Internal isolation method for sgx security application
A security application and security isolation technology, applied in the field of computer security, can solve problems such as incompatibility of trusted computing bases, and achieve the effect of reducing trusted computing bases, having strong universality, and meeting security requirements.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0069] The present invention will be described in detail below in conjunction with specific embodiments. The following examples will help those skilled in the art to further understand the present invention, but do not limit the present invention in any form. It should be noted that those skilled in the art can make several changes and improvements without departing from the concept of the present invention. These all belong to the protection scope of the present invention.
[0070] Abbreviations and key terms involved in the present invention are defined as follows:
[0071] -TCB: Trusted Computing Base, Trusted Computing Base;
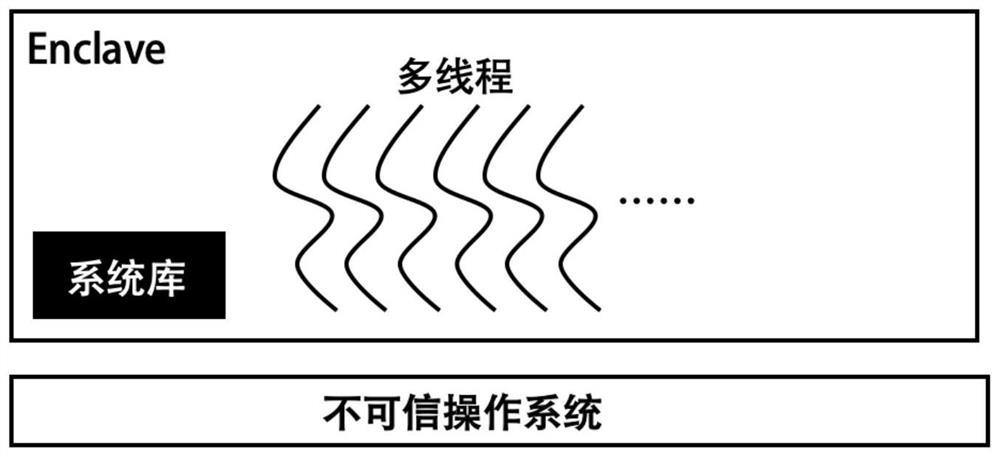
[0072] -SGX: Software Guard Extension, software guard extension;
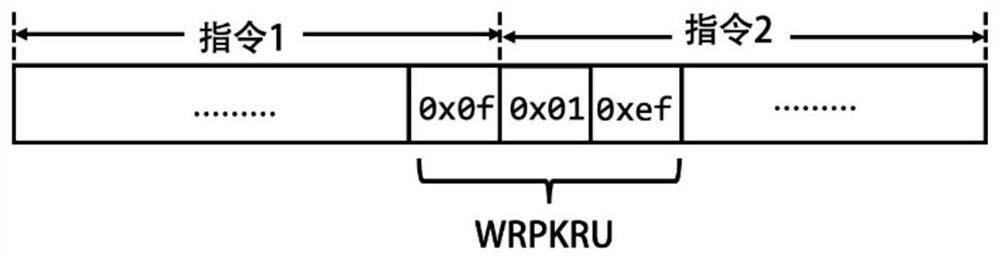
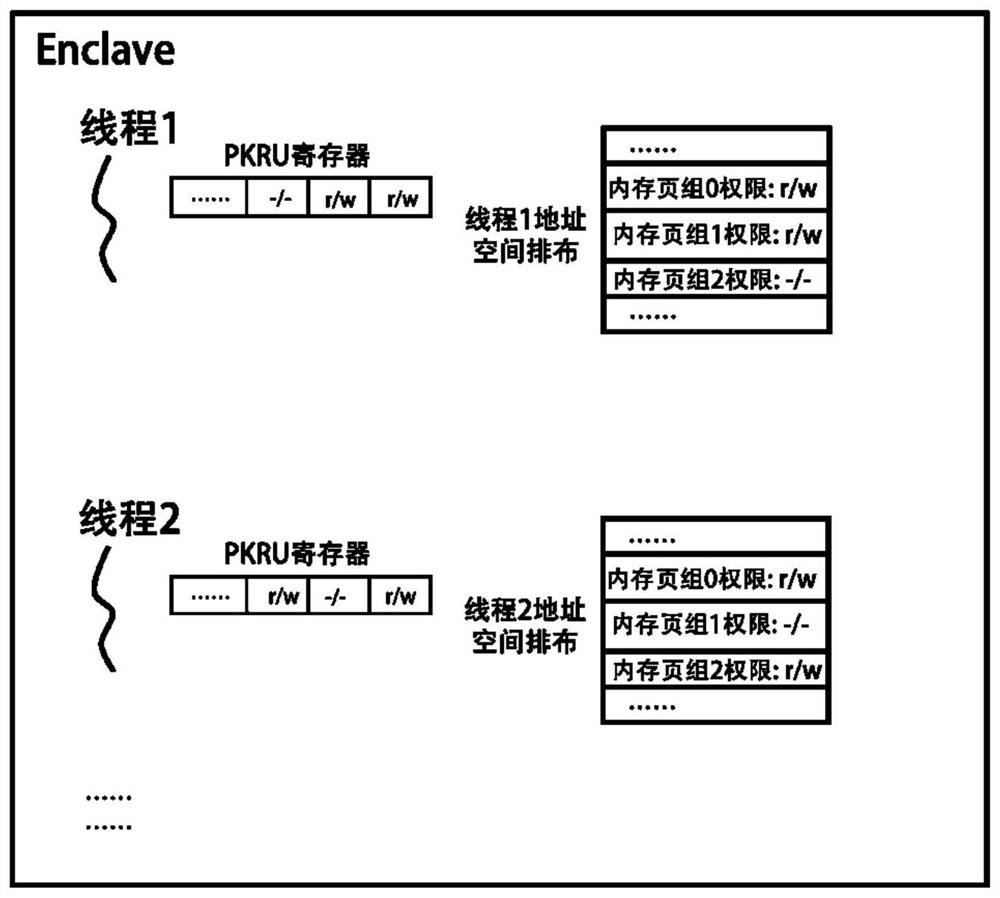
[0073] -MPK: Memory Protection Key, memory protection technology;
[0074] -RTM: Restricted Transactional Memory, hardware transactional memory technology;
[0075] -SSA: State Save Area, state save area.
[0076] According to an internal isolation method for SGX security applic...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com