Access control system and access control method of fine-grained privacy security
An access control, privacy and security technology, applied in the transmission system, electrical components, etc., can solve the problems of not being able to adapt to social networks, reducing system efficiency, and high overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
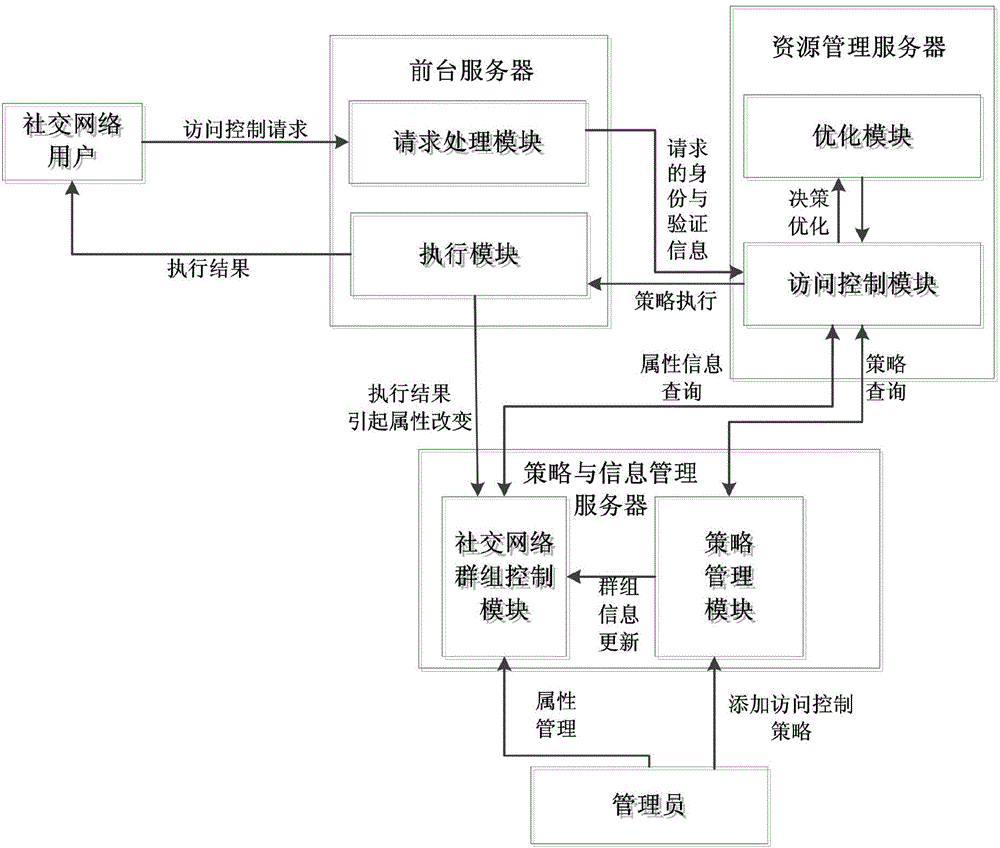
[0064] In this embodiment, a fine-grained privacy and security access control system is applied to m administrators, n participants, the relationship between administrators and participants, the relationship between participants, and the In the social network composed of the resources submitted by the participants and the tag library maintained by the administrator; m<n; and the access control model is established by the social network;
