Network security posture assessment method
A network security and situation assessment technology, applied in the assessment field, can solve the problems of complex vulnerability assessment models and low accuracy of assessment results, achieving high accuracy, overcoming differences, and simple overall assessment models
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
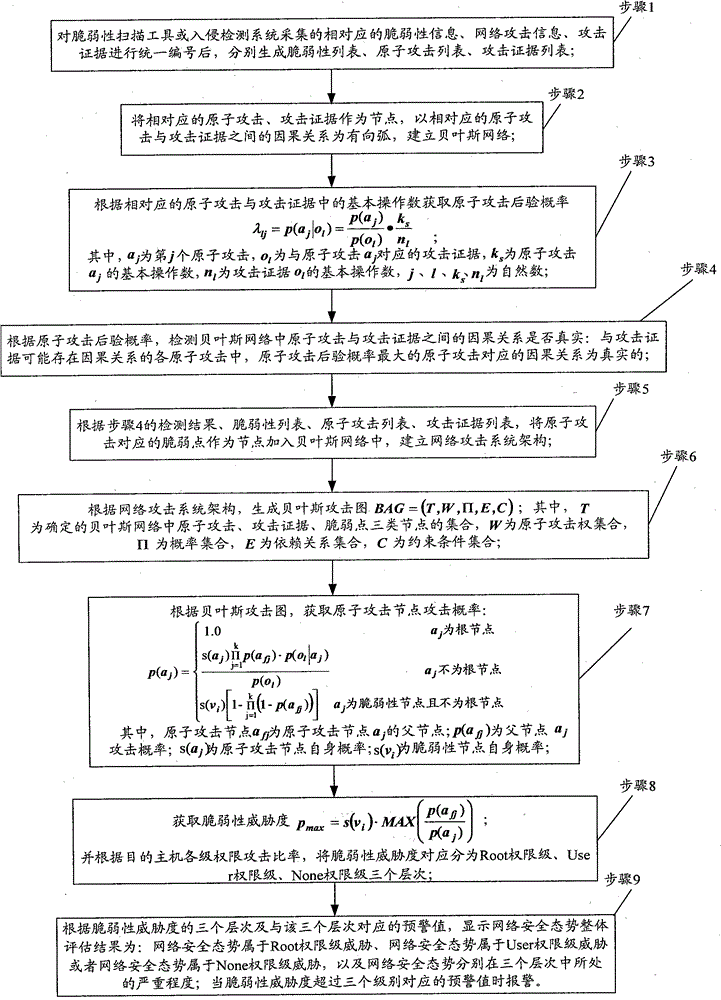
[0025] figure 1 It is an overall flow chart of the network security situation assessment method of the present invention. like figure 1 As shown, the network security situation assessment method of the present invention includes the following steps:
[0026] Step 1. After uniformly numbering the corresponding vulnerability information, network attack information, and attack evidence collected by the vulnerability scanning tool or the intrusion detection system, generate a vulnerability list, an atomic attack list, and an attack evidence list respectively.
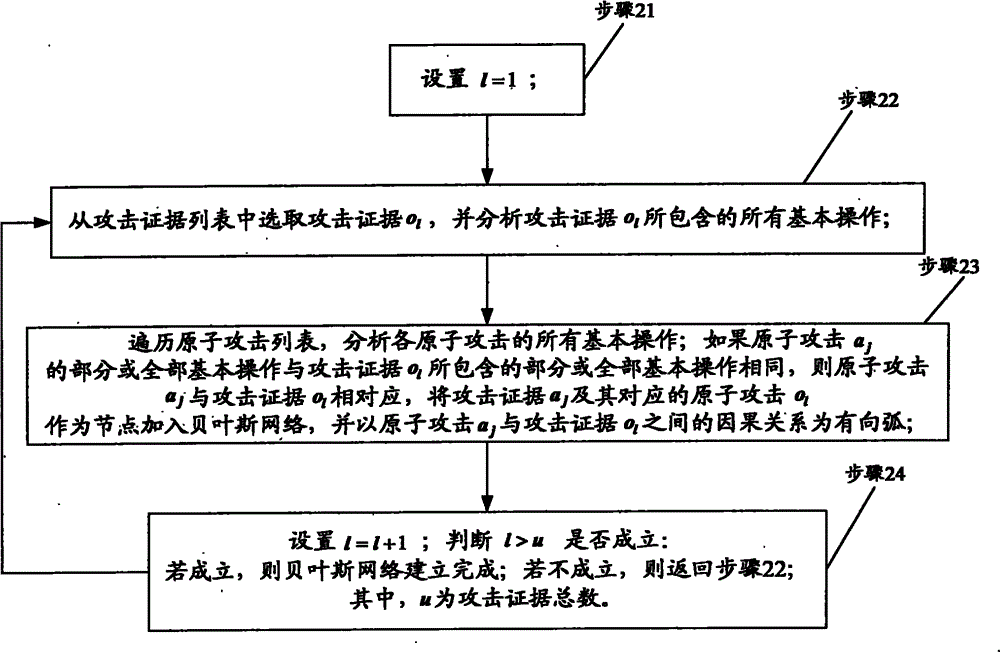
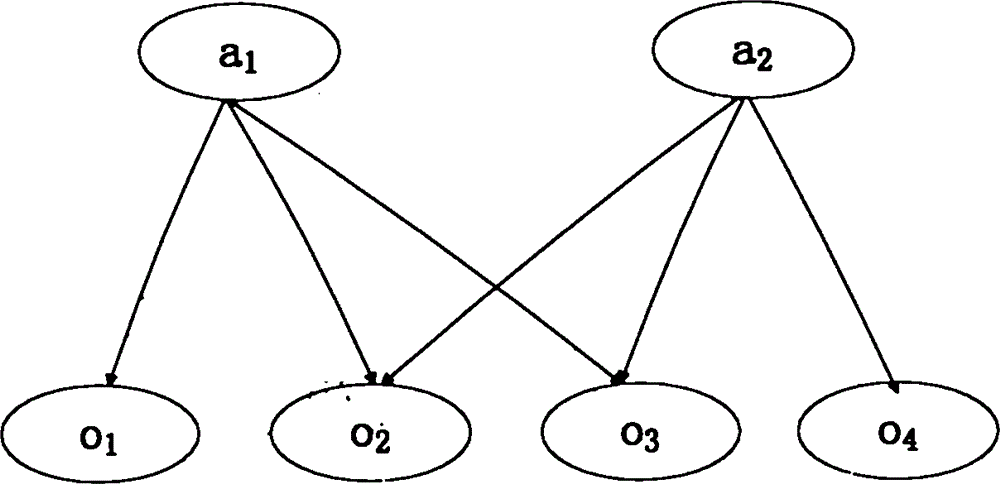
[0027] Step 2. Taking the corresponding atomic attack and attack evidence as nodes, and taking the causal relationship between the corresponding atomic attack and attack evidence as ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com