A Flow-Based Tracing Attack Path Method in Network Shooting Range
A technology of attack path and flow, applied in the field of network shooting range, can solve the problem of lack of research on the overall model of directional network attack tracking and traceability, and achieve the effect of ensuring accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0055] The specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings.
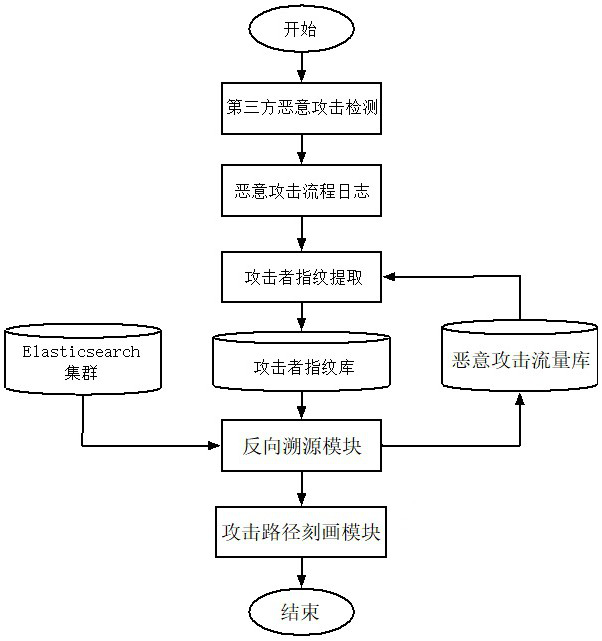
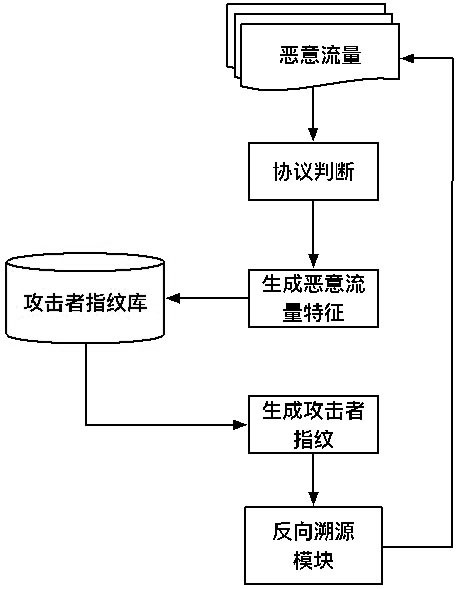
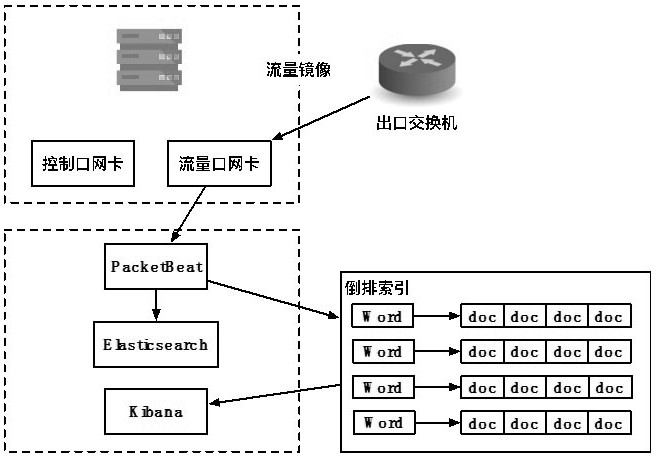
[0056] The present invention designs a traffic-based traceability attack path method in the network shooting range, which is used to describe the attack path of malicious traffic in the network shooting range. In practical applications, such as figure 1 As shown, the following steps A to I are performed in real time.
[0057] Step A. Monitor and collect all data traffic in the network shooting range, obtain each data traffic, form a traffic cluster, and mark the status of each data traffic as unprocessed, and then enter step B.
[0058] Step B. Perform malicious traffic detection for all data traffic in the traffic cluster, obtain each malicious traffic therein, and then enter step C.
[0059] Step C. Randomly select a piece of malicious flow from the unprocessed malicious flow as the current malicious flow, and create ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com