Method for hiding secret information in images
A technology of secret information and images, applied in the field of information security, can solve problems such as the exact method has not been proposed, the loss of strong robustness, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0062] Embodiments of the present invention will be further described below with reference to the drawings and specific embodiments.
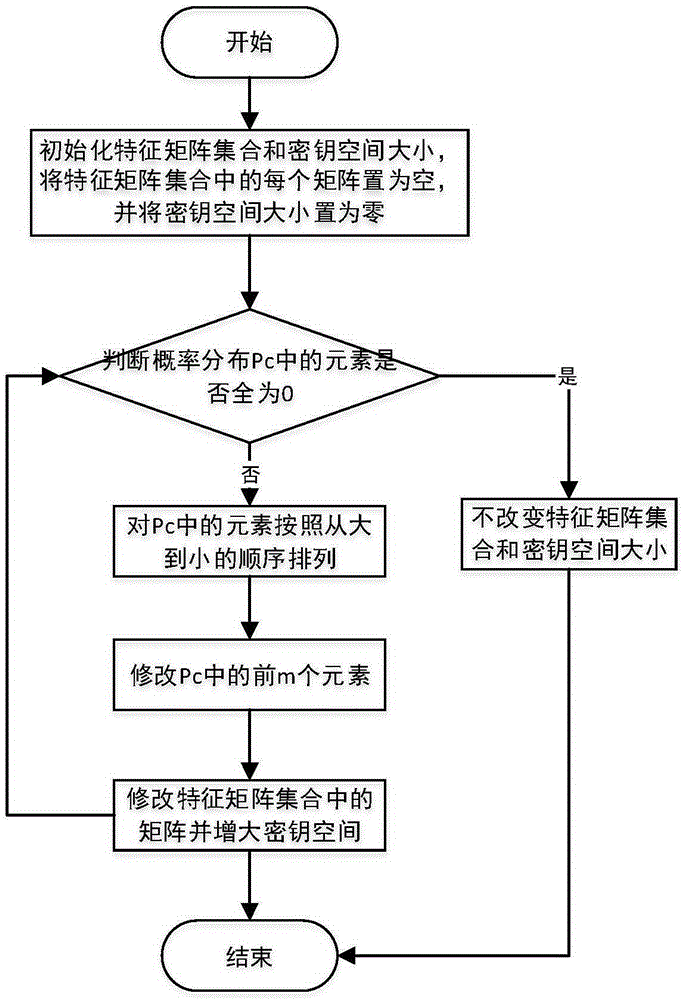
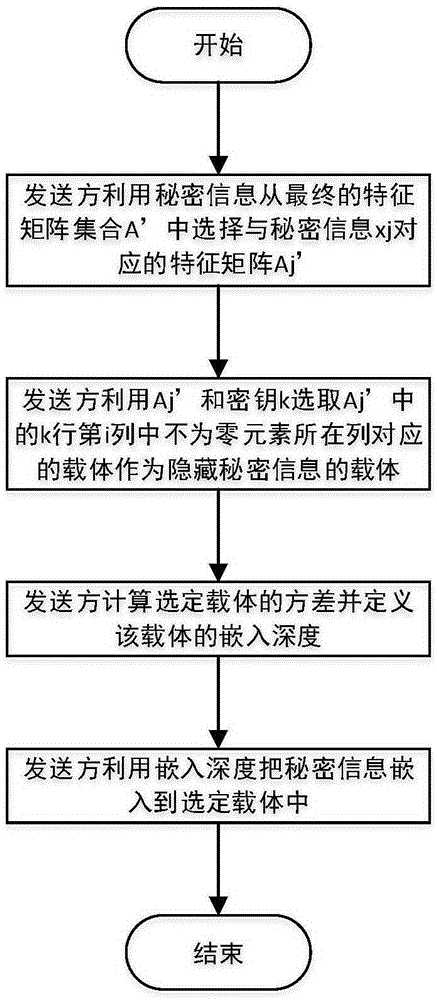
[0063] refer to figure 1 , the present invention is to realize steps as follows:
[0064] Step 1, the sender determines the probability distribution of the bearers.
[0065] (1a) The sender uses the shared key k to select the carrier image from the carrier image database;
[0066] (1b) The sender divides the selected carrier image into small blocks of 8×8, and calculates the blur value of each small block;
[0067] (1b1) Define the membership degree of fuzzy set as follows:
[0068] u ( p , q ) = 1 1 + | d ( p , q ) - d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com