Charging method with privacy protection in smart power grid
A privacy-preserving, smart-grid technology for handling coins or banknotes, coin-free or similar appliances, coin-operated devices for distributing discrete items, etc. Guaranteed safe effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
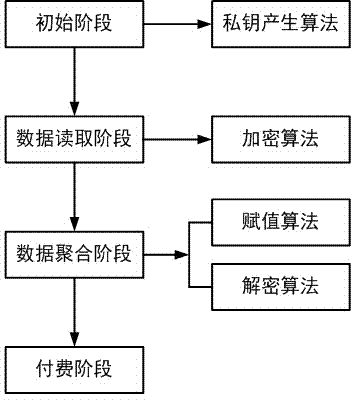
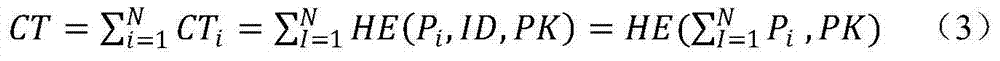
[0020] A billing method with privacy protection in smart grid, figure 1 It is a flowchart of the present invention. The smart meter records the electricity used by the user in real time, encrypts the recorded data by means of homomorphic encryption, and sends the ciphertext to the aggregator. After a period of time, the aggregator sums the collected ciphertexts about the power consumption of a certain user; then decrypts the ciphertexts to obtain the plaintext of the sum of the power consumption of the user in that time period; finally the aggregator sends the plaintext to the power The company and the power company calculate the electricity consumption cost of the user. Specific steps are as follows:
[0021] 1) Initialization phase: Assumption 1 k is a security parameter. The system generates a public-private key pair for homomorphic encryption:
[0022] KG(1 k ) → (SK, PK) (1)
[0023] where KG (1 k ) is the key generation algorithm. The algorithm inputs a security...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com