Method and system for detecting hostile attack on Internet information system
A malicious attack, information system technology, applied in the usage of multiple keys/algorithms, platform integrity maintenance, etc., can solve the problems of data inconsistency, large detection workload, large differences, etc., to reduce labor costs, reduce workload, the effect of reducing workload
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0064] In order to make the object, technical solution and advantages of the present invention more clear and definite, the present invention will be further described in detail below with reference to the accompanying drawings and examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
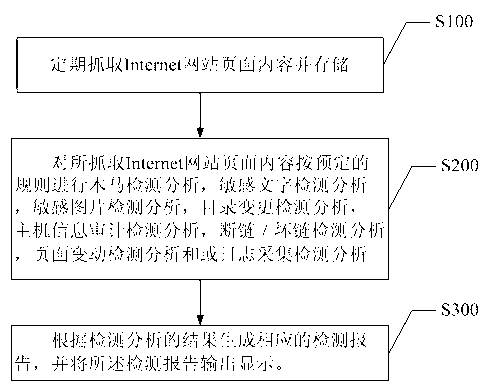
[0065] Such as figure 1 What is shown is a flowchart of a preferred embodiment of a method for detecting malicious attacks on Internet information systems in the present invention. Specifically include the following steps:
[0066] S100. Periodically capture and store page content of Internet websites.
[0067] In a specific embodiment, the Internet website page content is regularly captured mainly through the NMAP protocol and / or the SYSLOG protocol. Among them, NMap, also known as Network Mapper, is a network scanning and sniffing toolkit under Linux. The SYSLOG protocol is used fo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com