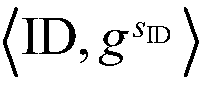
Confusable anonymous authentication method
An anonymous authentication and authentication key technology, applied in the field of anonymous authentication and confusion theory, cryptography, can solve the problem that the program is difficult to understand and analyze
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0237] Such as figure 2 As shown, the present embodiment applies the above method to a mobile intelligent group sensing system for searching for parking spaces. Users in the system first need to register their identity information with the system administrator, and legitimate users after registration can register with the server in the system. An anonymous authentication request is initiated, and the server provides the user with information about available parking spaces after authenticating the user's legitimacy. The anonymous authentication request ensures that the user's private information is not exposed, but if a user performs an illegal operation that does not comply with the system regulations, the tracker in the system can find the user's identity through the user's authentication request.
[0238] The specific steps of the application are as follows:
[0239] 1 The system administrator initializes the system (Setup)
[0240] 2 new members to register as a user
...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com