Role mining optimization method based on enumeration mining method and potential constraints
An optimization method and role-based technology, applied in special data processing applications, instruments, digital data authentication, etc., can solve the problems of not considering the underlying access mode, time-consuming and laborious, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] The technical solutions of the present invention will be further described in detail below in conjunction with specific embodiments.
[0023] 1 Preliminary knowledge and problem description
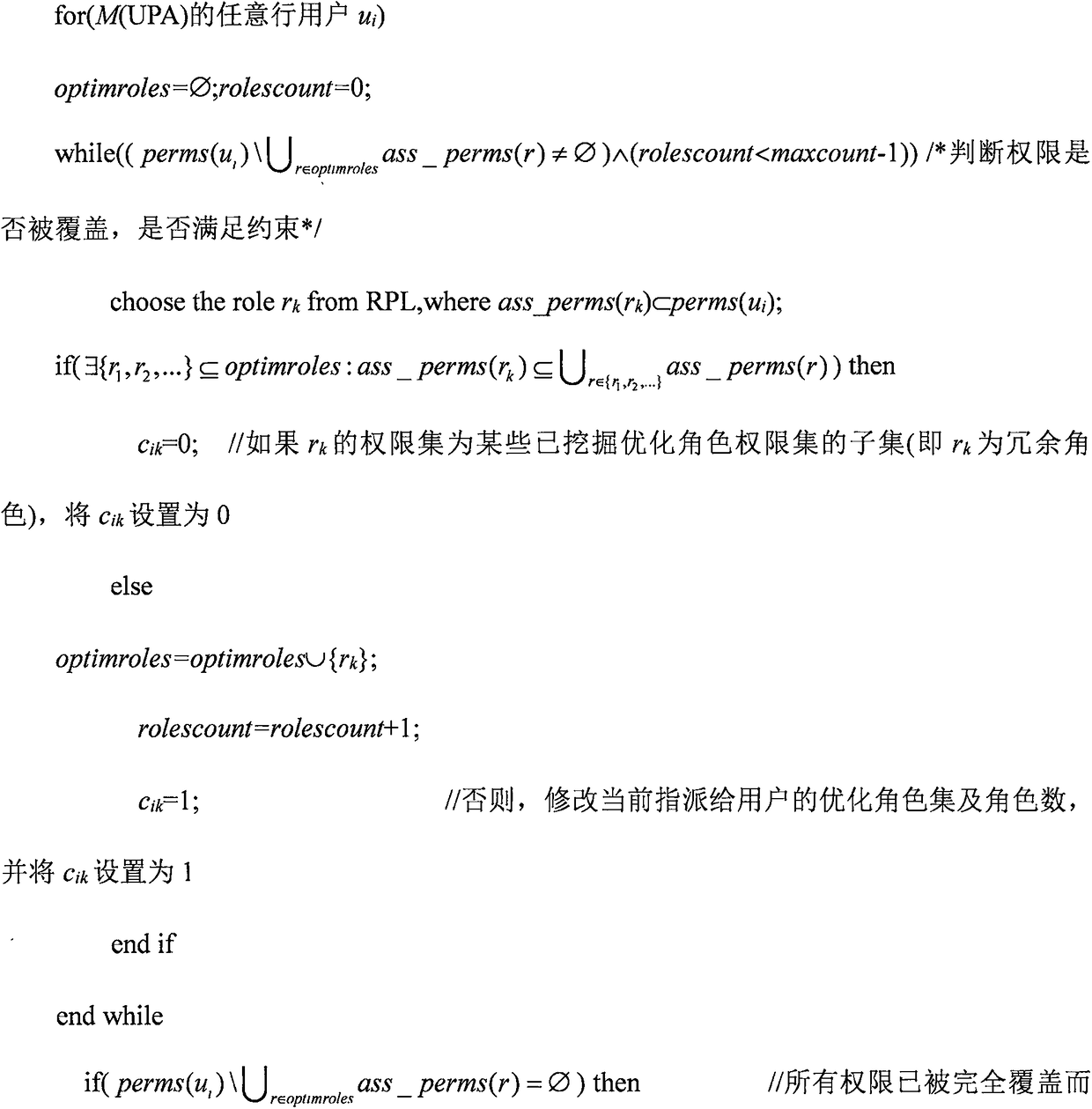
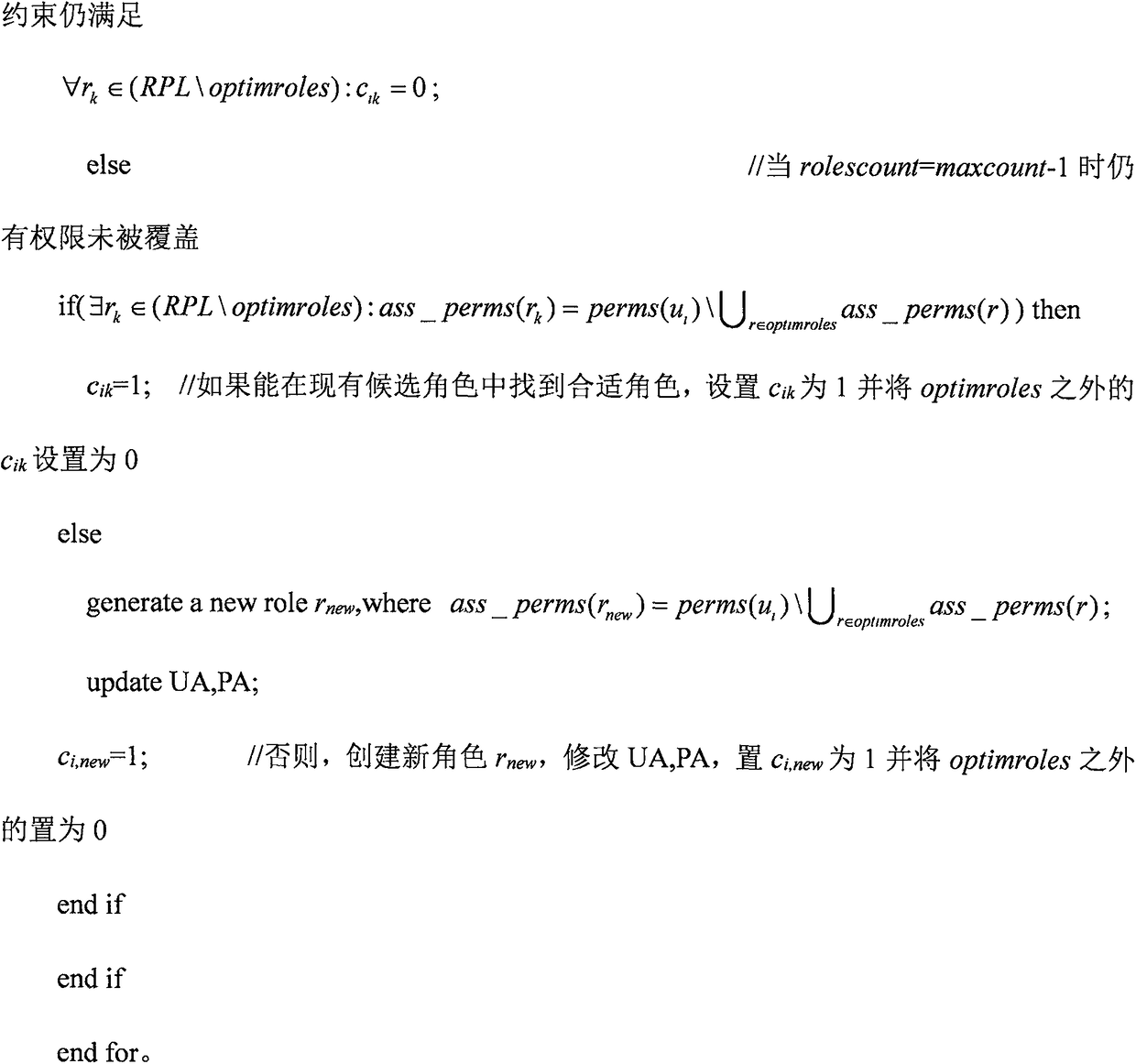
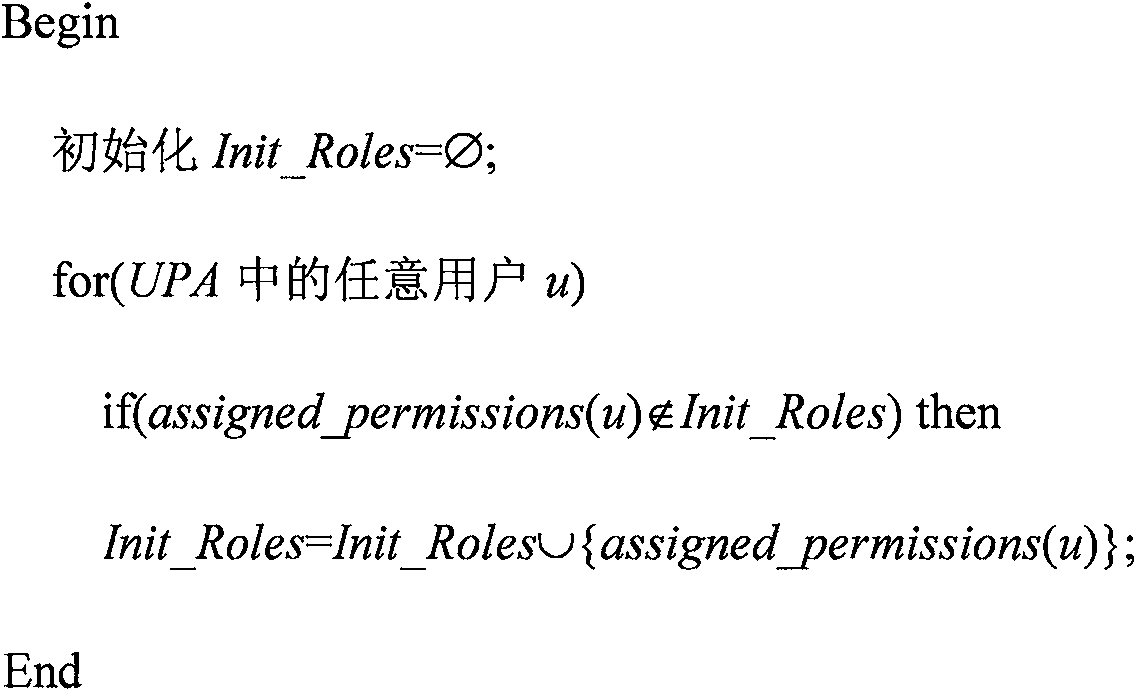
[0024] 1.1 Role mining based on enumeration method
[0025] The existing technology mines roles by enumerating different subsets of permissions at the bottom layer, and allows roles to overlap, and proposes two algorithms: full mining and fast mining. Although the former can exhaustively enumerate all candidate role sets from the user-authority assignment relationship, the time complexity is exponential and the mining efficiency is low; the latter improves the mining process and counts the number of users associated with roles, although it cannot exhaustively enumerate all roles , but the mining efficiency is better than the former. In order to reflect the efficiency and completeness of enumeration mining, the basic idea of role mining based on enumeration method: for a given a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com