An exception handling method for ID card authentication information processing request
A technology for information processing request and exception handling, applied in the electronic field, which can solve the problems of theft, loss of ID card, malicious use of ID card, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
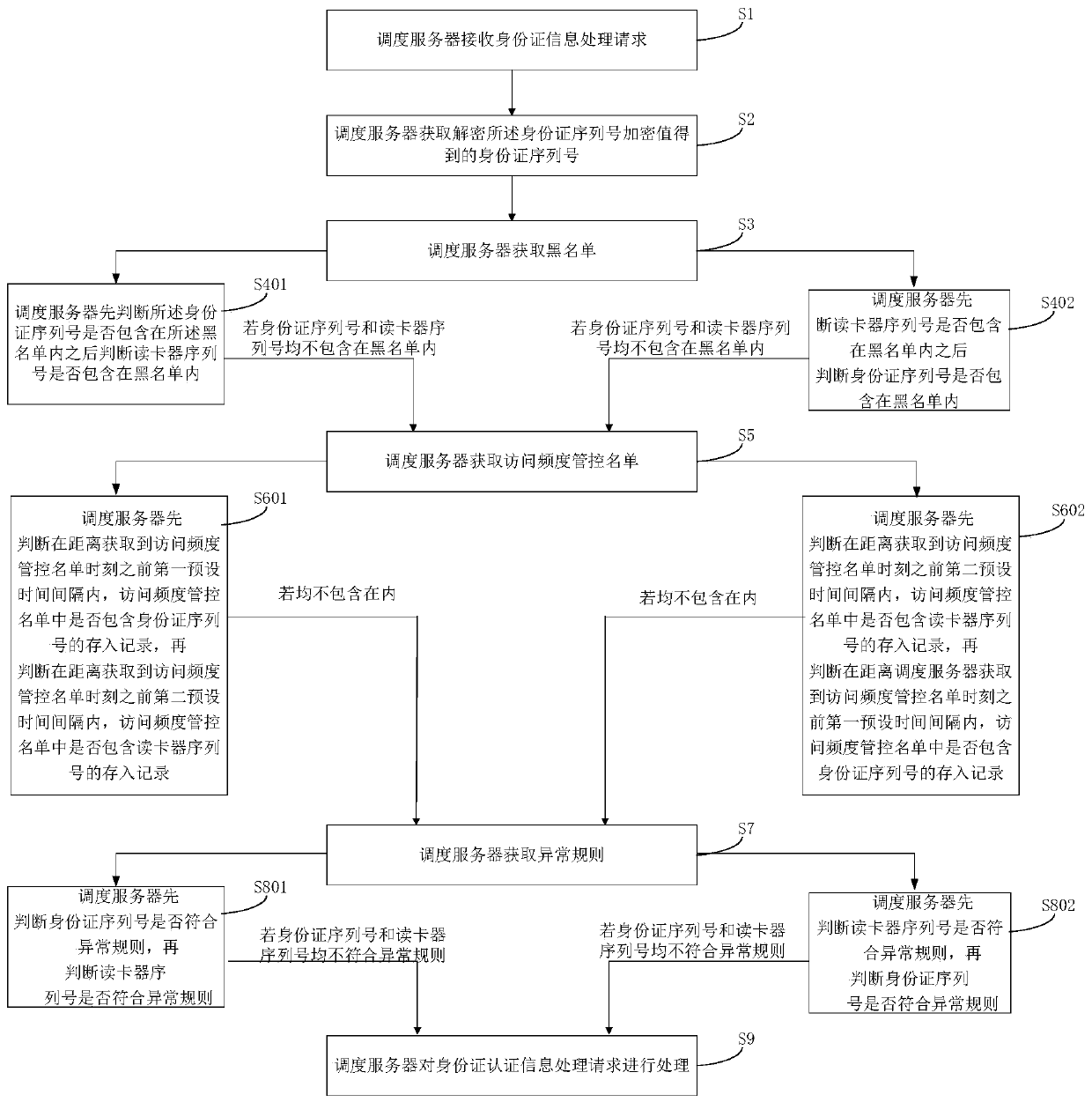
[0024] This embodiment provides a method for processing a request for processing ID card authentication information, such as figure 1 shown, including the following steps:
[0025] S1: The scheduling server receives the ID card authentication information processing request, and the ID card authentication information processing request includes: the encrypted value of the ID card serial number and the card reader serial number;
[0026] The ID card processing request is a processing request initiated by the ID card reader. After the scheduling server determines that the ID card processing request is a legal processing request, it allocates an idle security authentication module for the ID card processing request according to the preset rules. The authentication module performs data interaction with the originator of the ID card processing request. The encrypted ID card serial number is obtained by encrypting the ID card serial number obtained from the ID card by the ID card rea...
Embodiment 2
[0104] This embodiment provides an ID card authentication information processing request exception handling system, such as figure 2 As shown, including dispatching server 201 and ID card reader 202:
[0105] Wherein, the ID card reader 202 is used to generate an ID card authentication information processing request, and send the ID card processing request to the scheduling server 201; wherein, the ID card authentication information processing request includes: ID card serial number encryption value and card reading device serial number;
[0106] The scheduling server 201 is configured to receive an ID card authentication information processing request, and obtain the ID card serial number obtained by decrypting the encrypted value of the ID card serial number;
[0107] The scheduling server 201 is also used to obtain the blacklist, and judge whether the ID card serial number is included in the blacklist, and if the ID card serial number is included in the blacklist, then te...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com