Authentication method and device, electronic equipment and storage medium
An electronic device and authentication technology, applied in secure communication devices, electrical components, user identity/authority verification, etc., can solve problems such as user privacy leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0149] In order to make the above objects, features and advantages of the present invention more comprehensible, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
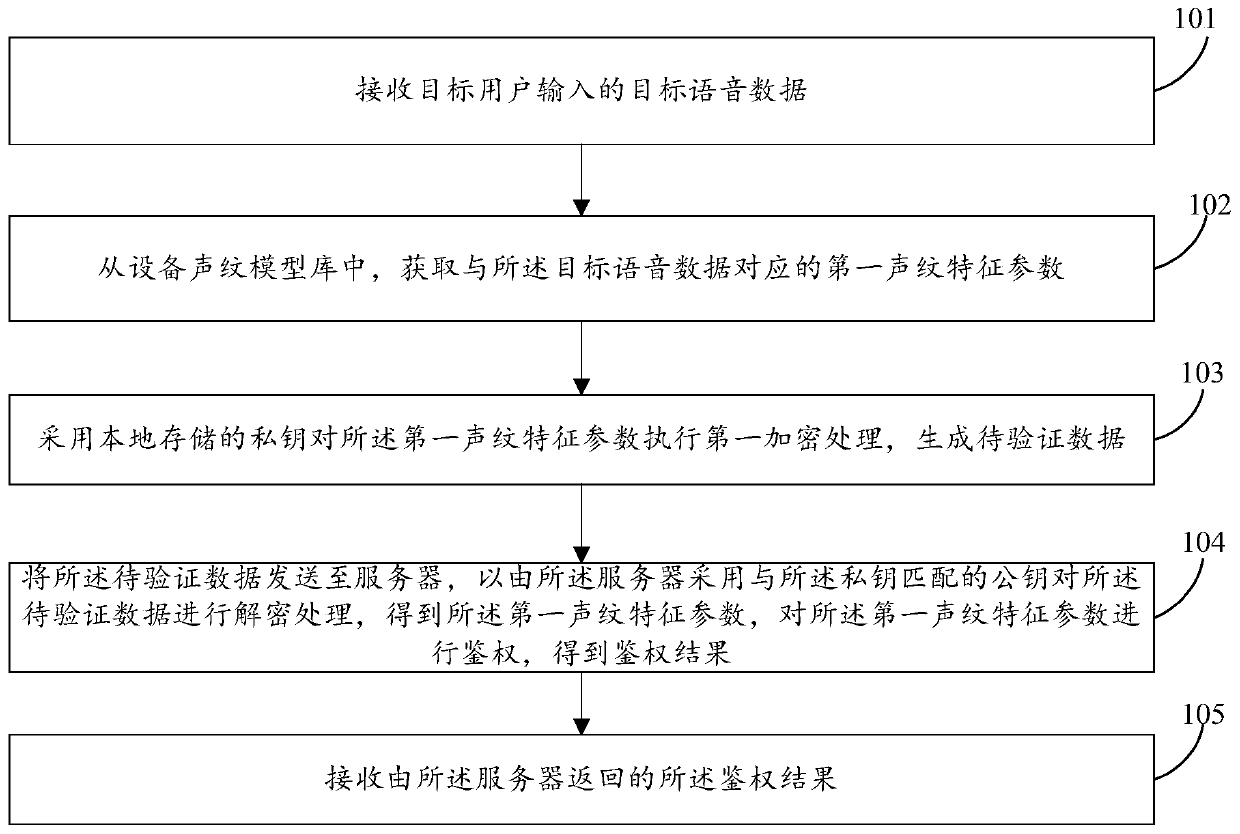
[0150] refer to figure 1 , which shows a flow chart of the steps of an authentication method provided by an embodiment of the present invention. The authentication method can be applied to electronic devices, and can specifically include the following steps:
[0151] Step 101: Receive target voice data input by a target user.
[0152] In the embodiment of the present invention, the electronic device can be a smart magic mirror device. The smart magic mirror device refers to adding a mirror display and human-mirror interaction functions to the mirror by embedding a display screen, a sensor, and an operating system in a traditional mirror. It has thus become the "fourth screen" besides computers, TVs, mobile phones, etc.
[0153] ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com