Self-modifying code identification method based on hardware emulator
An identification method and simulator technology, applied in the field of self-modifying code identification based on hardware simulators, can solve the problems of static analysis method analysis capability constraints, static binary representation inconsistency, static analysis powerlessness, etc., to resist detection and improve transparency. , the effect of improving analysis efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The technical content of the present invention will be further described below in conjunction with the accompanying drawings.
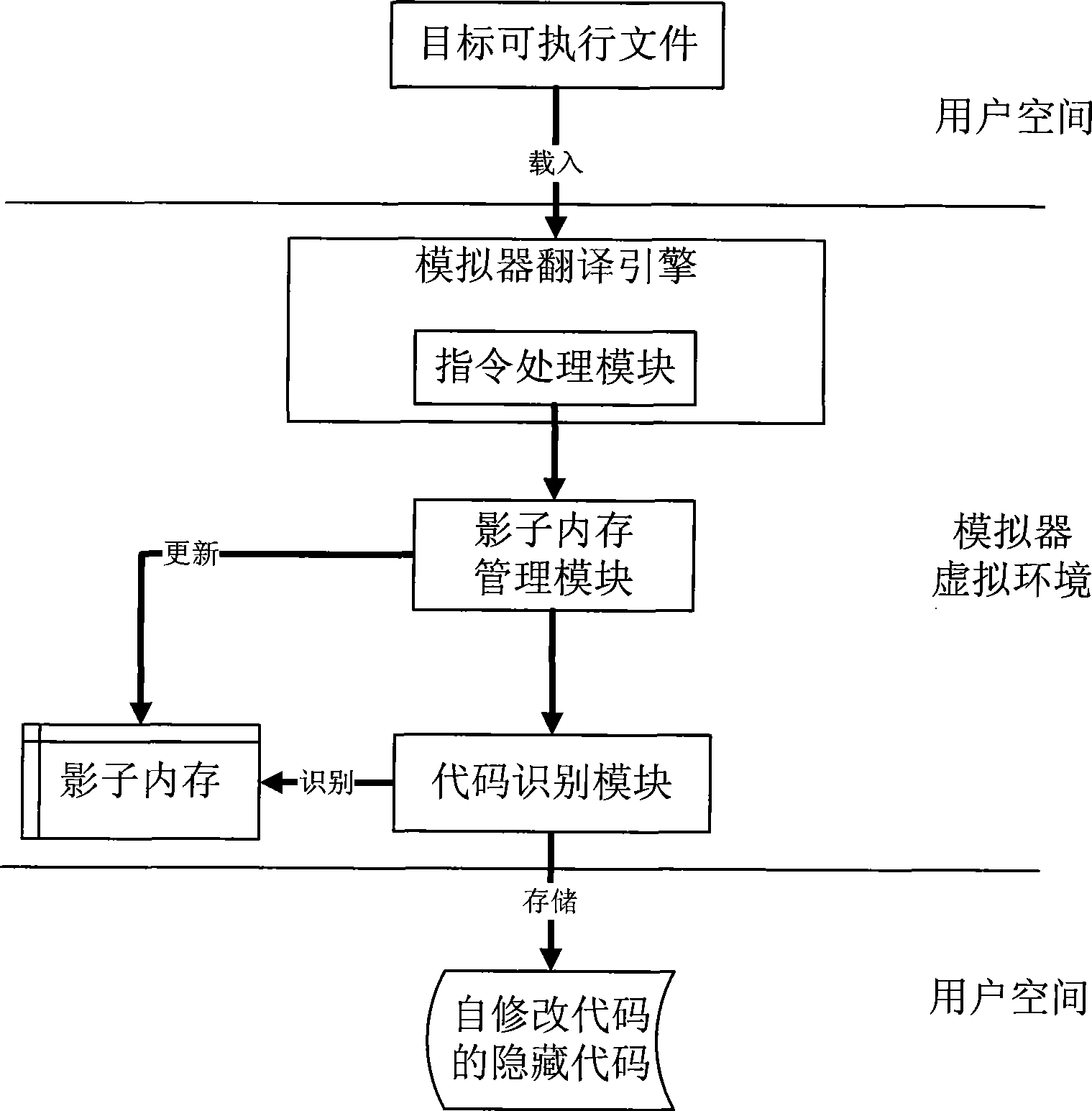
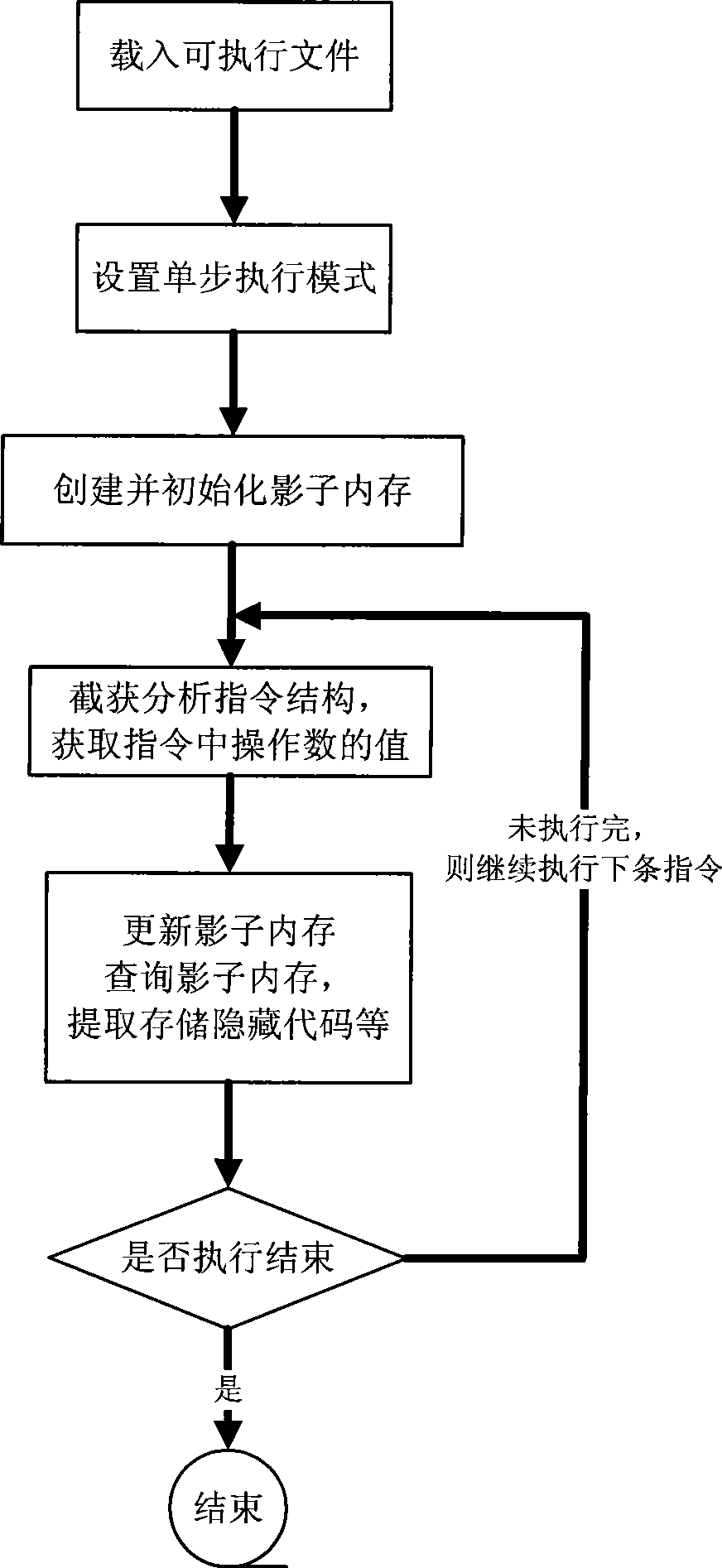
[0027] refer to figure 1 , the present invention expands the translation code block of the hardware simulator system into a cache area of the translation code block, and adds a shadow memory in the hardware simulator; when the program is running, intercepts the virtual system command to obtain the data information of the analysis target. Perform dynamic analysis on executable files in the modified hardware simulator, and identify and extract codes that are dynamically released into memory and executed during program execution by monitoring information such as memory write operations and control transfer instructions during program execution. Finally, using the control jump and other information obtained during the dynamic analysis process, the extracted code is restored to the original executable file, and a complete binary file with the same...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com