Application encrypted traffic generation method and system based on generative adversarial network
A traffic and network technology, applied in the direction of biological neural network model, transmission system, neural learning method, etc., can solve the problem of high marking cost and achieve the effect of reducing cost
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] Below in conjunction with accompanying drawing and specific embodiment, further illustrate the present invention, should be understood that these examples are only for illustrating the present invention and are not intended to limit the scope of the present invention, after having read the present invention, those skilled in the art will understand various aspects of the present invention All modifications of the valence form fall within the scope defined by the appended claims of the present application.
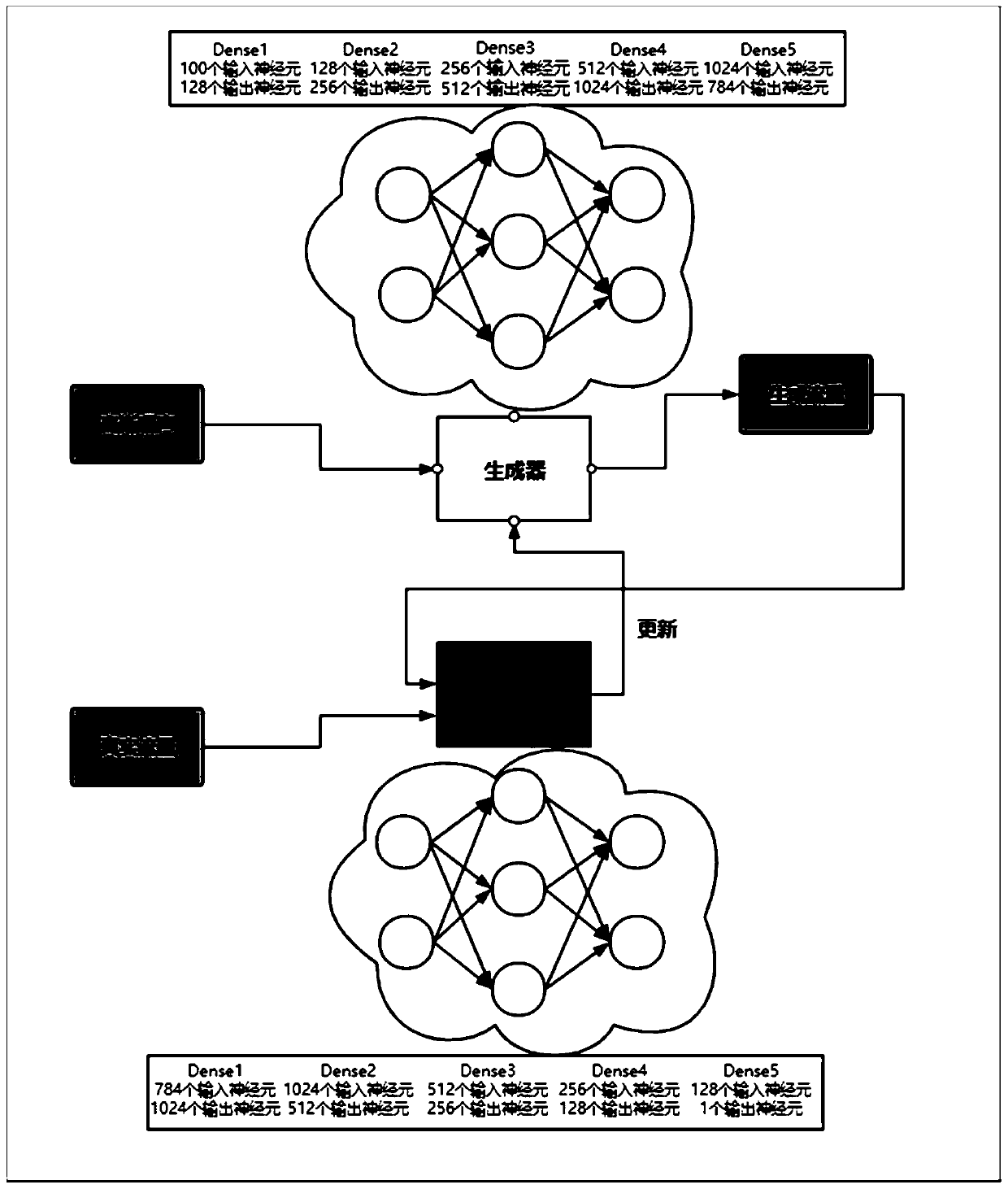
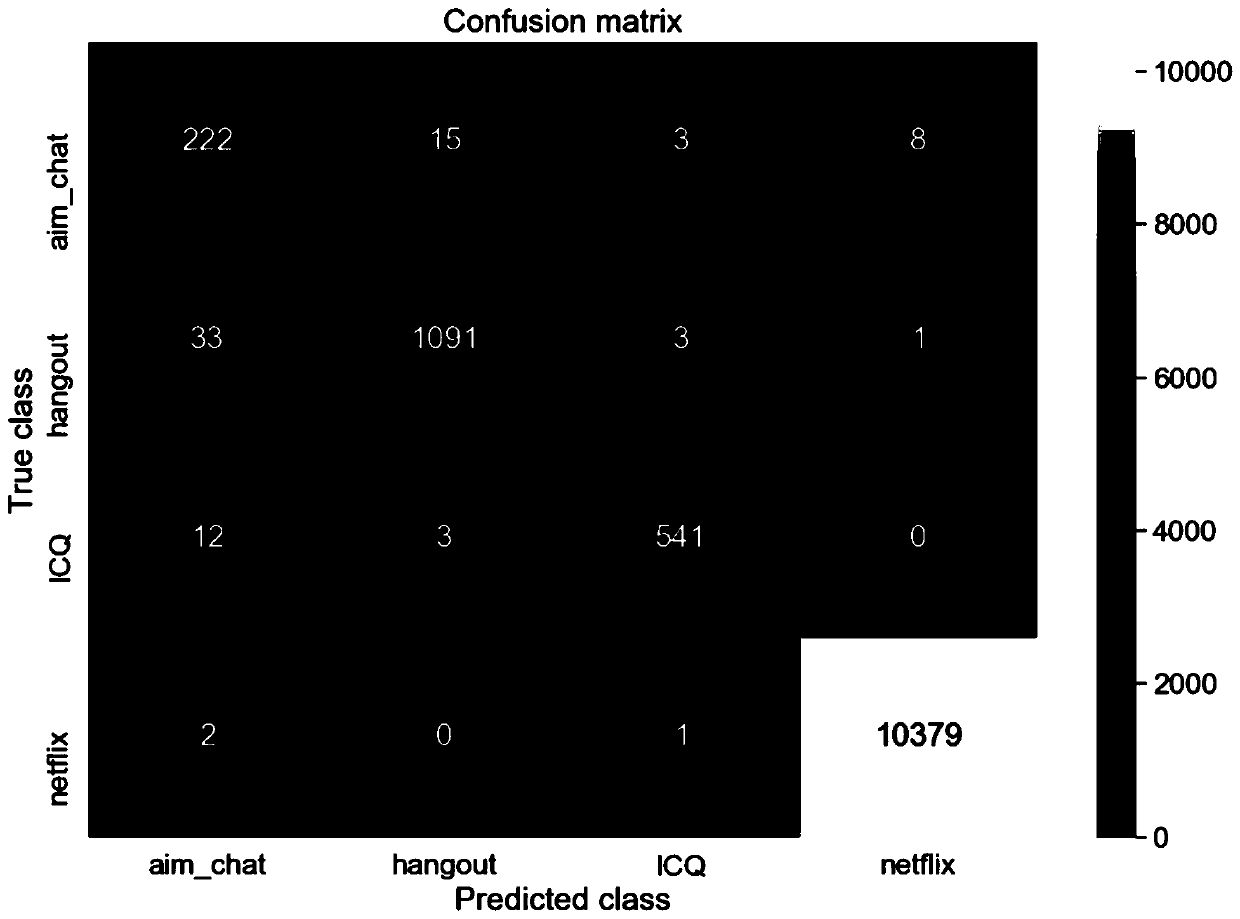
[0040] A method for generating application encrypted traffic based on Generative Adversarial Networks, such as figure 1As shown, through the encrypted traffic packet of the real application, the traffic data (including the protocol header) is extracted, converted into decimal, and intercepted to 784 bits (if it is insufficient, fill it with 0), and use " between each byte, "Segmentation, put only one traffic data in each line, put the traffic of the same application ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com