Method for encrypting white box password based on random permutation
A technology of random permutation and encryption method, which is applied in the field of information security, can solve problems such as solution breakthrough, low implementation efficiency, large memory space, etc., and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
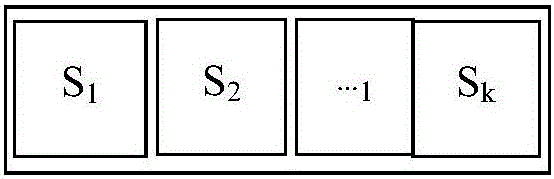
[0051] Layer S consists of multiple random permutations S 1 , S 2 ,...,S k Instead, go through a simple parallel permutation, such as image 3 As shown, here S 1 , S 2 ,...,S k be k randomly selected permutations, let their input length be t 1 , t 2 ,...,t k , here t 1 , t 2 ,...,t k Can be different. Assume that the input of the S layer is I, and I is divided into length t 1 , t 2 ,...,t k Divided into k blocks, the first block I 1 by S 1 Perform substitution to get the result O 1 ;Second block I 2 by S 2 Perform substitution to get the result O 2 , and so on, and finally concatenate the k results, O 1 ||O 2 ||...||O k That is the output of the S layer.
Embodiment 2
[0053] Layer S consists of multiple small random permutations S i The structure is completed through a variety of combinations, that is, the structure in the dotted line box shown in the figure below, and the S in the dotted line box i The combined structure is as follows Figure 4 Shown:
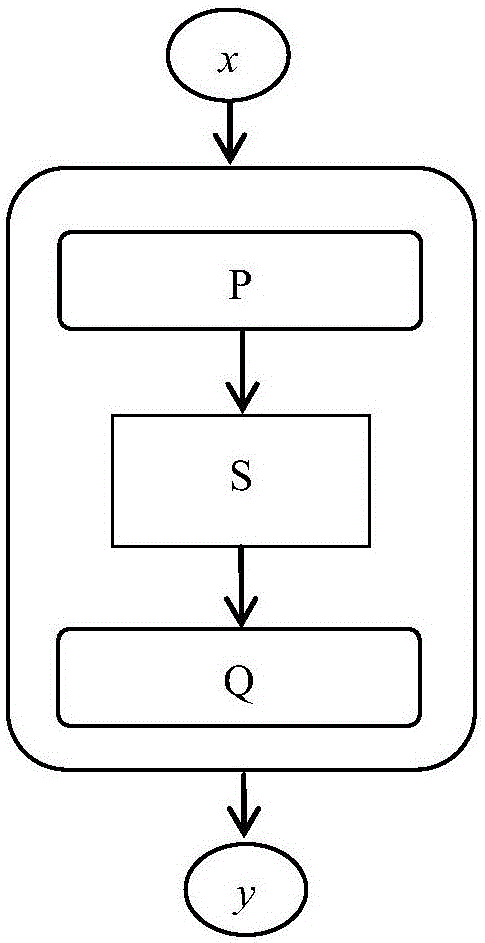
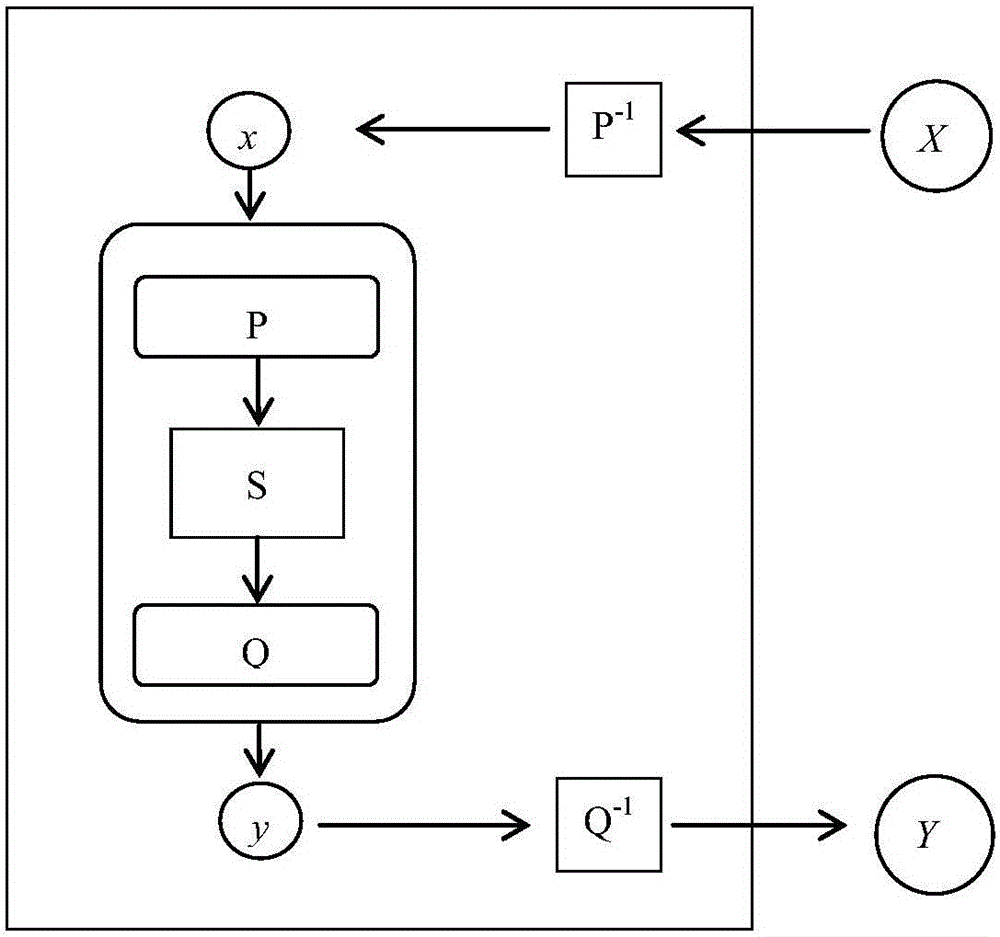
[0054] i) S i There can be multiple or only one. When S i When there is only one, then there are no multiple S i In the case of a composite construction, that is figure 1 basic structure.
[0055] ii) S i The operation of exchanging positions can be performed multiple times. That is to say, S 1 , S 2 ,...,S k The output of O=O 1 ||O 2 ||...||O k will act as S j1 , S j2 ,...,S jk input, here j 1 , j 2 ,...,j k is 1, 2,..., the full row of k; and S j1 , S j2 ,...,S jk The output of will in turn be used as S t1 , S t2 ,...,S tk input, where t 1 , t 2 ,...,t k is another full row of 1, 2, ..., k, and so on, S 1 , S 2 ,...,S k The position exchange of can be perfo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com