Query track privacy protection method
A privacy protection and trajectory technology, applied in security devices, electrical components, transmission systems, etc., can solve the dilemma of privacy risk and service quality, and achieve the effect of reducing the number of queries, ensuring service quality, and solving conflicting problems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] Such as figure 1 Or shown in 2, a kind of query track privacy protection method of the present invention, it comprises the following steps:
[0037] Step 1. The location server grids the map of the city, calculates the service similarity of each adjacent grid, and merges the adjacent grids with a service similarity of 1 into the same area to generate a similar map;
[0038] Further, step 1 specifically includes the following steps:
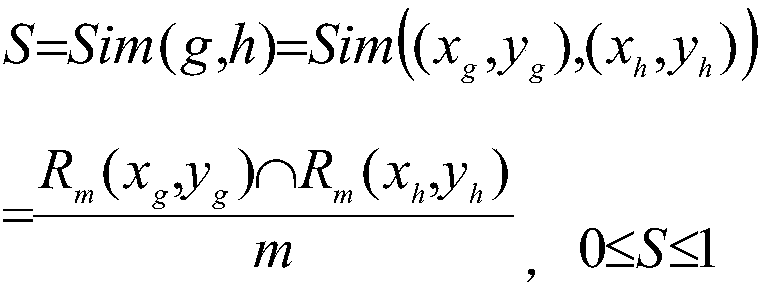
[0039]Step 1-1, the location server grids the map of the city, and calculates the Euclidean distance between the center point of each grid and all points of interest; the location server has the coordinates of all points of interest, and the location server uses an algorithm to traverse the grid map , take the m interest points of the Euclidean distance between each grid and all interest points for comparison. Interest points are terms in geographic information systems, which generally refer to all geographical objects that can be abstract...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com