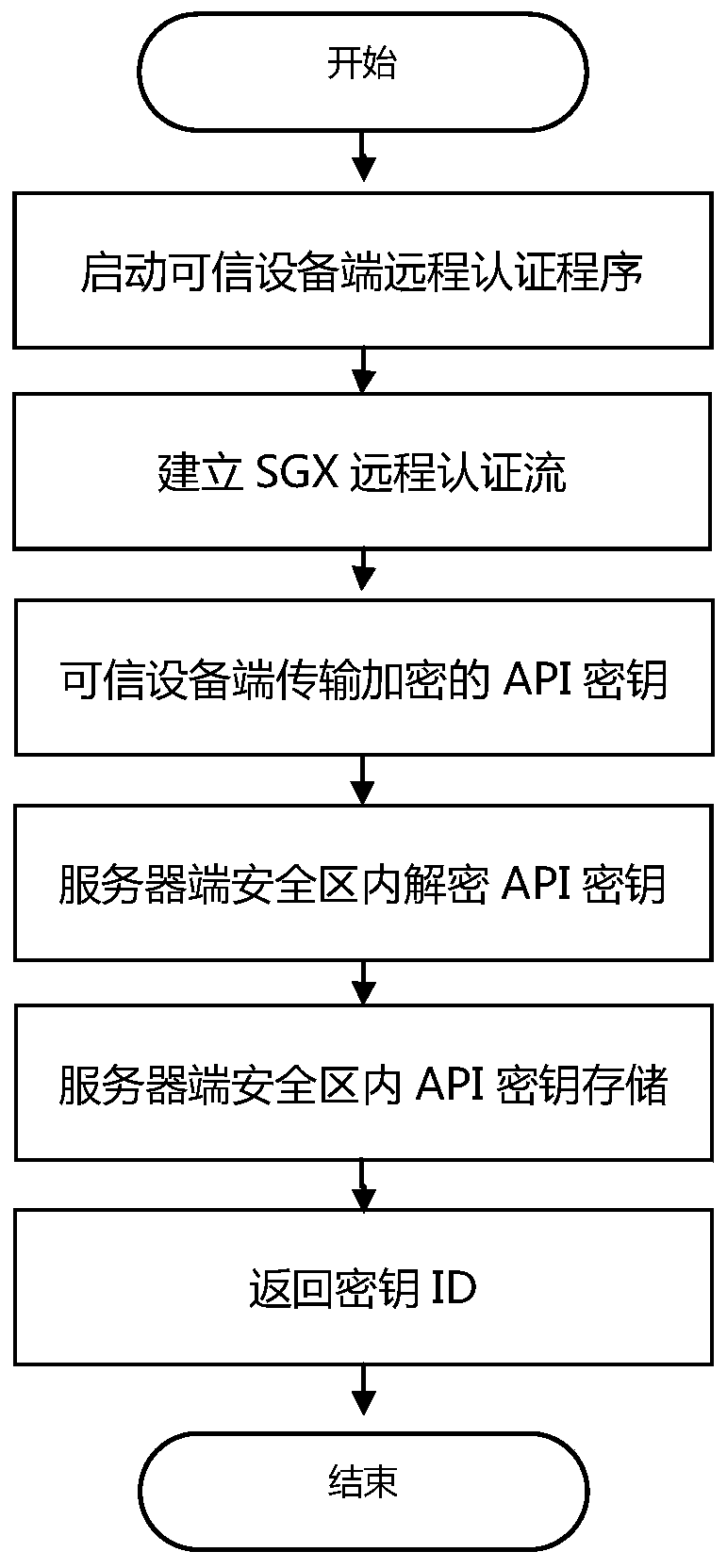
[0055] The present invention will be further described in detail below with reference to the accompanying drawings and embodiments. It should be noted that the following embodiments are intended to facilitate the understanding of the present invention, but do not limit it in any way.
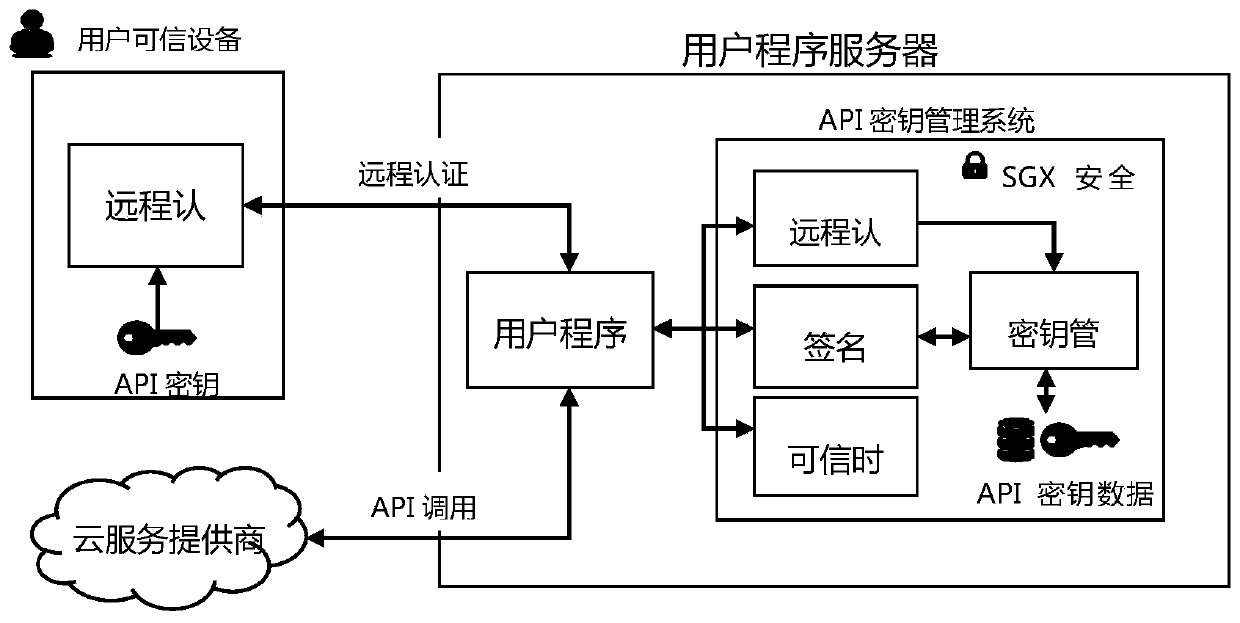
[0056] Such as figure 1 As shown, the API key protection system of the present invention includes 4 modules:
[0057] The remote authentication module runs on the server where the user program is located, and is used to cooperate with the user's trusted device to complete SGX remote authentication and securely obtain the user's API key;
[0058] The key management module runs on the server where the user program is located, and is used to store and manage the acquired API key in the SGX security zone;
[0059] The trusted time module runs on the server where the user program is located, and is used to provide trusted time stamps to the user program to enhance signature security;
[0060] The s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com