Attribute-based encryption method for resisting continuous auxiliary input leakage of secret keys
An auxiliary input and attribute encryption technology, applied in the field of cryptography, can solve problems such as inability to use cryptographic schemes in combination, rare, key leakage, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] The present invention will be described in detail below in conjunction with the implementations shown in the drawings, but it should be noted that these implementations are not limitations of the present invention, and those of ordinary skill in the art based on the functions, methods, or structural changes made by these implementations Equivalent transformations or substitutions all fall within the protection scope of the present invention.
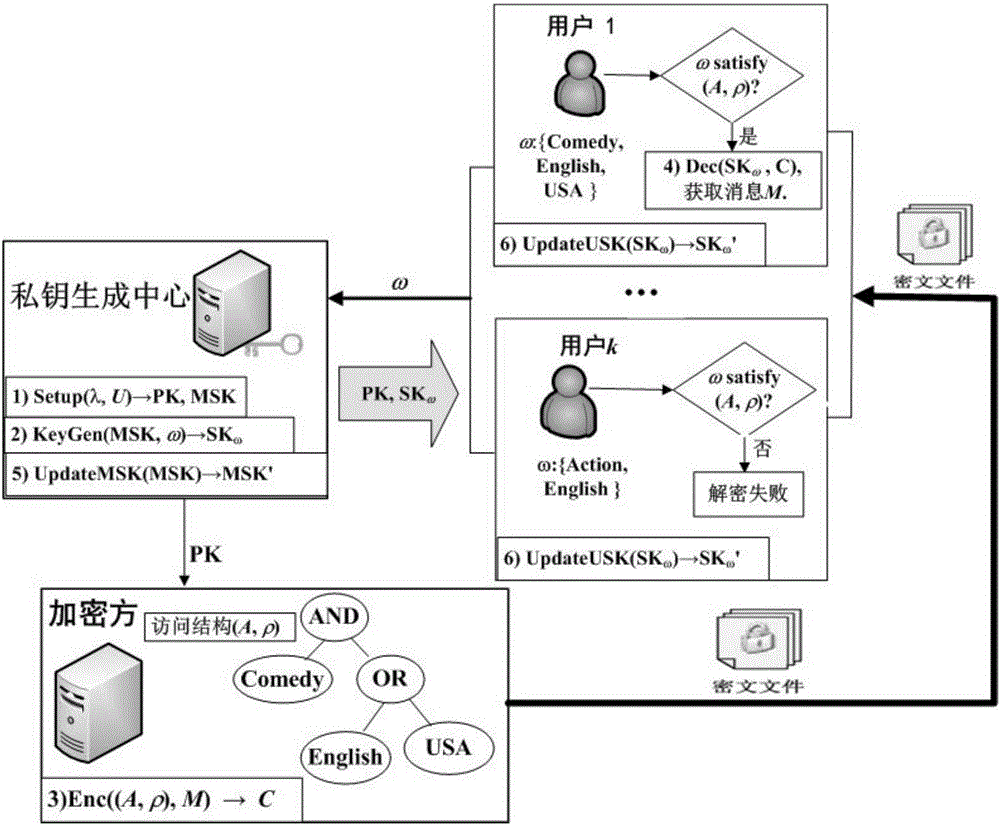
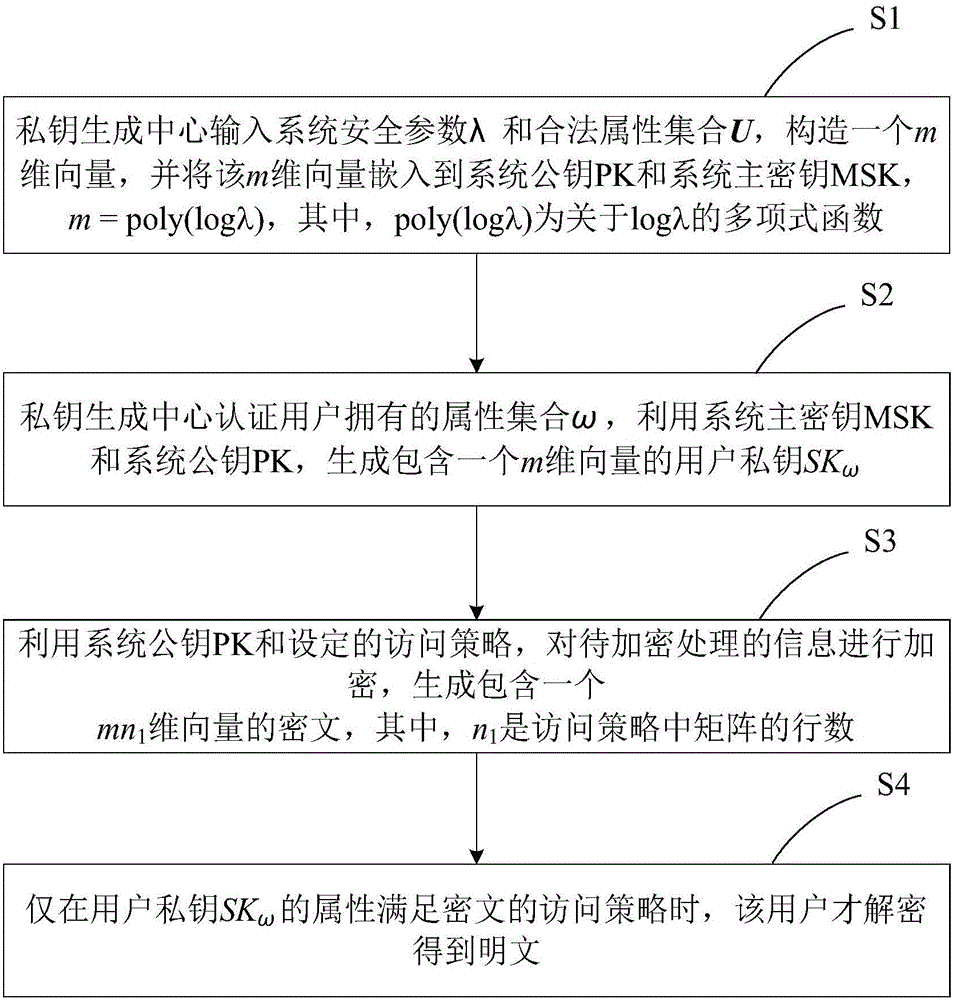
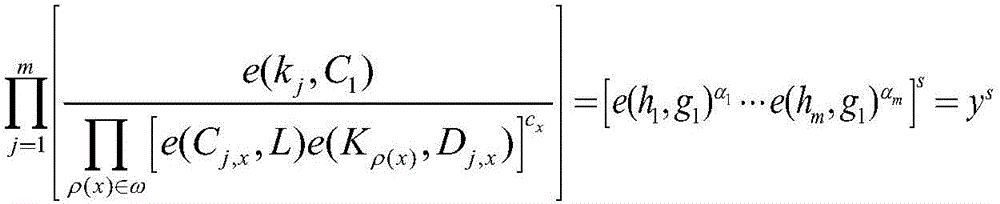
[0054] Please refer to figure 1 and figure 2 Shown is a specific implementation of an attribute-based encryption method against key continuous auxiliary input leakage in the present invention.
[0055] The implementation of an attribute-based encryption method against key continuous assisted input leakage shown in this embodiment relies on an attribute-based encryption computer system, which includes: a user, which acts as a message encryption party or a ciphertext Receiver; a private key generation center, as a trusted third p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com