Intrusion-tolerant cloud storage data auditing method
A technology of data auditing and intrusion tolerance, applied in the field of cloud computing security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] It should be noted that the embodiments in the application and the features in the embodiments can be combined with each other if there is no conflict. Hereinafter, the present invention will be described in detail with reference to the drawings and in conjunction with the embodiments.
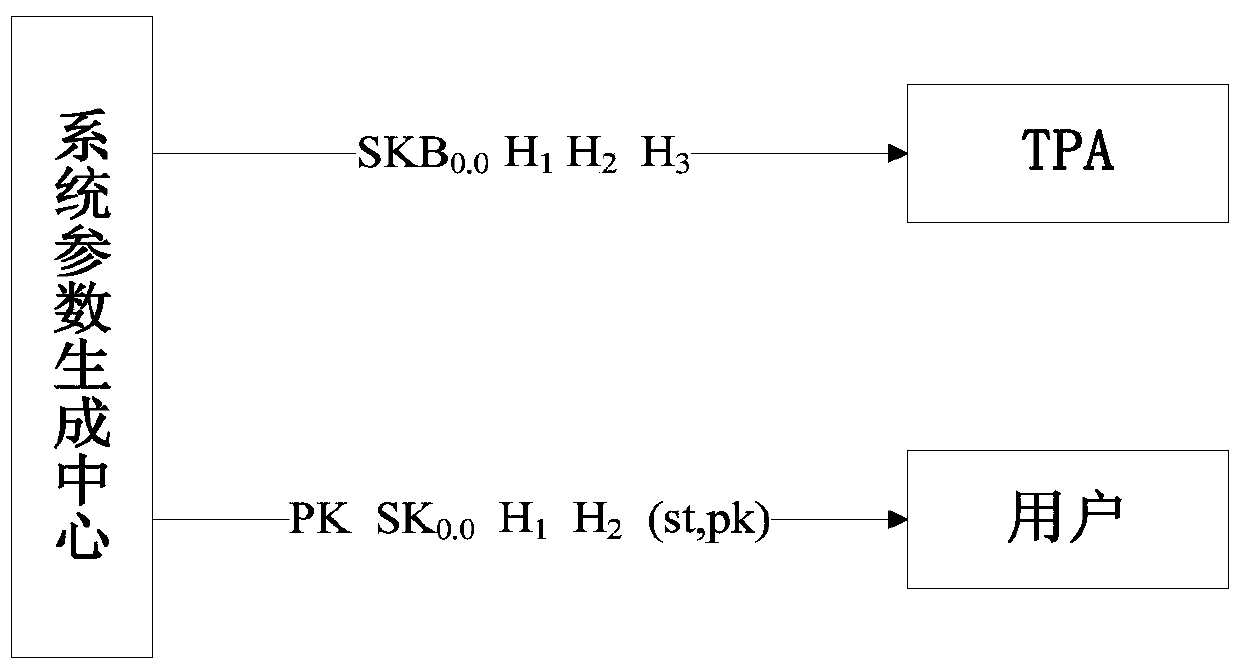
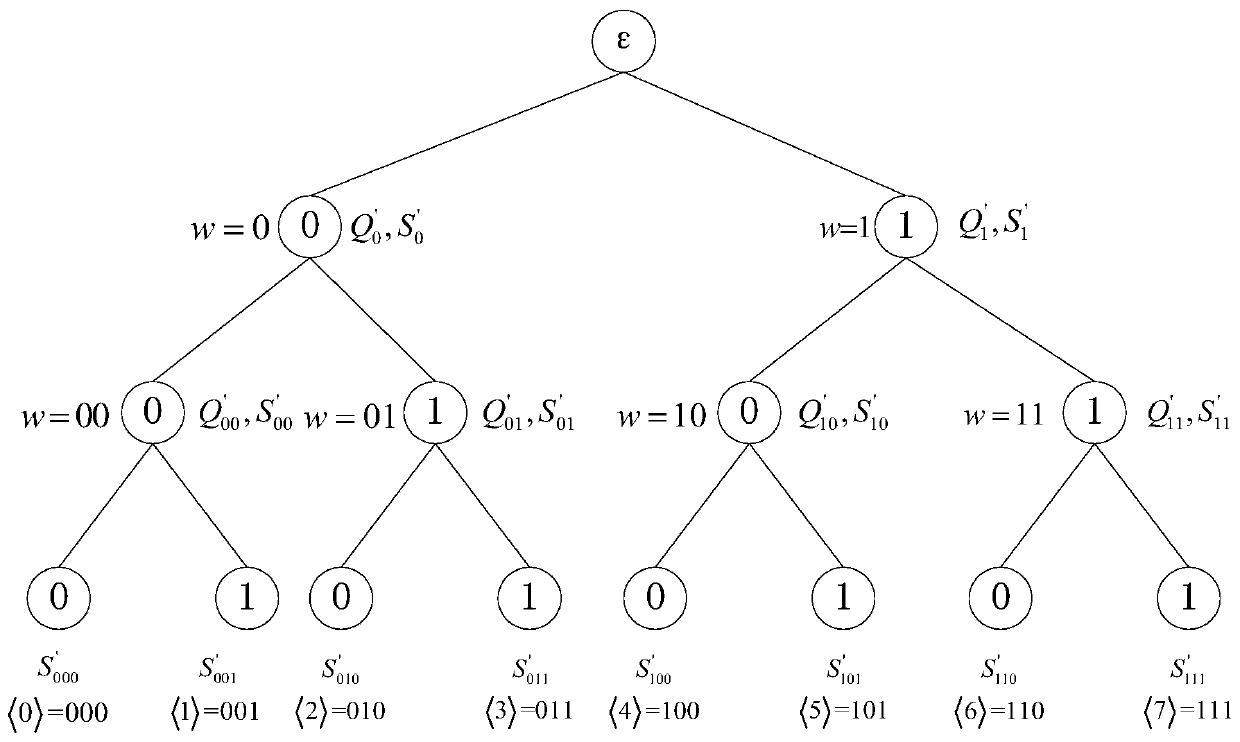
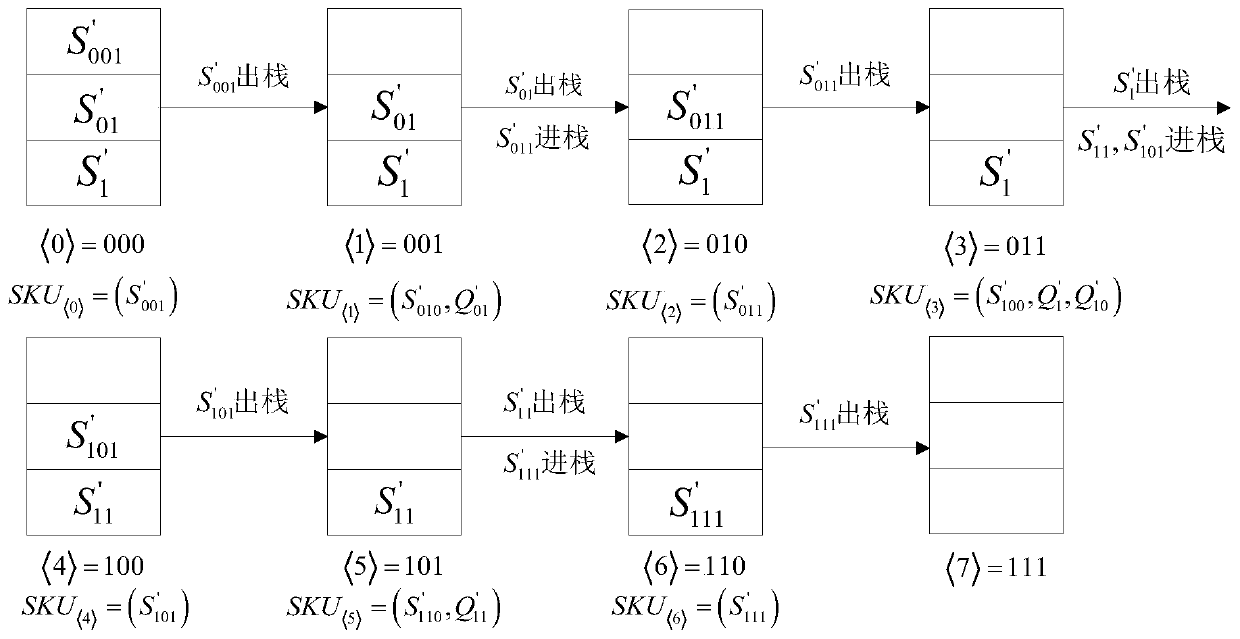
[0055] Such as figure 1 with Figure 8 As shown, the system members used in the intrusion-tolerant cloud storage data audit method provided by the present invention include system parameter generation centers, cloud servers, users, and third-party audits (TPA). The parameter generation center generates various parameters required for system operation, including user private keys, user public keys, etc.; cloud servers provide users with storage services; users upload a large number of data files to the cloud server for storage; third-party audits provide users with Audit service to check the integrity of the data on the cloud server stored by the user.
[0056] The following embodiments are...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com