Access authentication method and system in mobile communication network
A mobile communication and access authentication technology, applied in the field of mobile communication, can solve the problems of inability to do reasonable prevention, man-in-the-middle attacks, attacks, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0073] Specific embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
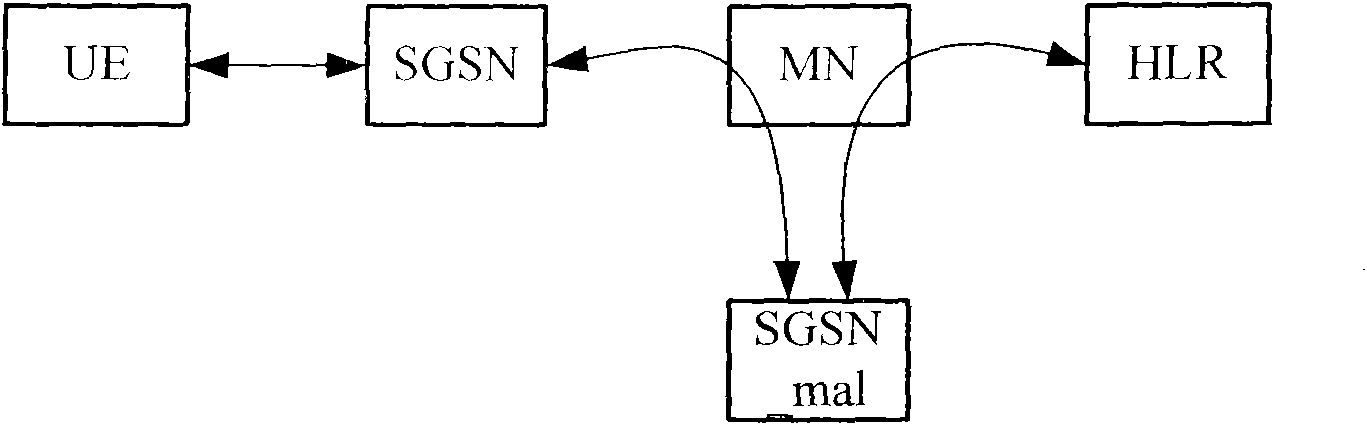
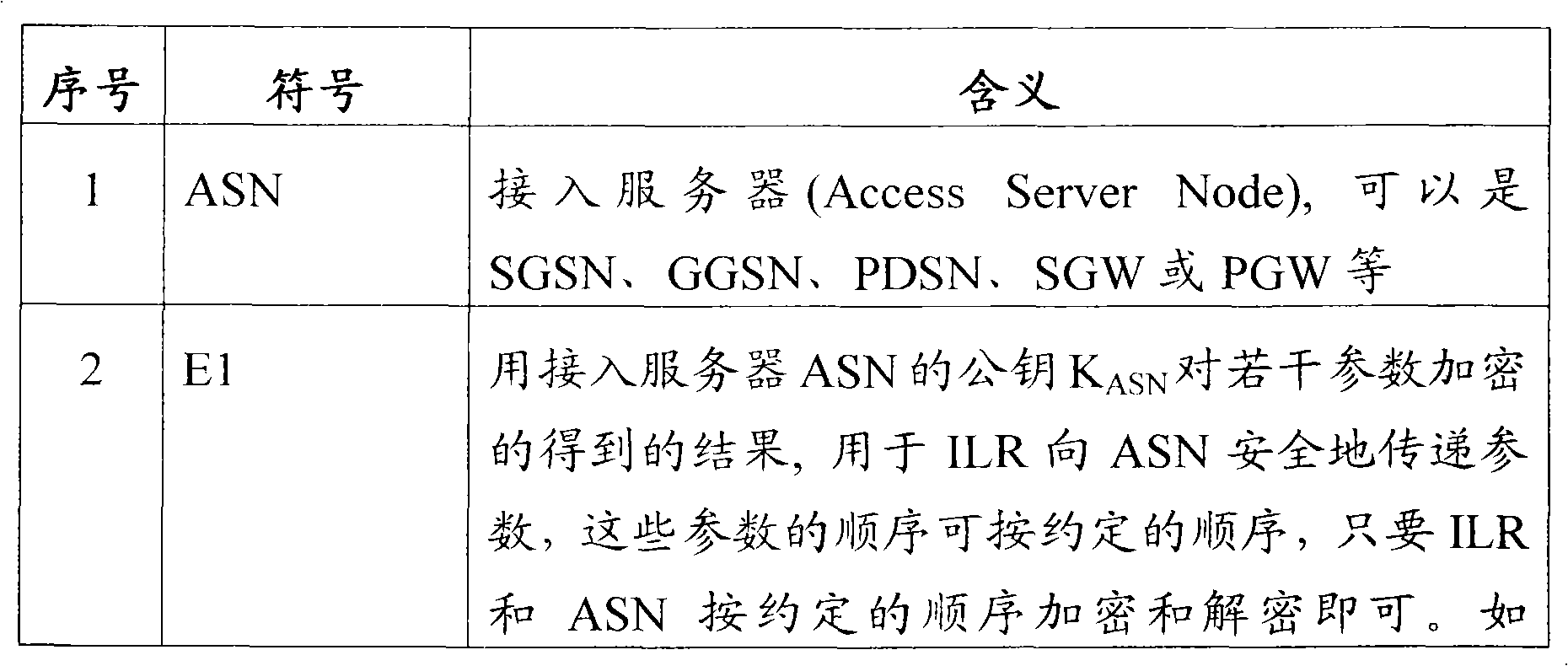
[0074] When the UE accesses the network, it must first pass the authentication of the Access Service Node (ASN: Access Service Node). Since the mobile user UE often roams from one access point to another, the ASN and The identity location register (ILR Identity Location Register, ILR) that stores user identity information and location information is often not in the same place. When the two are located in different areas and are interconnected through IP networks or other data networks, background technology figure 1 The man-in-the-middle attack described in .
