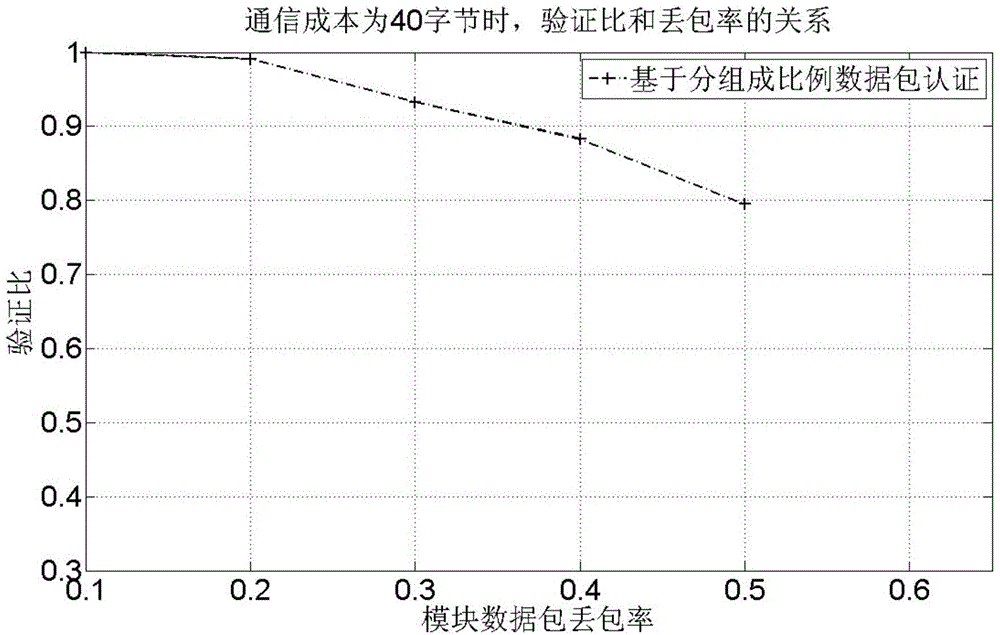
Safety multicast source authentication method based on group data packet coupling
An authentication method and secure multicast technology, applied in the field of network communication, can solve problems such as information redundancy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] Specific embodiments of the present invention will be described below in conjunction with the accompanying drawings, so that those skilled in the art can better understand the present invention. It should be noted that in the following description, when detailed descriptions of known functions and designs may dilute the main content of the present invention, these descriptions will be omitted here.
[0042] figure 1 It is a schematic diagram of the security multicast source authentication method based on packet data packet matching in the present invention.
[0043] In this example, if figure 1 As shown, all data packets and their groups are used as nodes to carry out hash calculations. In this embodiment, MD5 is used to obtain the corresponding summary value and joint summary value H mi 、H 5 , sign the node at the root of the tree to get the root signature S sig . The root signature of the tree chain is performed using 128-byte RSA (RSA: public key encryption algo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com