Network threat intelligence text key information extraction method based on weak supervised learning
A key information, weakly supervised technology, applied in neural learning methods, biological neural network models, digital data information retrieval, etc. Qualitative indicators evaluate the effectiveness of screening schemes, improve interpretability and accuracy, and avoid potential errors
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0061] The present invention will be described in further detail below in conjunction with the accompanying drawings and specific implementation examples.
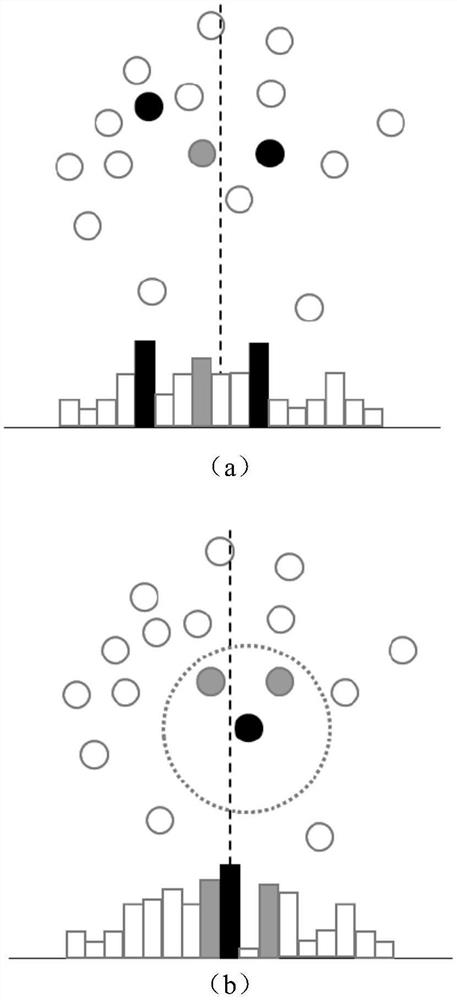
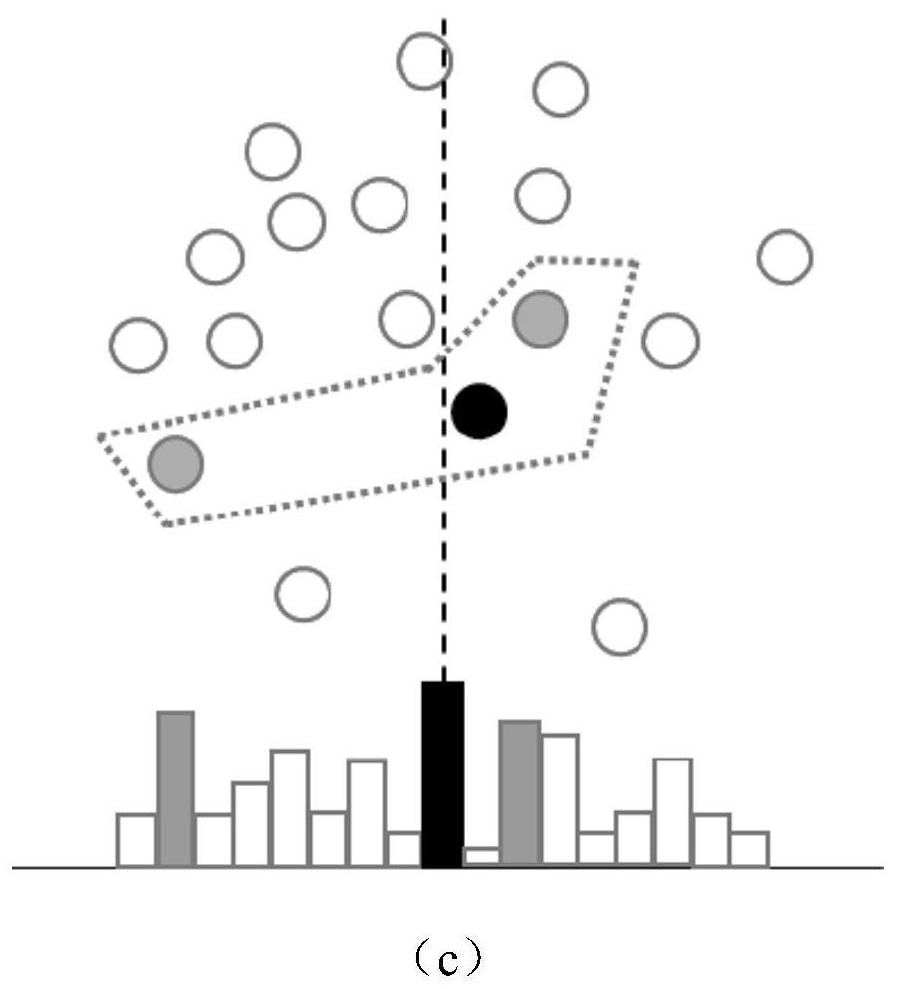
[0062] The system structure of the inventive method is as figure 1 As shown, the method consists of the text key information screening deep learning method SeqMask based on weakly supervised learning in S3 and the key information evaluation method in S4. The following specific implementation scenarios will take the application scenario of network threat intelligence technical and tactical analysis as an example.
[0063] Step S1: Preprocess the text information uploaded by web crawlers and users, clean the data and divide into sentences to form an analysis corpus; determine the text theme through the original storage environment, collection method, research field, etc. of the text, and form the sentence theme through screening and other methods Label.
[0064] Text preprocessing is based on information collection of cybe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com