Cloud computing data security label management method and system
A security marking and data security technology, applied in transmission systems, electrical components, etc., can solve the problems of loss of data control, lack of security control, and inability to ensure the correct use of data, and achieve the effect of easy implementation and convenient expansion
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
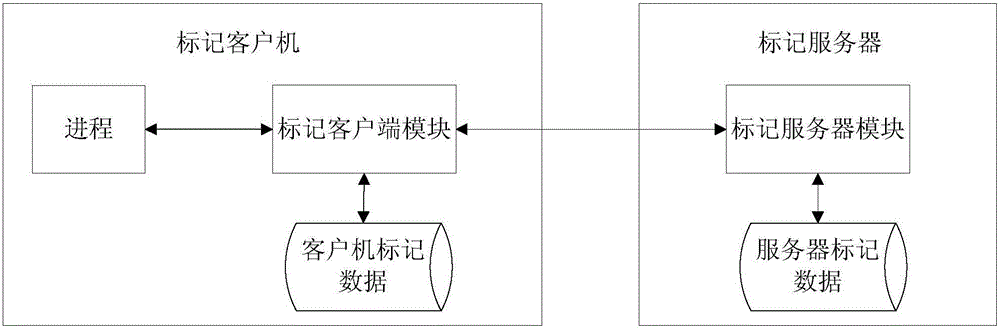
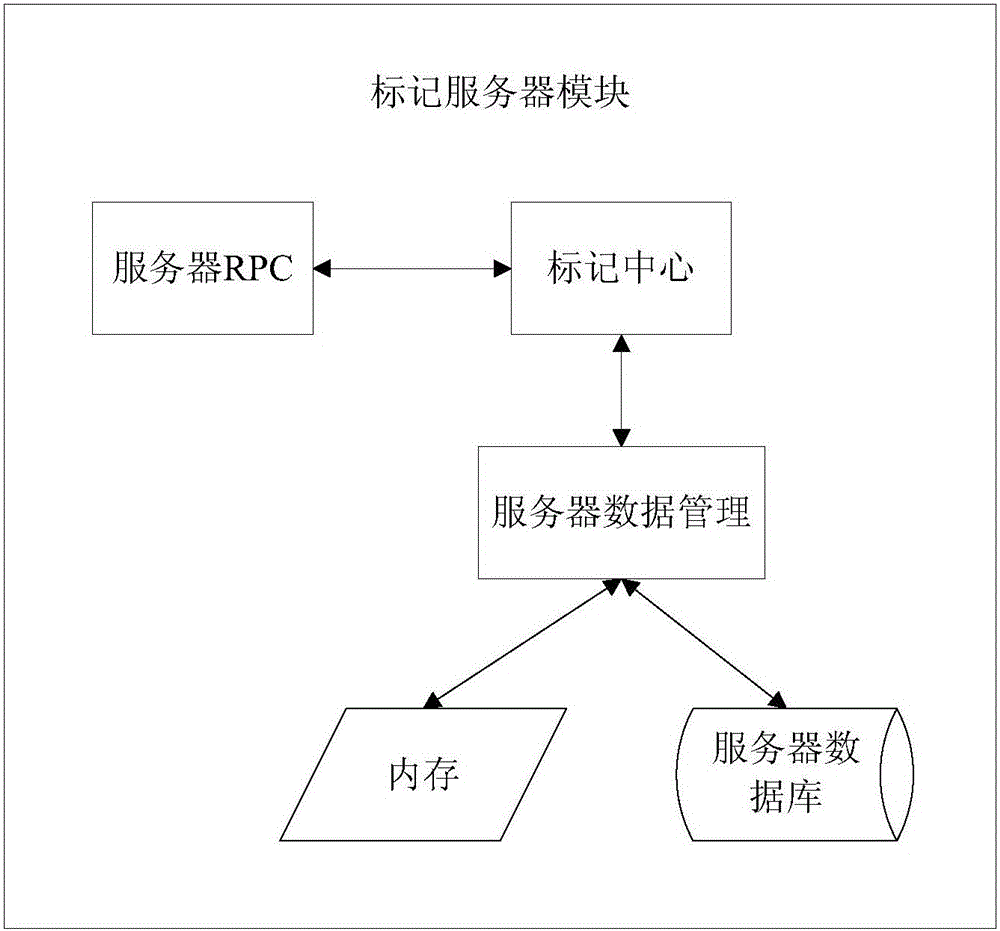
[0044] Aiming at the deficiencies in the prior art, the present invention proposes a cloud computing data security mark management method and system.
[0045] The following are the overall steps of the present invention, as follows:
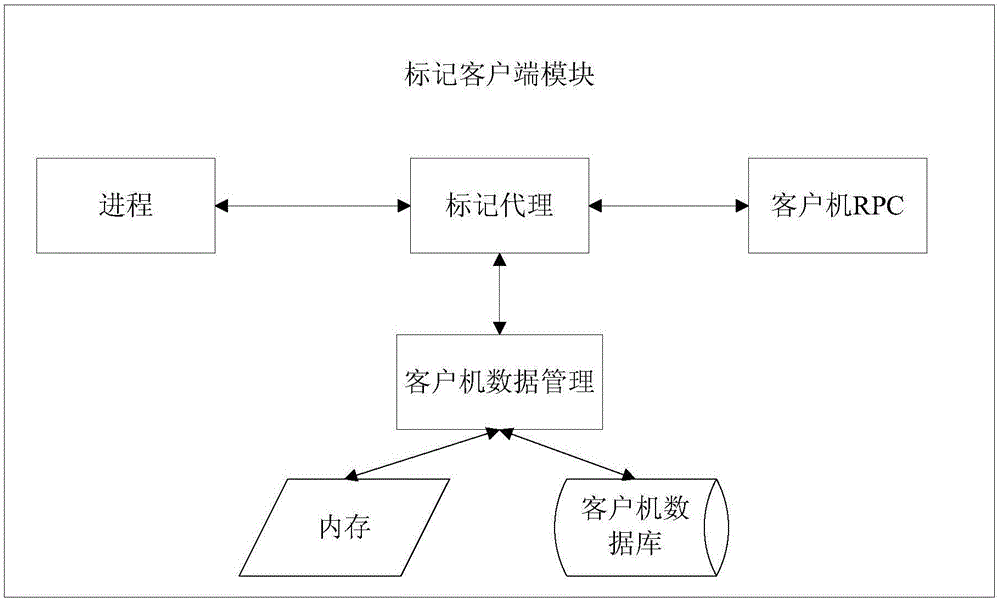
[0046] The method of the present invention efficiently processes marking operations under the cloud computing platform through a distributed storage-based method, including creation, retrieval, modification and deletion of marking data. Including the following steps:
[0047] Step 1: After receiving the marking operation request, the marking agent of the client verifies the legitimacy of the marking operation, and judges whether to respond or reject the request;
[0048] Step 2: If the response request is judged, the response method is determined according to the tag data and operation type of the operation;
[0049] Step 21: Use proxy response to process the operation request, including asynchronous response and synchronous response;
[0050]...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com