Software vulnerability detection method and device based on graph convolution network
A convolutional network and software vulnerability technology, applied in computer security devices, instruments, electrical digital data processing, etc., can solve problems such as difficult to meet needs, and achieve the effect of improving detection efficiency and software quality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to make the objectives, technical solutions and advantages of the present invention clearer and more comprehensible, the present invention will be described in further detail below with reference to the accompanying drawings and technical solutions.
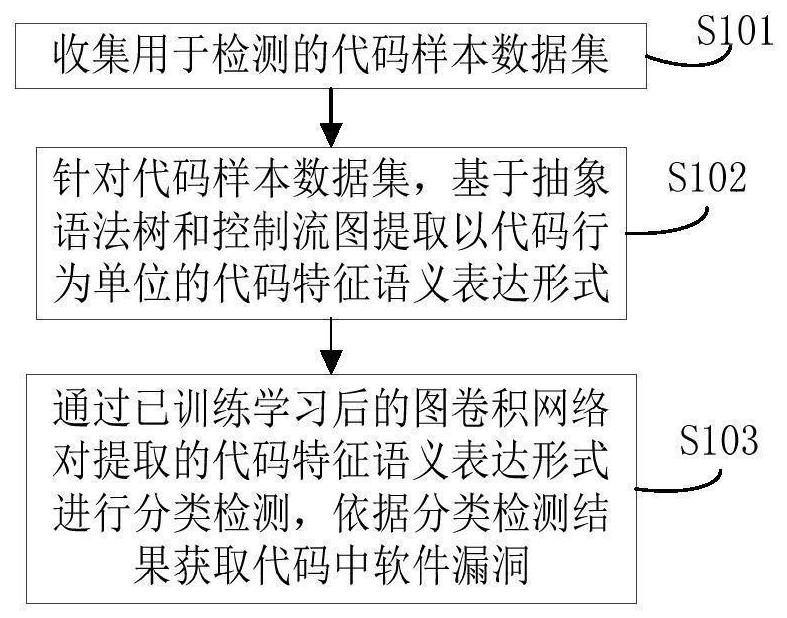
[0025] With the rapid development of the Internet, the scale of various online systems has been growing rapidly. However, at present, vulnerability mining is still mainly through manual analysis, which requires a lot of time, manpower, and in-depth understanding of software systems and technologies. Therefore, new methods are needed to assist vulnerability analysis to speed up the analysis. To this end, in the embodiments of the present invention, refer to figure 1 As shown, a software vulnerability detection method based on graph convolutional network is provided, which includes the following contents:
[0026] S101) collect a code sample data set for detection;
[0027] S102) for the code sample data set, base...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com