Malicious code detection method, system and mobile terminal under Android system
一种恶意代码检测、安卓系统的技术,应用在恶意代码检测领域,达到提高检测精度、检测范围全面、消耗资源少的效果
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] In order to enable those skilled in the art to better understand the technical solutions in the embodiments of the present invention, and to make the above-mentioned purposes, features and advantages of the present invention more obvious and easy to understand, the technical solutions in the present invention will be further detailed below in conjunction with the accompanying drawings illustrate.
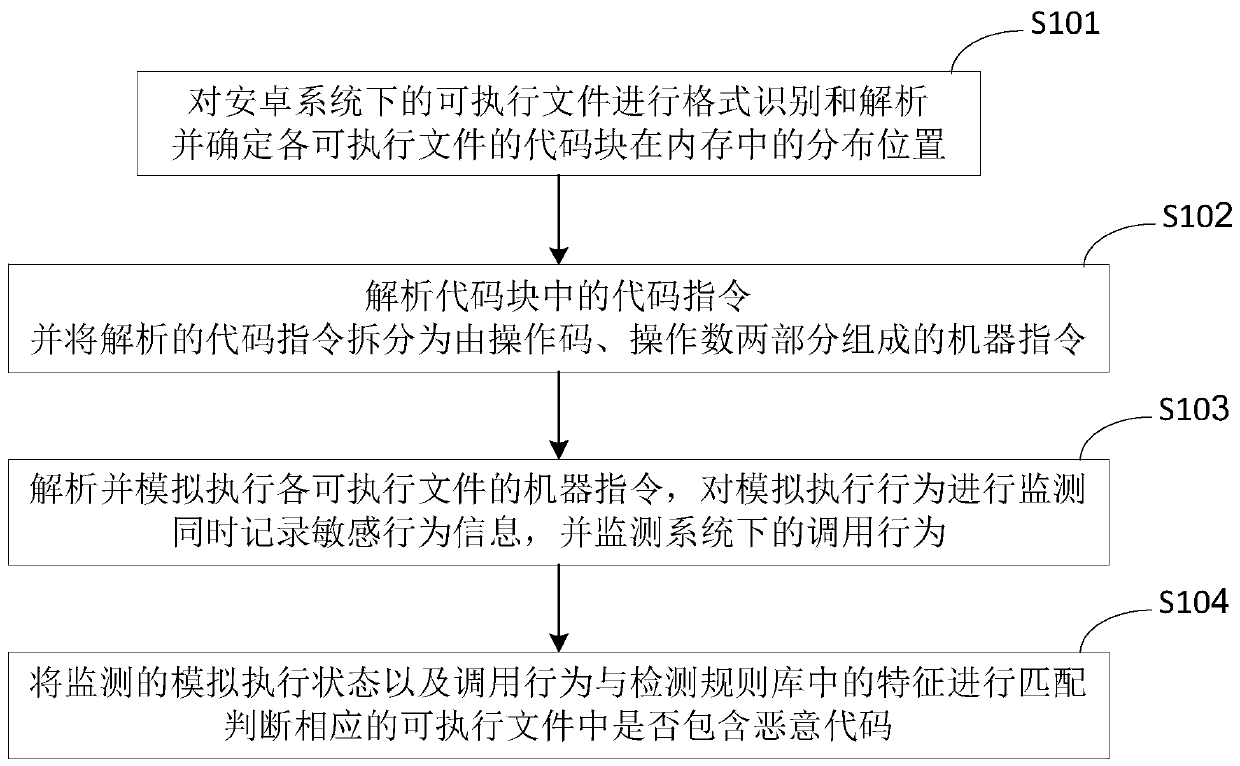
[0043] The present invention provides the method embodiment of the malicious code detection under Android system, as figure 1 shown, including:
[0044] S101: Perform format identification and analysis on executable files under the Android system, and determine the distribution position of the code blocks of each executable file in the memory. This process supports format identification and analysis of various executable files, including APK, DEX , ELF, OAT and other formats of executable files;
[0045] It can be understood that the format recognition and parsing of execut...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com