Encryption system and method of resistance to continuous leakage based on certificate
An encryption method and certificate technology, applied in transmission systems, digital transmission systems, countermeasures against encryption mechanisms, etc., can solve problems such as system attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
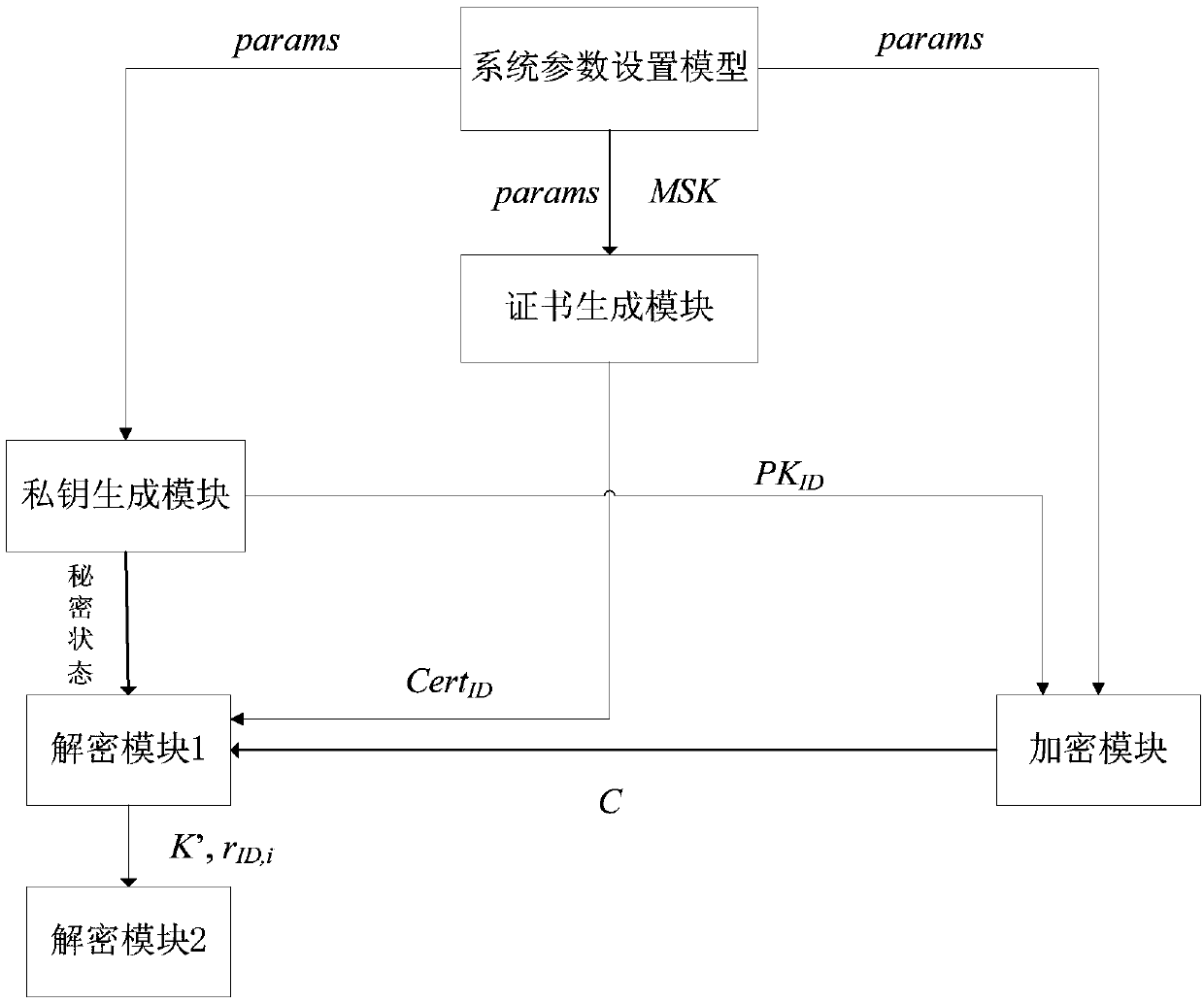
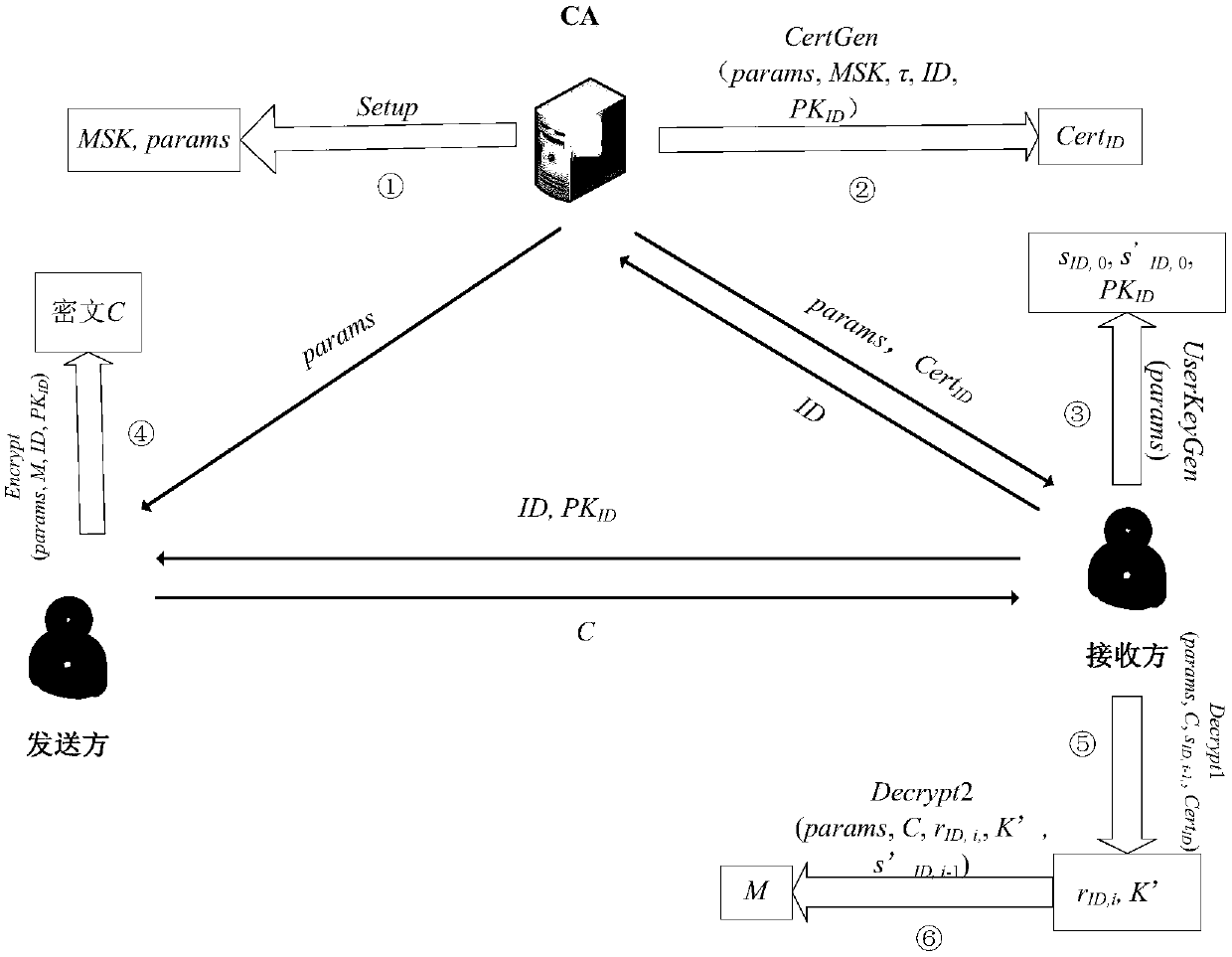
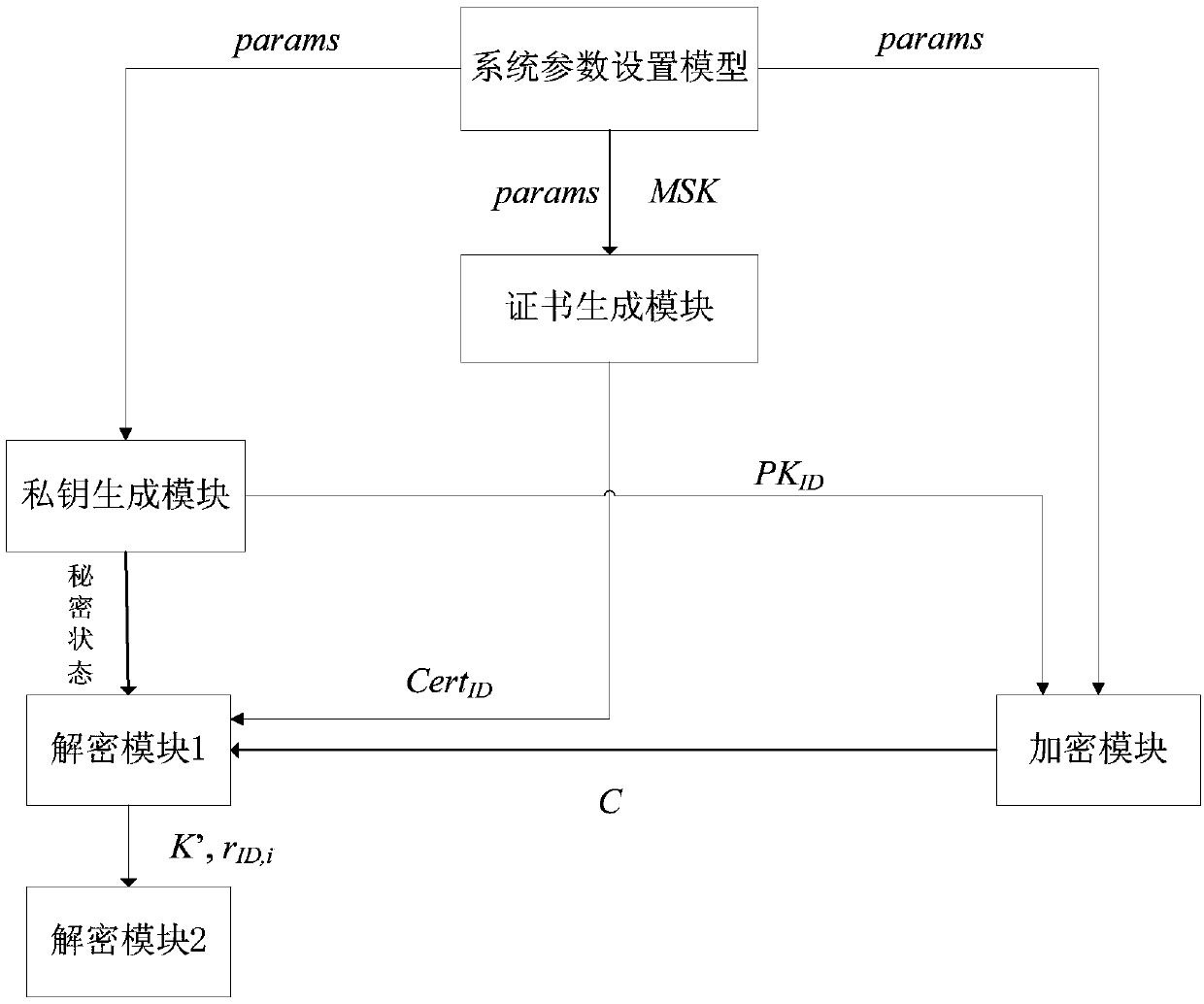
[0045] A certificate-based anti-persistent leakage encryption system and method proposed by the present invention will be described in detail below in conjunction with the accompanying drawings.
[0046] The terms used in the present invention are explained as follows:
[0047] 1. Bilinear mapping
[0048] make and are two multiplicative cyclic groups with the same prime order p. g is generator of . If mapped Satisfies the following three properties, it is called a bilinear map:
[0049] - Bilinearity: e(g a , g b )=e(g,g) ab ,in
[0050] - Non-degenerate:
[0051] - Computability: e is efficiently computable.
[0052] 2. Strong extractor
[0053] a function in If given any value and Satisfy SD((Ext(X,S),S,I),(U k ,S,I))≤ε Ext , where ε Ext ∈R + , U k and S are two respectively in {0,1} m , {0,1} μ A random variable uniformly distributed on , then this function is called the average case (k,ε Ext ) - strong extractor.
[0054] 3. Bilinear ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com