Vulnerability detection method and device, computer equipment and memory medium
A vulnerability detection and computer program technology, applied in the computer field, can solve the problems that the physical firewall does not have the ability to distinguish ports and applications, and cannot guarantee the security of application servers, so as to achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] In order to make the purpose, technical solution and advantages of the present application clearer, the present application will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present application, and are not intended to limit the present application.
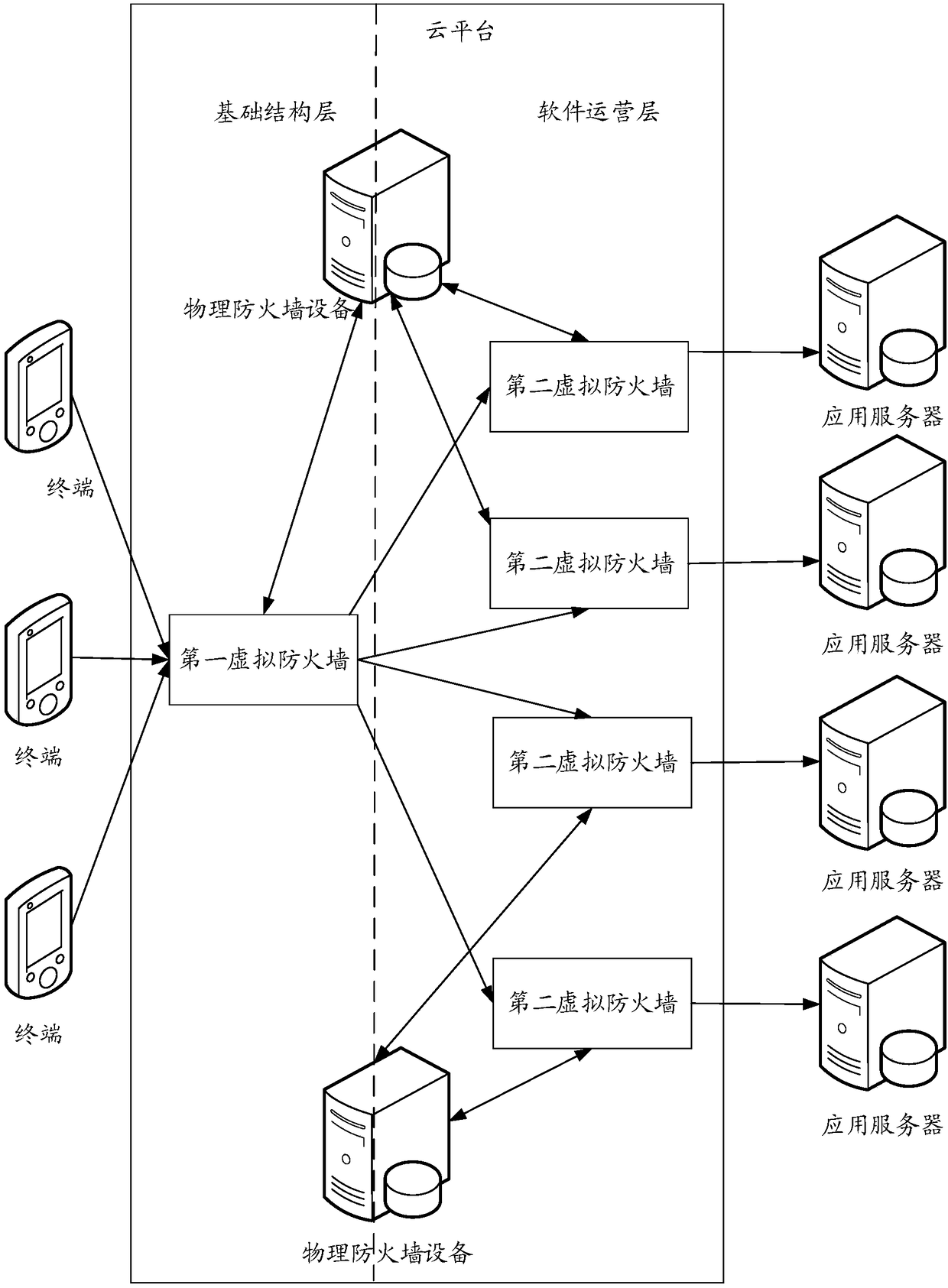