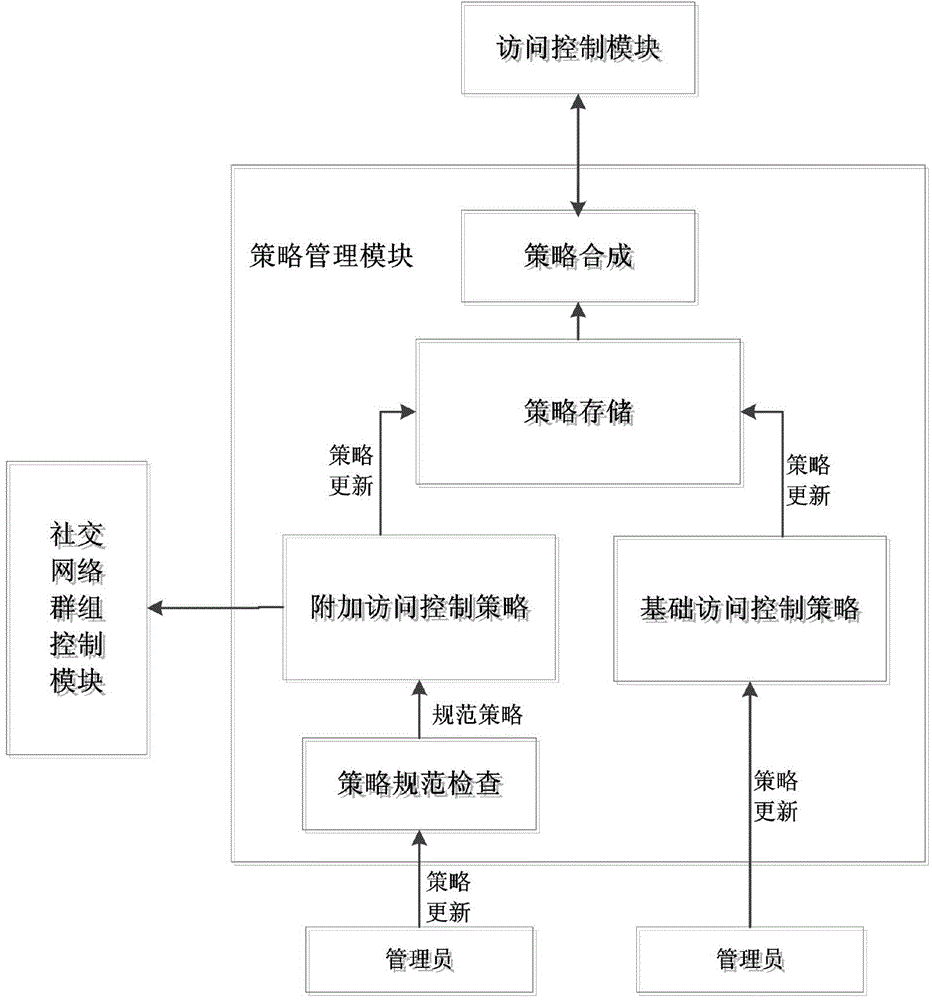
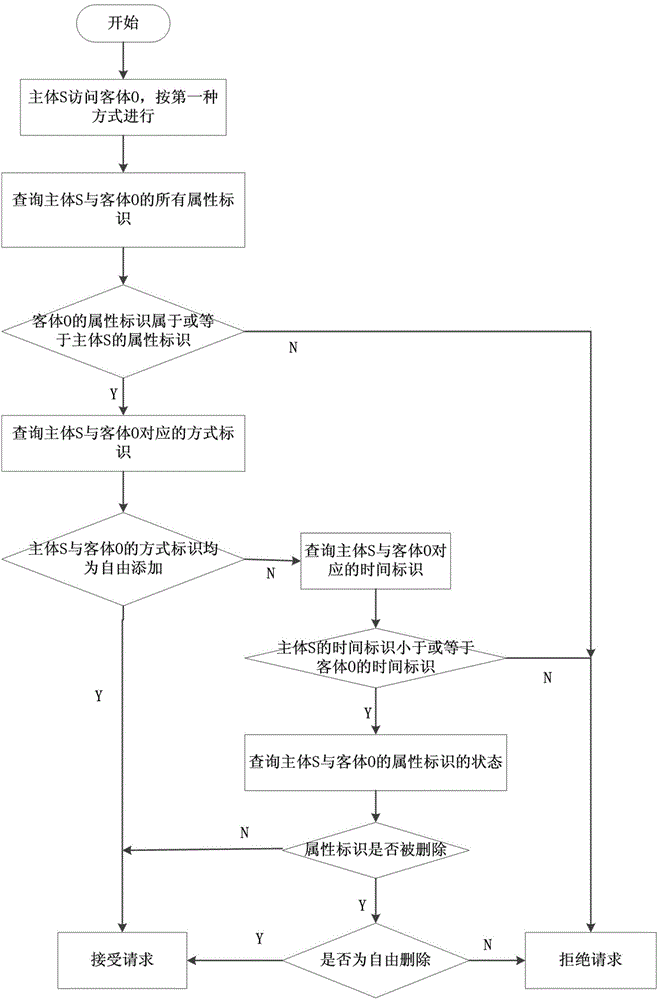
[0065] The access control model includes: n participants, resources submitted by n participants, attribute sets of n participants, attribute sets of resources submitted by n participants, m administrators, m administrators Maintained tag library, set of resource access methods of n participants; attribute sets of n participants include subject attribute identifier, subject time identifier and subject mode identifier; attribute sets of resources submitted by n participants include object attributes Identification, object time identification an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com