Method and device for guaranteeing system security
A system security and security configuration technology, applied in the field of system security, can solve the problem of low security level of EPG equipment, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
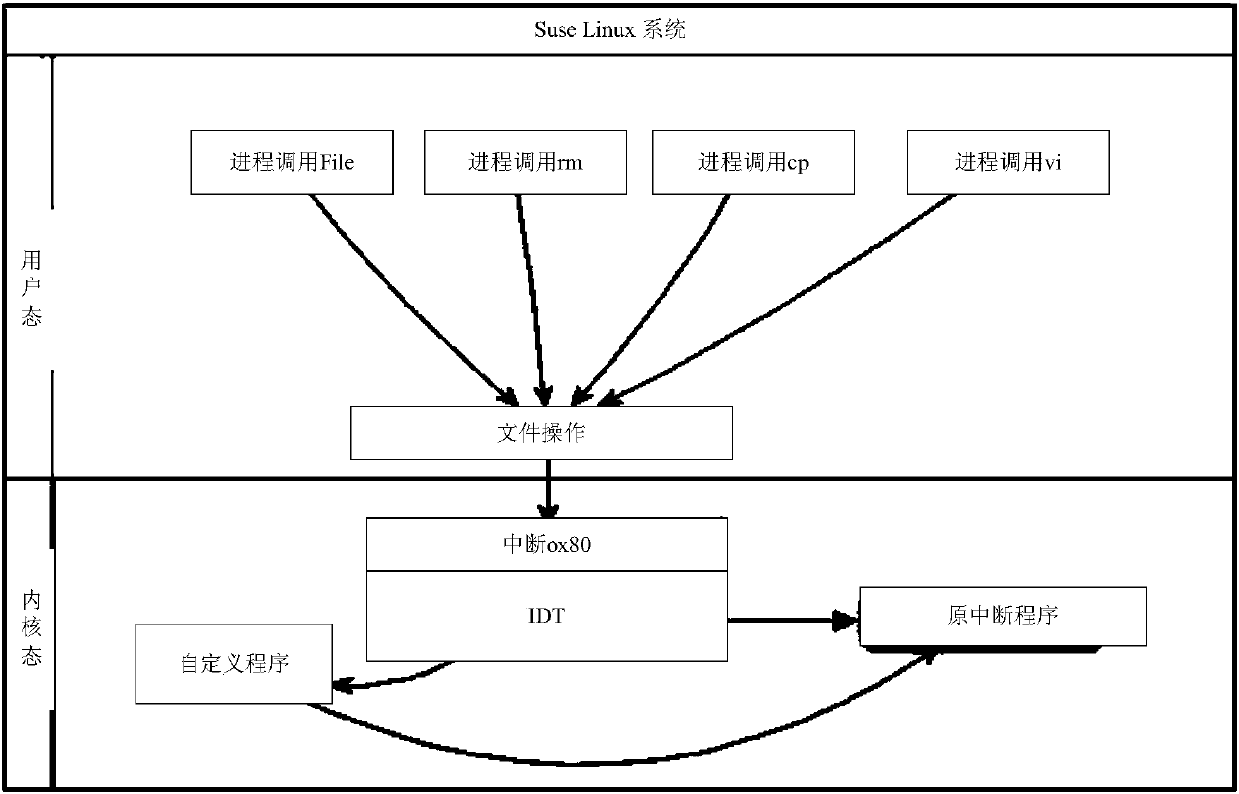
[0042] The technical solution in this application document can run on the EPG equipment in the IPTV service system, that is, execute the technical solution in the application document in the Linux system in the EPG equipment.
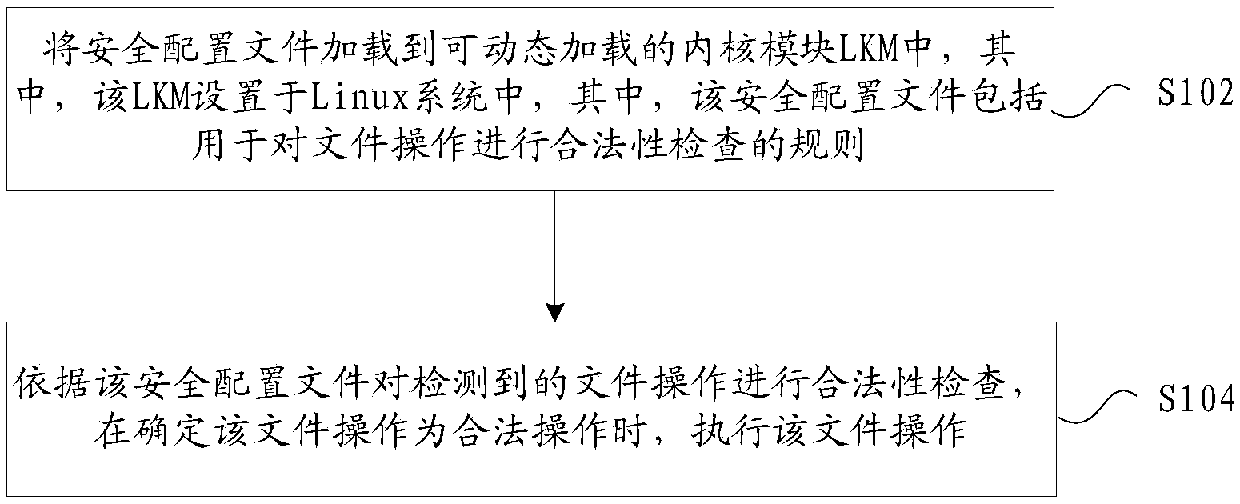
[0043] figure 1 is a flowchart of a method for ensuring system security according to an embodiment of the present invention, such as figure 1 As shown, the process includes:
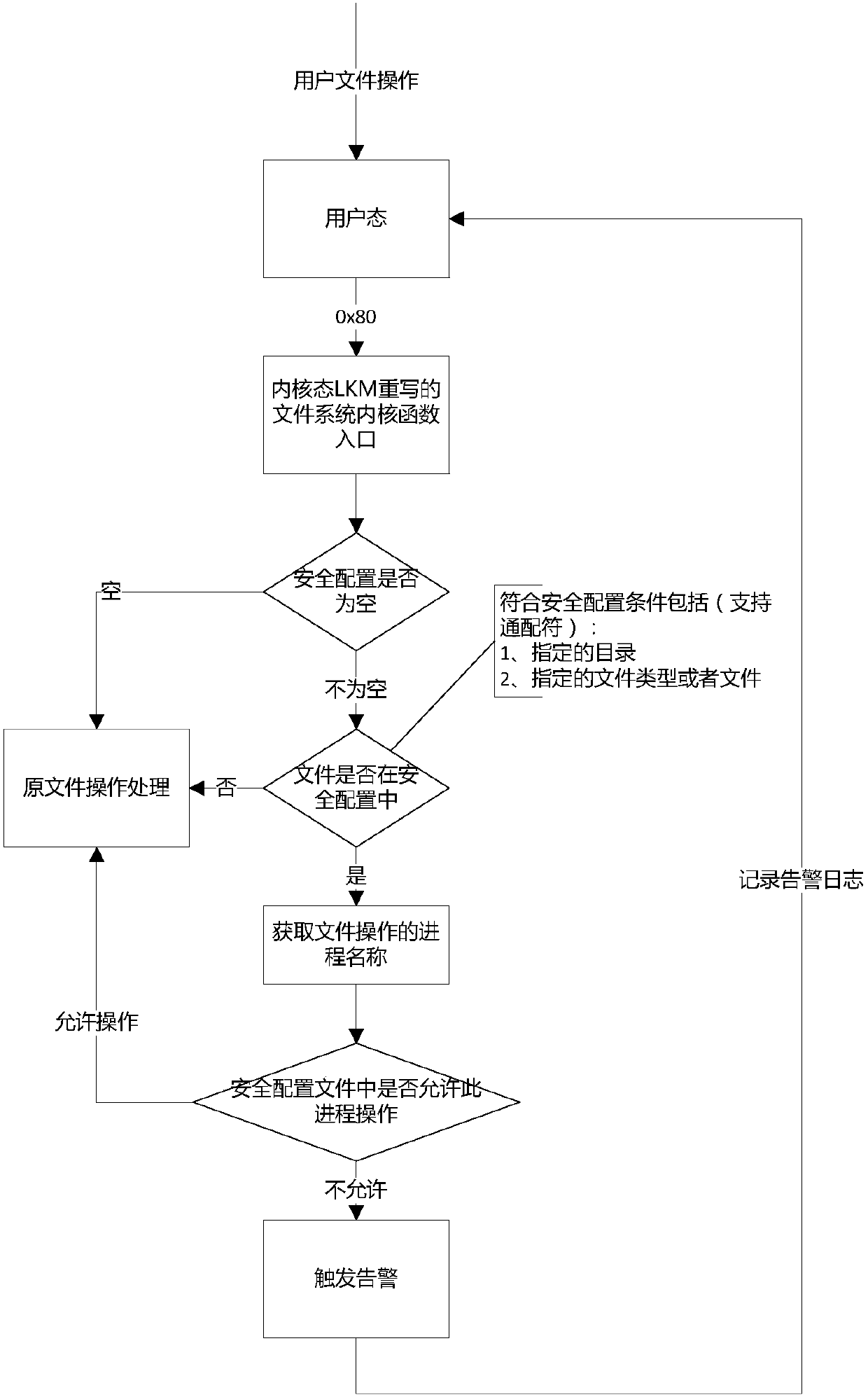
[0044] Step S102, loading the security configuration file into a dynamically loadable kernel module LKM, wherein the LKM is set in a Linux system, wherein the security configuration file includes rules for checking the validity of file operations;
[0045] Step S104, check the validity of the detected file operation according to the security configuration file, and execute the file operation when it is determined that the file operation is legal.
[0046] It should be noted that the file operations recorded in the above steps include modifying files, deleting files, moving files...
Embodiment 2
[0091] In this embodiment, a device for ensuring system security is also provided, and the device is used to realize the above embodiments and preferred implementation modes, and what has been described will not be repeated. As used below, the term "module" may be a combination of software and / or hardware that realizes a predetermined function. Although the devices described in the following embodiments are preferably implemented in software, implementations in hardware, or a combination of software and hardware are also possible and contemplated.
[0092] Figure 5 is a structural block diagram of a device for ensuring system security according to an embodiment of the present invention, such as Figure 5 As shown, the device includes:
[0093] The loading module 52 is used to load the security configuration file into the dynamically loadable kernel module LKM, wherein the LKM is set in the Linux system, wherein the security configuration file includes rules for checking the...
Embodiment 3
[0103] The embodiment of the invention also provides a storage medium. Optionally, in this embodiment, the above-mentioned storage medium may be configured to store program codes for performing the following steps:
[0104] S1, loading the security configuration file into a dynamically loadable kernel module LKM, wherein the LKM is set in a Linux system, wherein the security configuration file includes rules for checking the validity of file operations;
[0105] S2. Perform a legality check on the detected file operation according to the security configuration file, and execute the file operation when it is determined that the file operation is a legal operation.
[0106] Optionally, in this embodiment, the above-mentioned storage medium may include but not limited to: U disk, read-only memory (ROM, Read-Only Memory), random access memory (RAM, Random Access Memory), mobile hard disk, magnetic disk Various media that can store program codes such as discs or optical discs.
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com