A security authentication resource allocation and management method in cloud environment
A technology of security authentication and management method, applied in the direction of digital transmission system, data exchange network, electrical components, etc., to achieve the effect of ensuring security, confidentiality, and high availability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0045] In order to make the technical problems, technical solutions and beneficial effects to be solved by the present invention clearer, the present invention will be described in detail below in conjunction with the accompanying drawings and embodiments. It should be noted that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
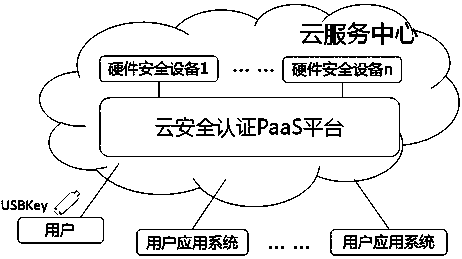
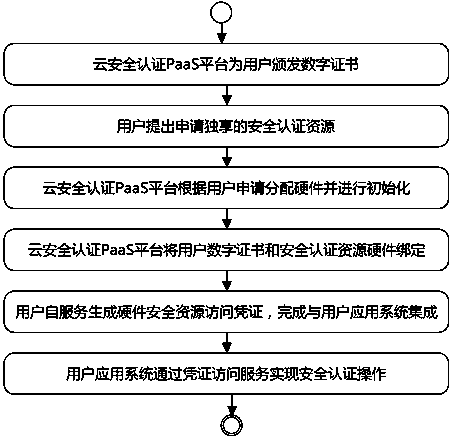
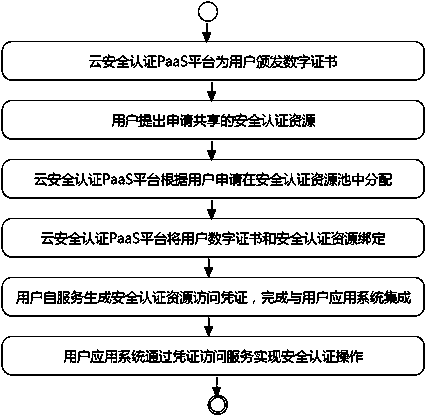
[0046] The security authentication resource allocation and management method in the cloud environment realizes the identity authentication of the cloud security authentication PaaS platform for users based on digital certificates, and implements unified allocation and management of security authentication resources by pooling hardware security device resources, providing user application systems with Efficient and flexible security certification services;
[0047] Among them, the cloud security certification PaaS platform is responsible for the issuance of digital certificates,...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com