Mobile terminal information resource safety security control and realizing method
A mobile terminal and security technology, applied in the field of communication, can solve the problem of no consideration, reduce the loss of information loss and leakage, and achieve the effect of destruction
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] The present invention will be further introduced below in conjunction with the accompanying drawings and specific embodiments, but not as a limitation of the present invention.
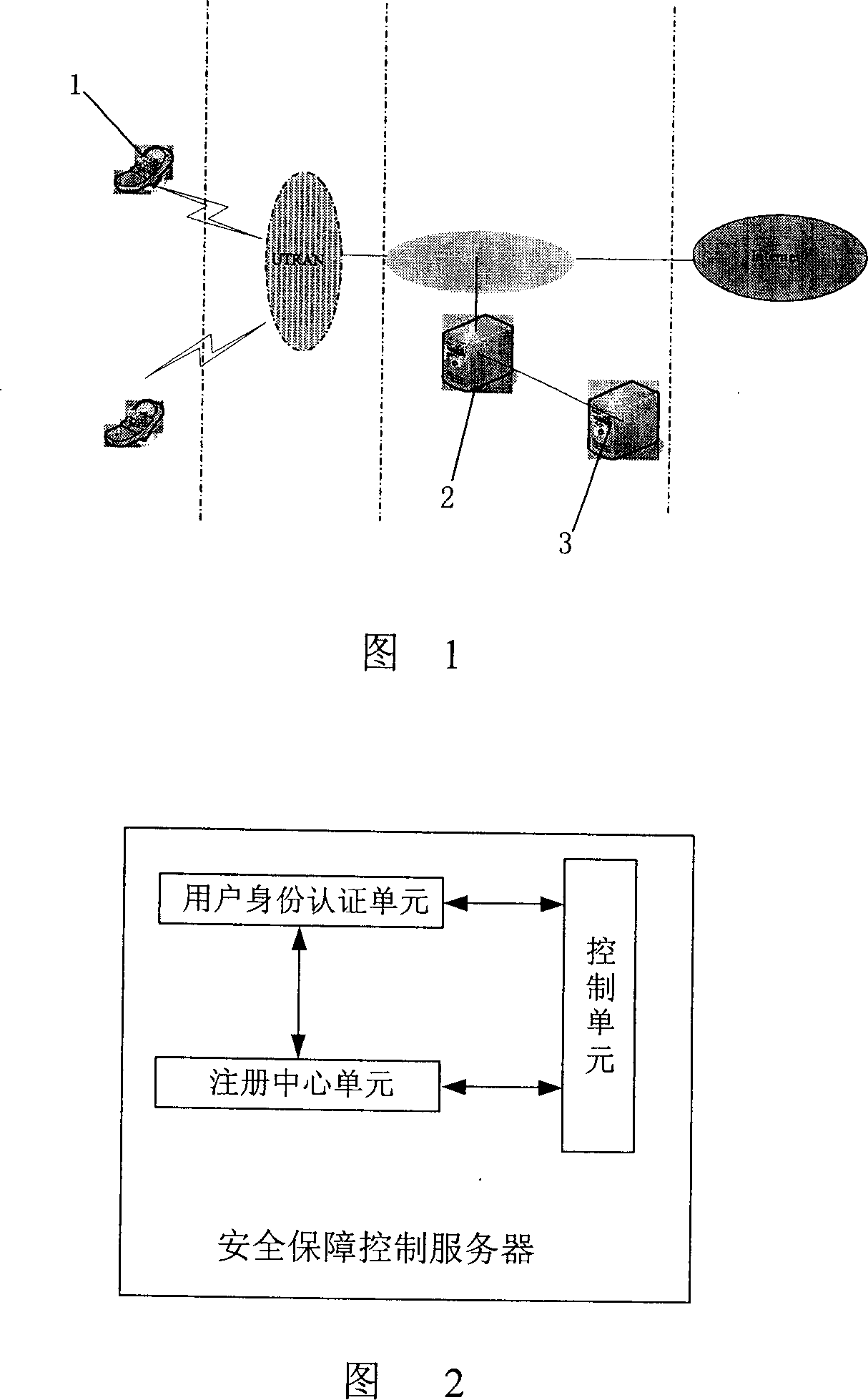
[0032] A mobile terminal information resource security assurance system, comprising a mobile terminal 1, a security assurance control server 2 (Information Assurance Control Server: IACS) and a network side database 3, wherein the security assurance control server 2 is directly connected to the network side database 3, and the mobile terminal 1 is connected to the security control server 2 through a wireless access network. The security assurance control server 2 can also be connected to an external network to realize mutual transmission of data.
[0033] Referring to Figure 2, the security control server 2 is the key to the entire system, and it includes: a user identity authentication unit, which provides confirmation of user ownership of information resources; a registration center unit, whi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com