Multi-party secure computing method and device, electronic equipment
A computing method and security technology, applied in the field of distributed computing, which can solve the problems of malicious algorithm implementation, leakage of private data, incorrectness, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
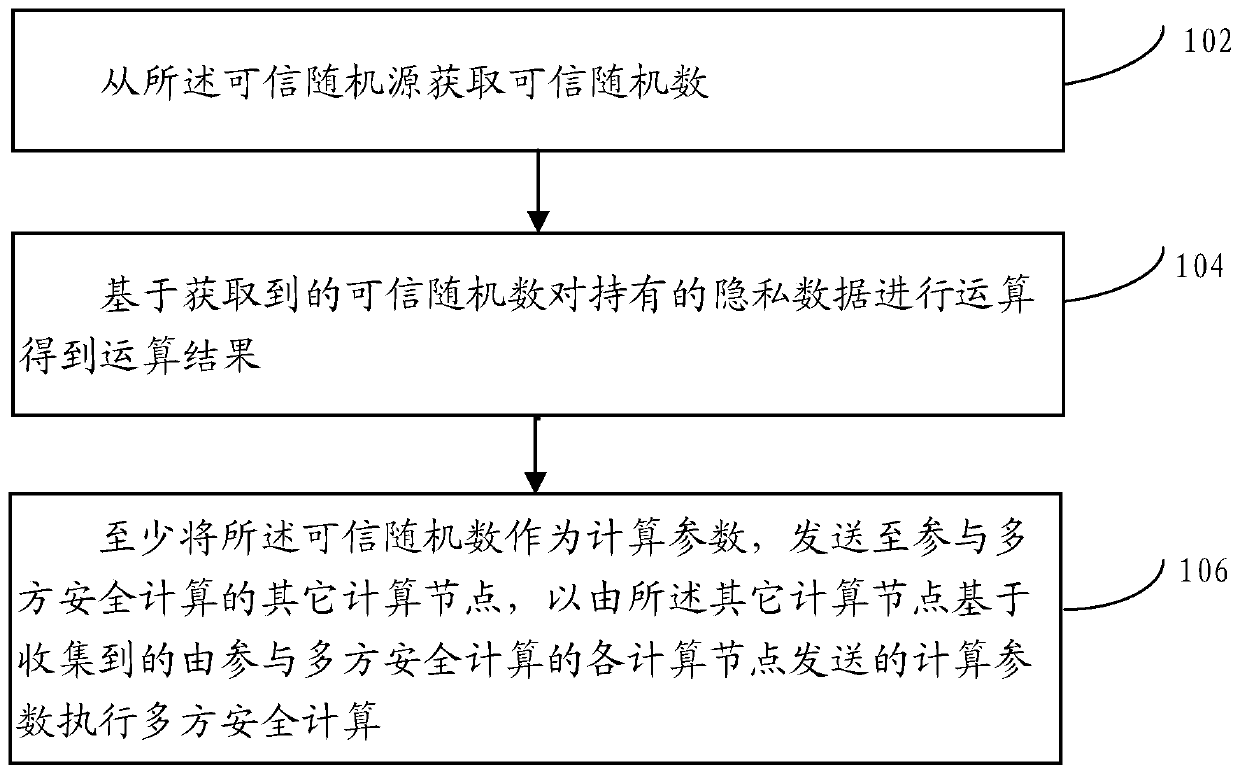
[0061] For computing nodes equipped with multi-party secure computing algorithms such as secret sharing and obfuscated circuits, one or more random numbers are usually generated based on the carried random algorithm, and the generated random numbers are used to calculate the private data held to obtain the budget As a result, the generated random number and the above-mentioned calculation results are then used as calculation parameters and transmitted to other calculation nodes participating in the multi-party secure calculation.
[0062] In practical applications, malicious multi-party security algorithms may use private data held by computing nodes participating in multi-party security calculations to construct pseudo-random numbers, and then use the pseudo-random numbers and The calculation results obtained by calculating the private data of the private data are transmitted to other computing nodes participating in the multi-party security calculation; furthermore, in this w...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com