Method and system for privacy protection of block chain transaction
A blockchain and transaction technology, applied in the security field of blockchain transaction privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
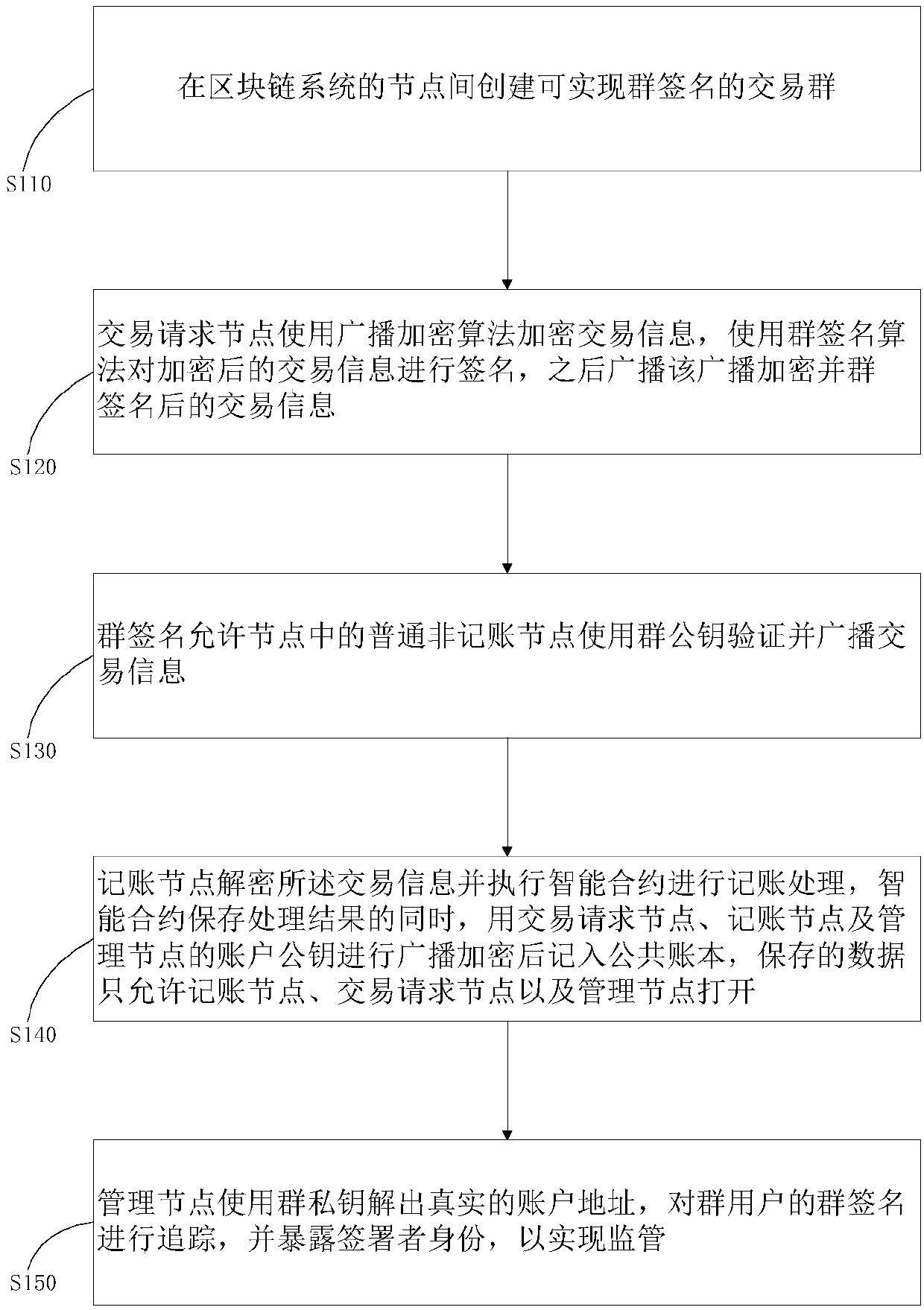
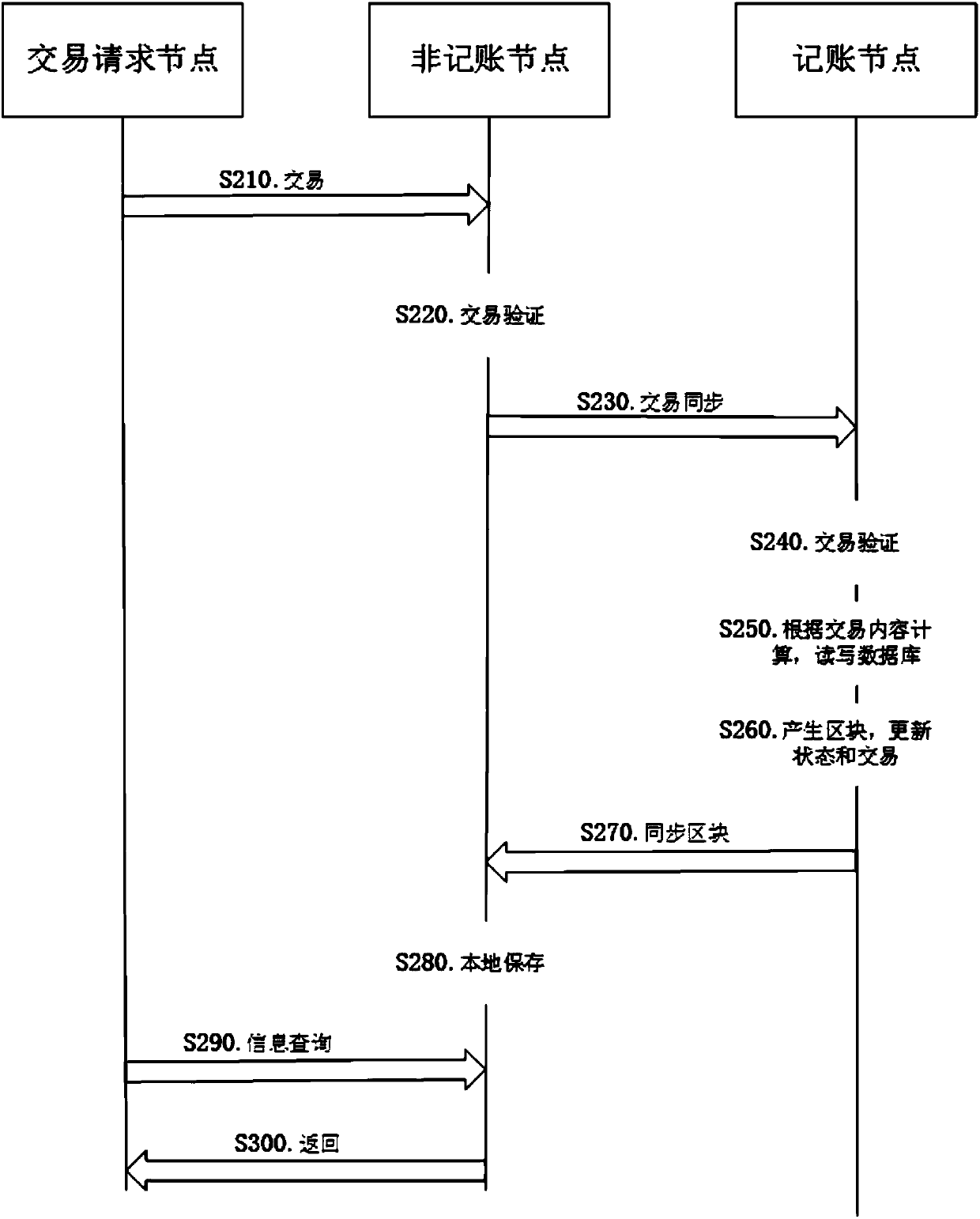
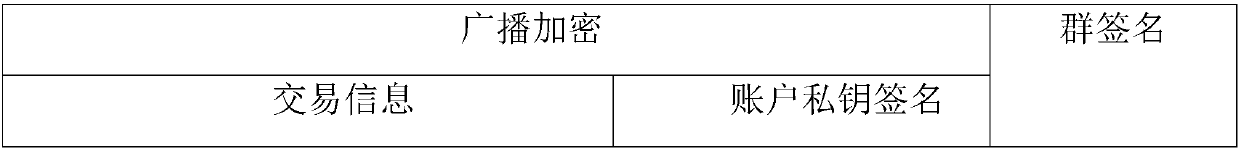
Method used
Image
Examples
Embodiment
[0061] In group signature, each user in the same group needs to have a public key, private key and group certificate. The group administrator also has the group private key. All related accounts are in the same group and managed by the group administrator.
[0062] (1) Account establishment: users can create accounts on the blockchain nodes, and the nodes automatically generate public-private key pairs and join the group. A specific example process is as follows:
[0063] A1: The user creates an account on the institution node;
[0064] A2: The node generates the account public-private key pair and prompts the user to enter the password;
[0065] A3: The node generates a public and private key file and saves it locally, and the private key file is encrypted with a password (password encryption is only one of the encryption algorithms);
[0066] A4: The node initiates an account creation application transaction, and the receiver is a built-in smart contract, which carries the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com