Secret key generation method
A technology for generating method and key, applied in public key and key distribution of secure communication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] The implementation of this program is as follows:
[0032] The key distribution center first generates an n×n symmetric matrix M, and protects this matrix as a secret, which must not be leaked;
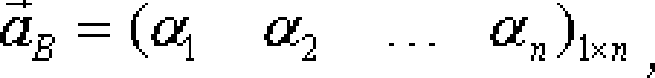
[0033] The key distribution center assigns a vector to each application object α → = α 1 α 2 . . . α n 1 × n , as the public key or ID of the object;
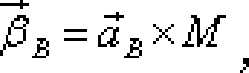
[0034] The key distribution center will Operate with the secret matrix M to generate the private key of t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com