Data exception detection system and method
A data anomaly and detection method technology, applied in the field of big data processing, can solve the problems of slow speed and low accuracy, and achieve the effect of high speed, high accuracy and absolute safety.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0042] see figure 1 , the present invention provides a data anomaly detection method, the data anomaly detection method comprises the following steps:
[0043] 1) Preprocessing the original data to remove the interference value in the original data, and filling the data after removing the interference value;
[0044] 2) Normalize the filled data;
[0045] 3) Shaping the normalized data to obtain supervised data;
[0046] 4) Using LSTM network to analyze the supervised data to obtain prediction data;
[0047] 5) Comparing the predicted data with the real data to determine whether the original data is abnormal.
[0048] In step 1), see figure 1 In the S1 step, the original data is preprocessed to remove the interference value in the original data, and the data after the removal of the interference value is filled.
[0049] As an example, the raw data includes low-dimensional flight data of the aircraft.
[0050] As an example, the raw data may include a data sequence of se...
Embodiment 2
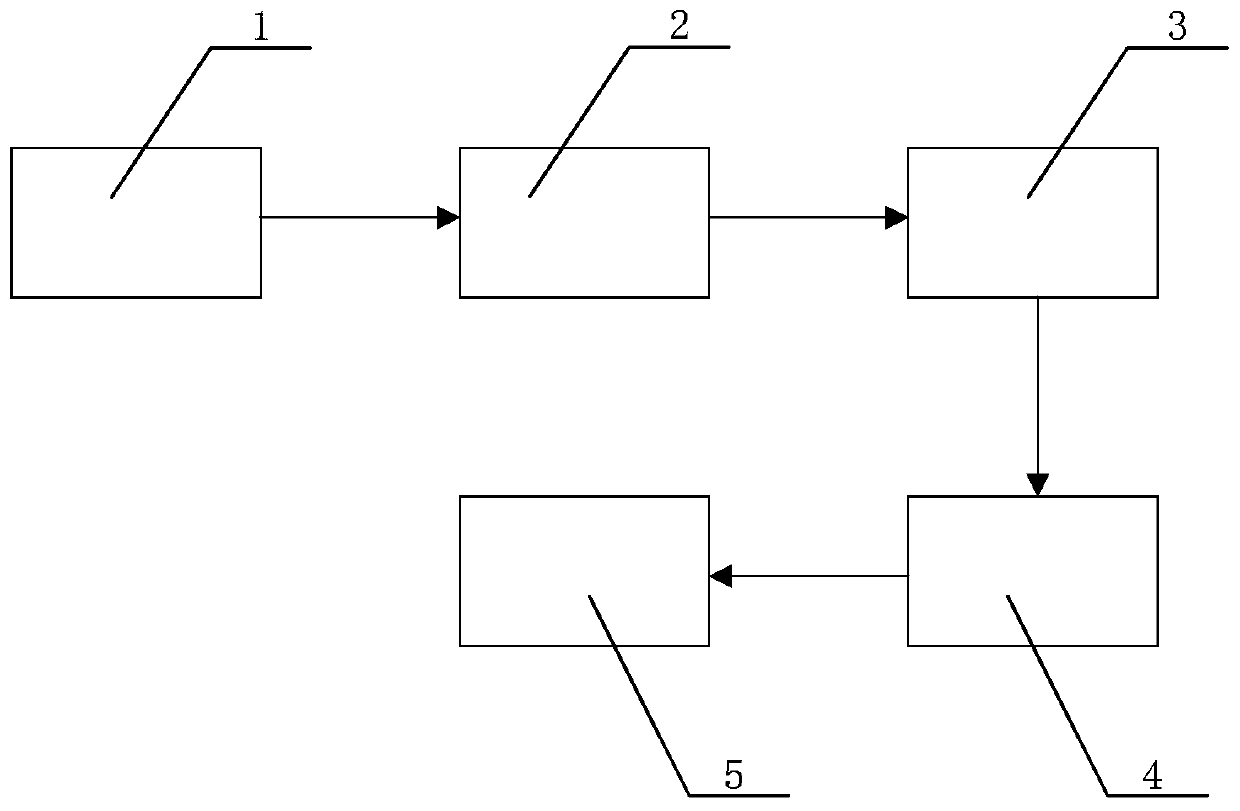
[0073] see figure 2 , the present invention also provides a data anomaly detection system, the data anomaly detection system includes: a preprocessing module 1, the preprocessing module 1 is used to preprocess the original data, to remove the interference value in the original data , and fill the data after removing the interference value; a normalization processing module 2, the normalization processing module 2 is connected with the preprocessing module 1, and the normalization processing module 2 is used for The filled data is normalized; the shaping processing module 3 is connected to the normalizing processing module 2, and the shaping processing module 3 is used for normalizing the data after the normalizing processing Shaping to obtain supervised data; an analysis module 4, the analysis module 4 is connected to the shaping processing module 3, and the analysis module 4 is used to analyze the supervised data using an LSTM network to obtain Predicted data; comparison ju...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com