Permission data validation method, device and system
A verification method and permission technology, applied in the field of permission verification, can solve problems such as unavailability of permission verification and inaccessible application interface.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other. The present application will be described in detail below with reference to the accompanying drawings and embodiments.
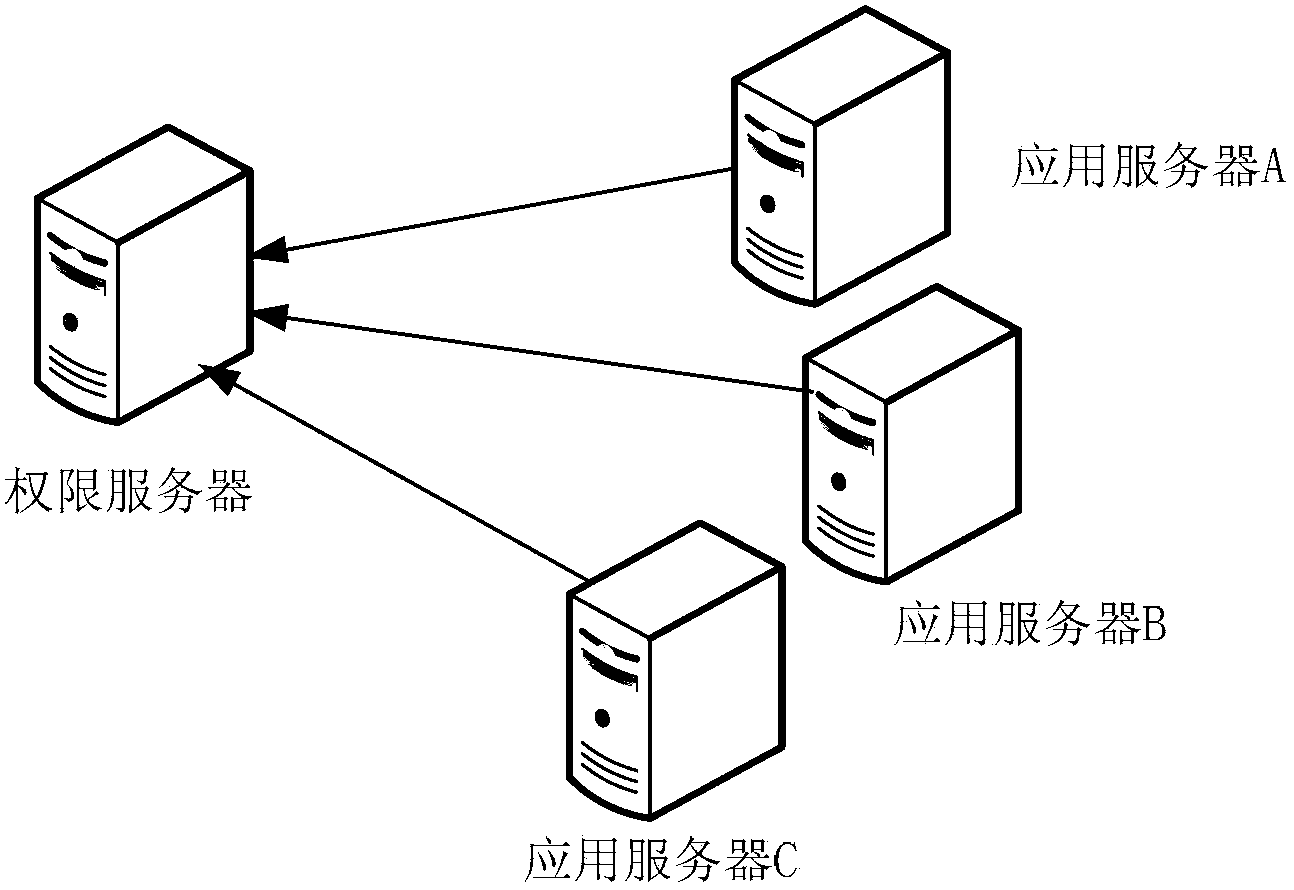
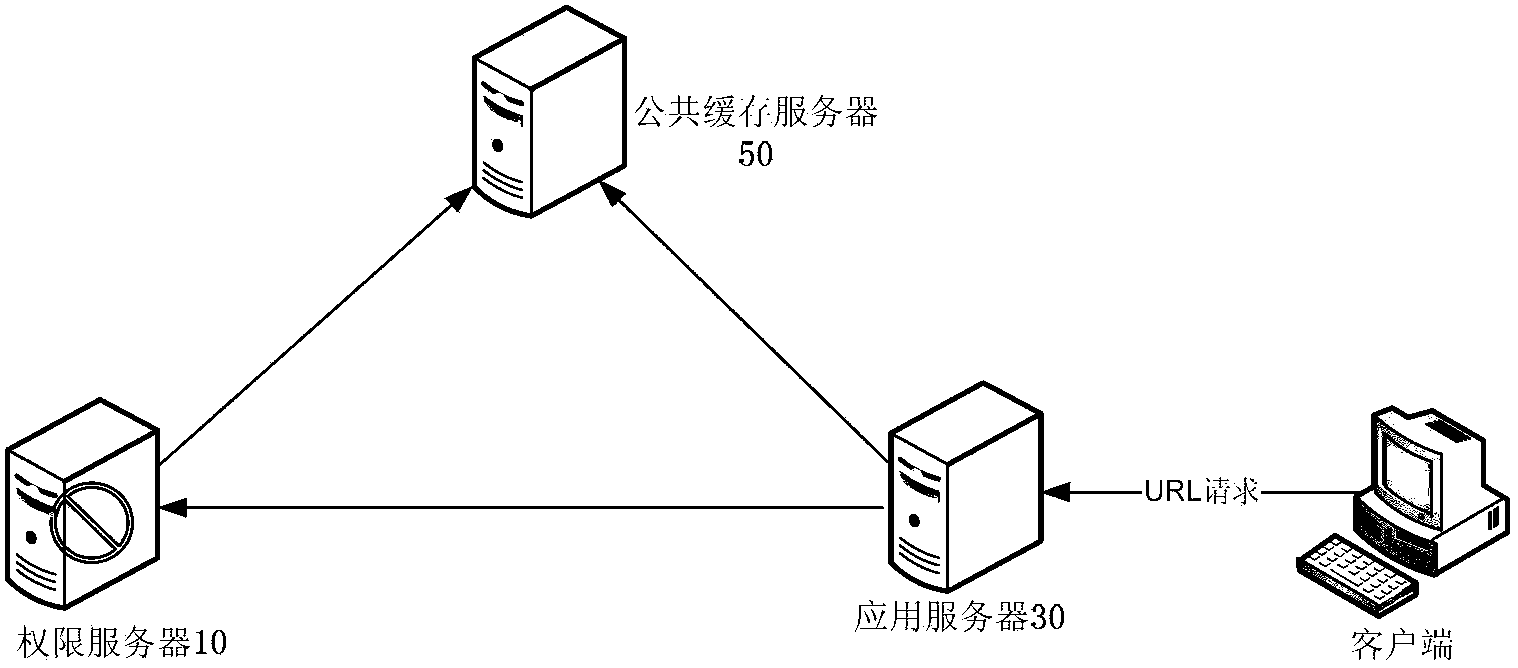
[0028] figure 2 is a schematic structural diagram of a verification system for authority data according to an embodiment of the present application; image 3 is based on figure 2 A schematic diagram of the detailed structure of the permission data verification system of the illustrated embodiment.
[0029] Such as figure 2As shown, the authorization data verification system includes: an authorization server 10; an application server 30, configured to receive authorization data access information from a client, and process the authorization data access information according to keyword generation rules to generate authorization verification keywords; One or more public cache servers 5...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com