Method and device for realizing internet lawful interception
A technology for legal monitoring and monitoring management, applied in the field of network communication information security, can solve problems such as difficulty in being timely and effective, and achieve the effect of reducing security management costs, reducing security risks, and realizing centralized management
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
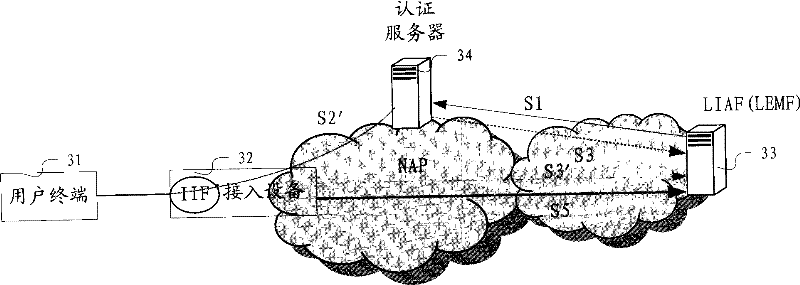
[0030] Figure 3A It is the first embodiment of the IP network lawful interception system structure provided by the present invention. It includes a user terminal 31, a network access device 32, an authentication server 34, and a lawful interception facility 33 (specifically, it may include a lawful interception management device LIAF and a law enforcement monitoring device LEMF). Among them, the user terminal 31 is controlled by the user as a related device used by the user to communicate; the network access device 32 is used to connect the user terminal and the connection device leading to other networks, which is provided by the network access provider Provided by (NAP), it is directly connected to the user terminal. According to the technology and configuration it adopts, through its internal internal monitoring function (IIF), data ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com