Bit-level image encryption method based on composite Tent chaotic mapping
A technology of chaotic mapping and encryption method, which is applied in image data processing, image data processing, usage of multiple keys/algorithms, etc. It can solve the problem that the algorithm cannot effectively resist brute force attacks, the randomness of the key sequence is low, and the mapping distribution is uneven and other issues to achieve the effect of improving the ability to resist differential attacks, increasing complexity, and expanding the key space
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
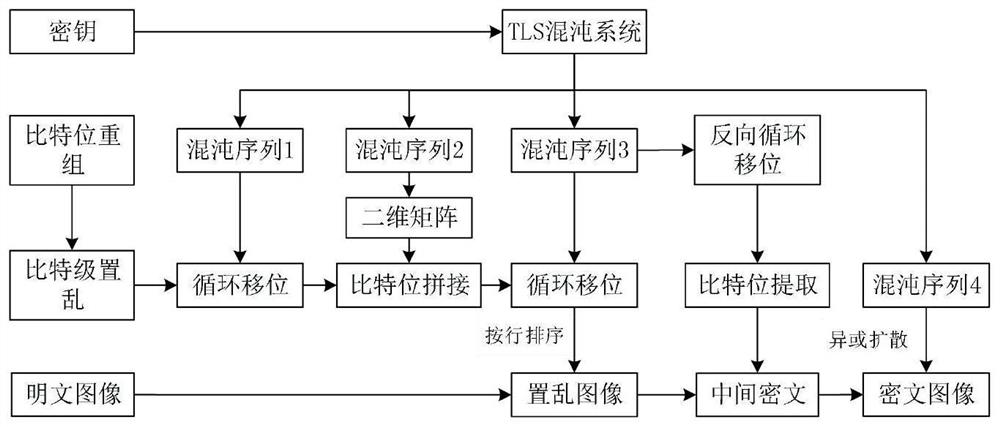
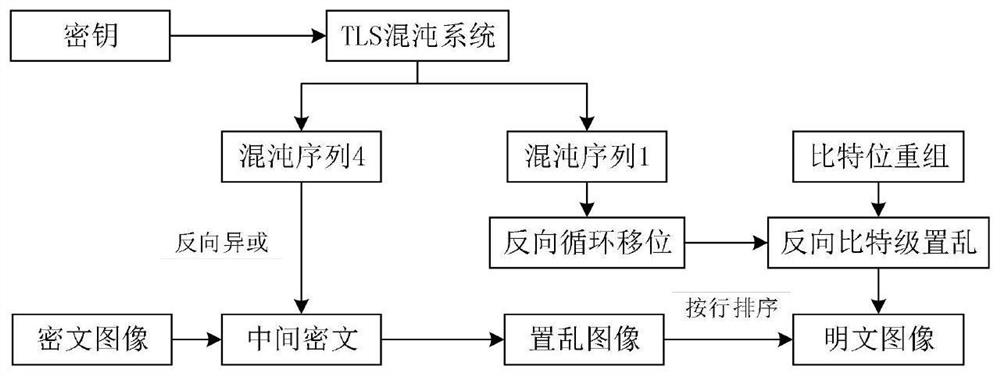
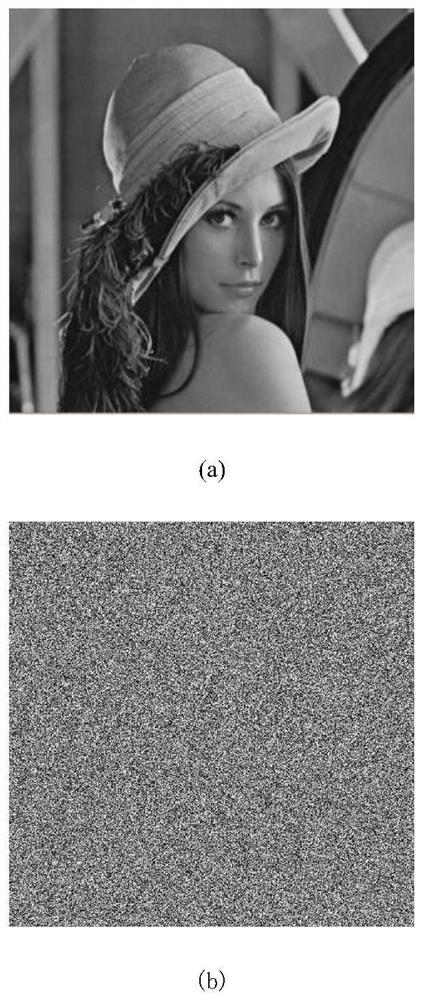
[0049] The invention will be further described below in conjunction with the accompanying drawings and specific implementation examples. The purpose of the present invention is to solve the problems of low randomness of the key sequence generated by the traditional chaotic map, small key space and limitation of bit scrambling. First, the Tent map is coupled with the Logistic map and the Sine map to obtain the composite chaotic map TLS, which increases the complexity of the chaotic system, enhances the randomness of the key sequence, and expands the parameter range of the chaotic system, thereby effectively improving the encryption system. security. And compared with the high-dimensional chaotic system, the execution cost of the one-dimensional chaotic system is lower. By introducing multiple composite chaotic systems in the encryption process to increase the number of keys, the key space of the algorithm is expanded, so that the algorithm can better resist brute force attacks...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com