Integrity verification method based on active attack resistance in cloud storage
An active attack and cloud storage technology, applied in the field of communication security, can solve problems such as being unable to resist active attacks, and achieve the effect of reducing communication traffic
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The present invention will be further described below in conjunction with the accompanying drawings.
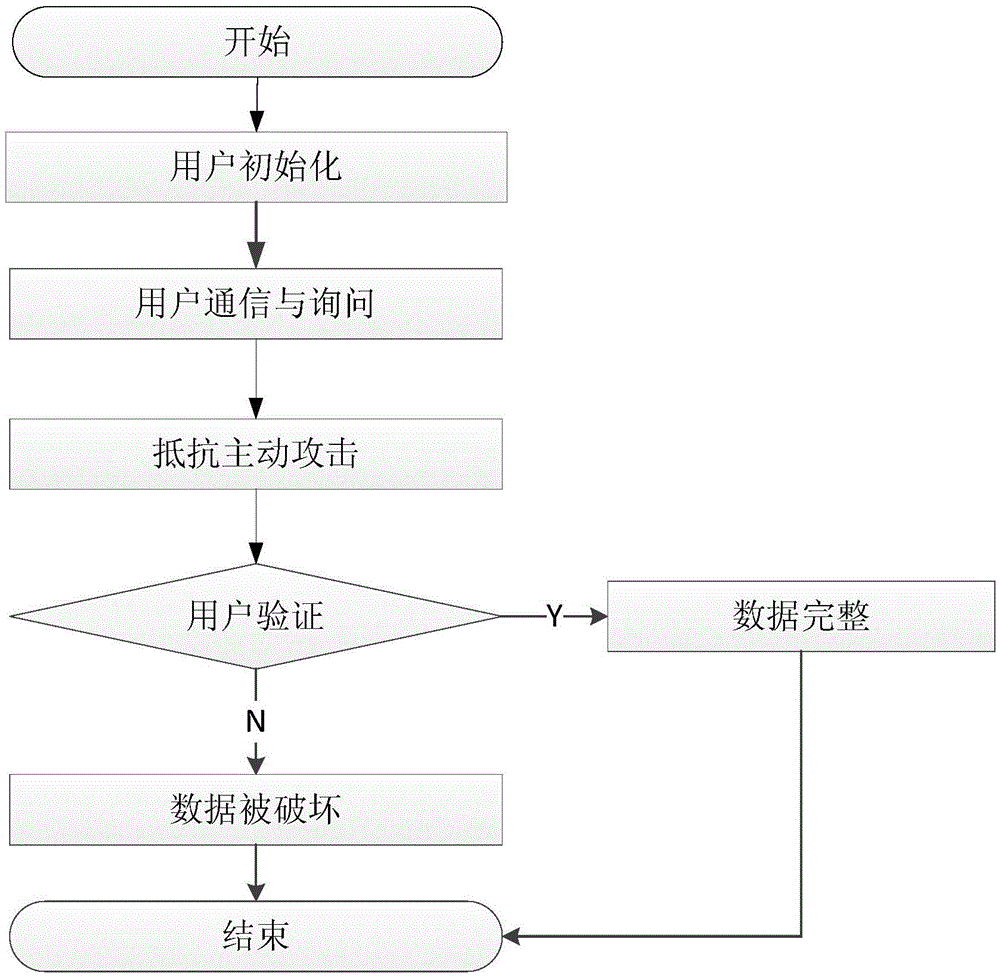
[0034] refer to figure 1 , the implementation steps of the present invention are as follows:
[0035] Step 1, user initialization.
[0036] (1a) Chunk the file:
[0037] When the user needs to send the local file F to the cloud service provider CSP, the user first needs to perform the block operation of the file. The file block technology includes uniform block technology, overlapping block technology, and variable length block technology. The example selects the uniform block technology, that is, the user needs to divide the file F to be stored into n blocks evenly, and set the length of the file F to be L to generate a block file The length of each block is When the last block cannot reach the block length When , add 0 behind it to make its length reach
[0038] (1b) The user divides the block file by the following formula Main tag for generating chunked...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com