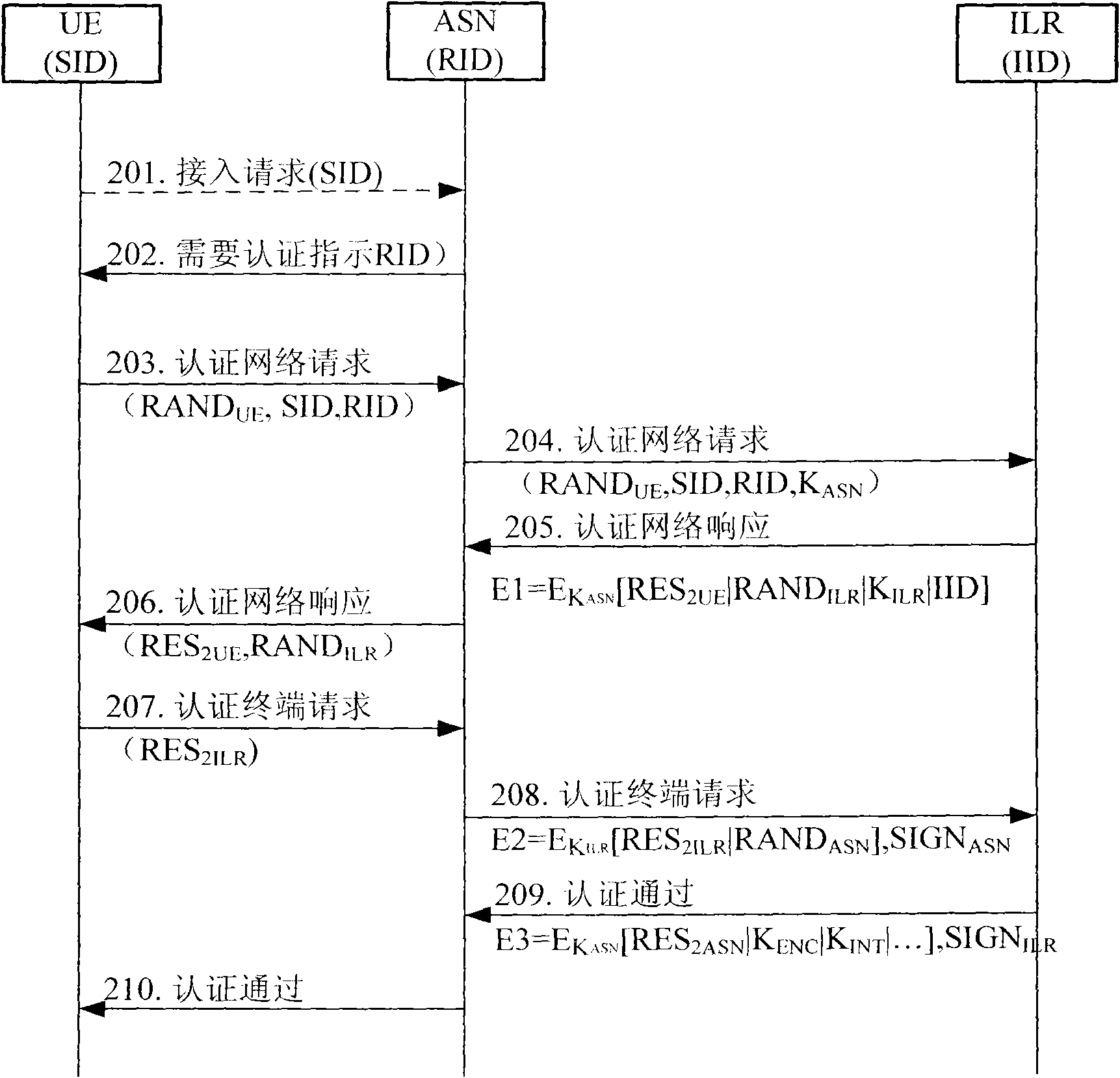
[0075] The authentication method described in this embodiment at least includes authentication of the UE by the ILR, and may further include authentication of the ILR by the UE and authentication of the ILR by the ASN.
[0076] Among them, the ILR authentication of the UE can ensure t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com