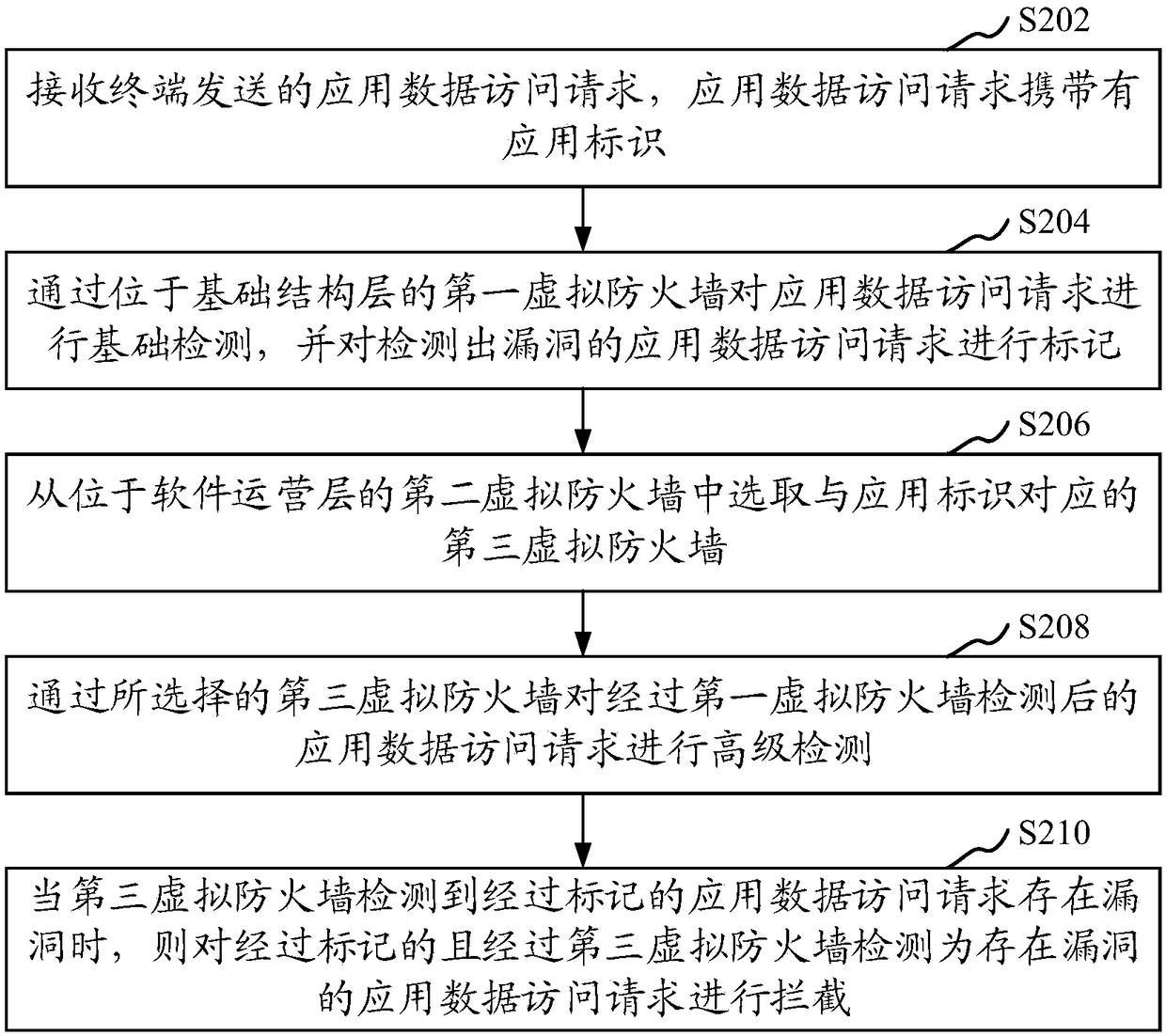
[0048] The vulnerability detection method provided by this application can be applied to such as figure 1 shown in the application environment. Among them, the cloud platform communicates with terminals and application servers through the network. The cloud platform can be configured through physical firewalls. For example, each physical firewall device is divided based on virtual resources to obtain multiple virtual firewall devices. Each virtual firewall device Corresponding to different application servers respectively, so as to realize the security guarantee for the d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com