RBAC based malicious program interception and processing method in Android platform
A malicious program and malicious technology, applied in the field of malicious program interception and disposal based on RBAC, can solve the problems of user privacy security threats, low dependency intensity, need to be improved, etc., to protect user privacy, protect privacy security, and balance user experience. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
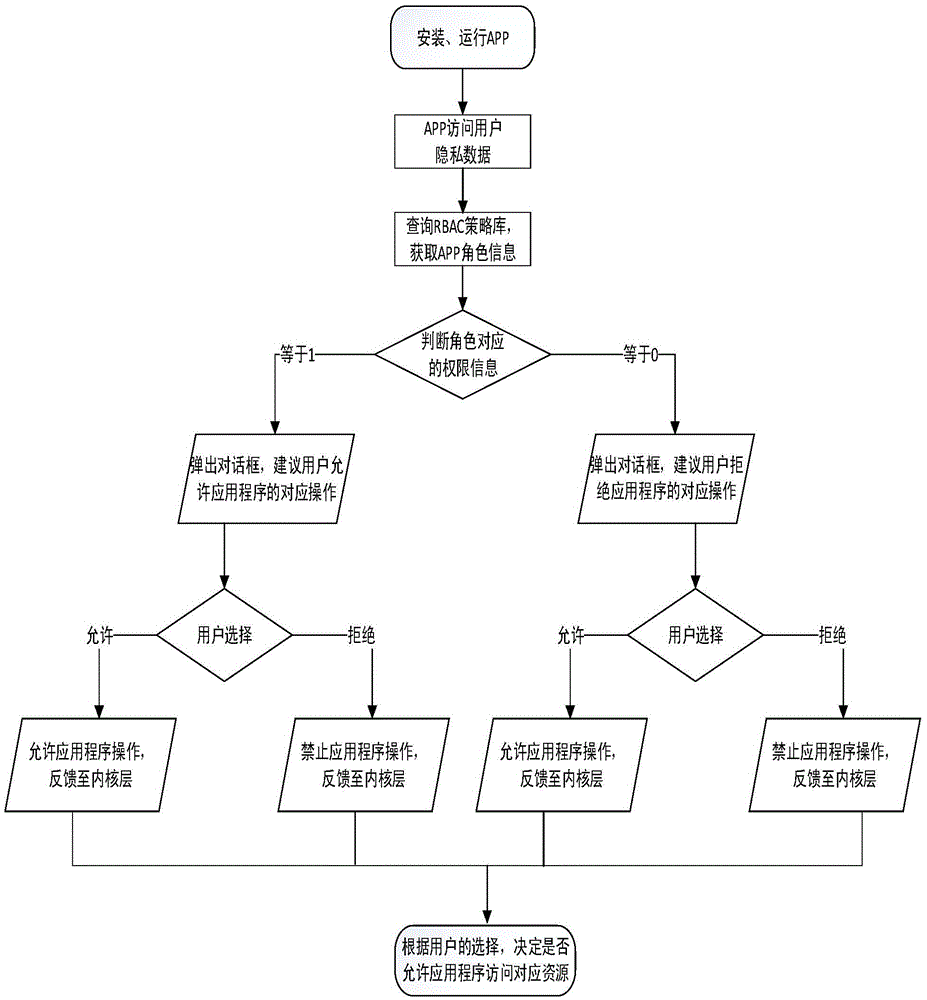
[0020] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
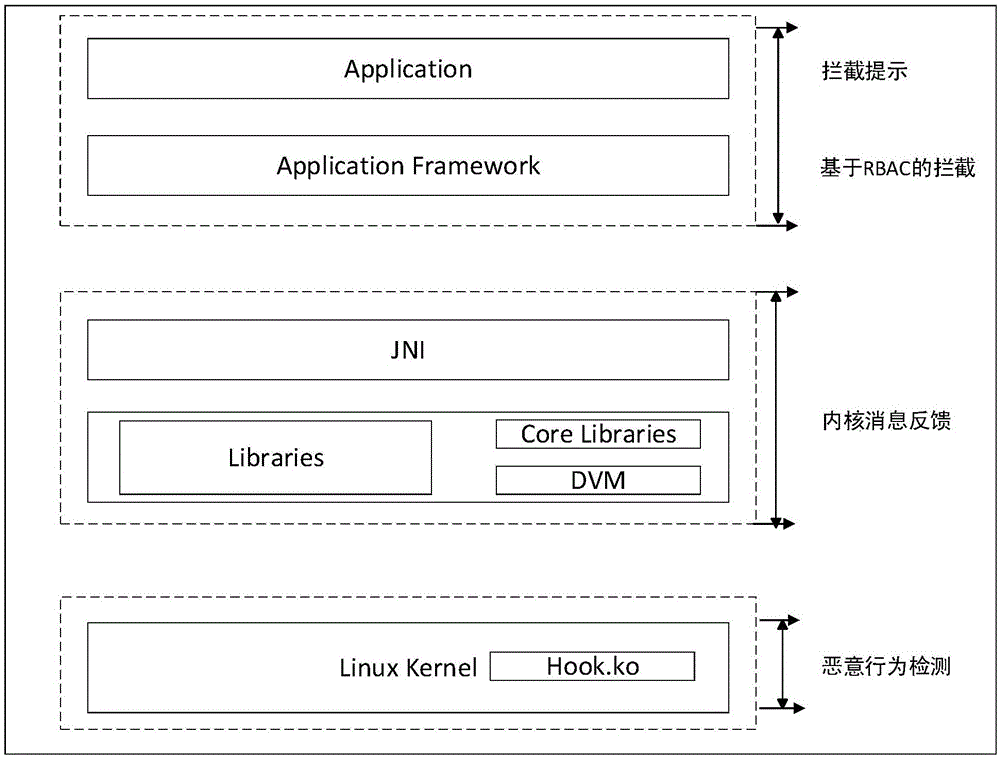
[0021] figure 1 , is an architecture diagram of the RBAC-based malicious program interception described in the present invention. According to the Android system architecture, the Android system is divided into two parts, the user space and the kernel space. This figure describes how the kernel layer and the application layer implement malicious behaviors against the application program after the application program is installed on the Android mobile device when the application program is executed. Specifically, RBAC-based malicious program interception includes the following four modules: malicious behavior detection module, kernel message feedback module, interception prompt module, and RBAC-based interception module.
[0022] Among them, the malicious behavior detection module is deployed in the AndroidLinux kernel layer. It realizes the mo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com