Cross-safety-domain access control system and method based on privacy protection
An access control and privacy protection technology used in the field of information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] The specific implementation manners of the present invention will be further described in detail below in conjunction with the accompanying drawings.
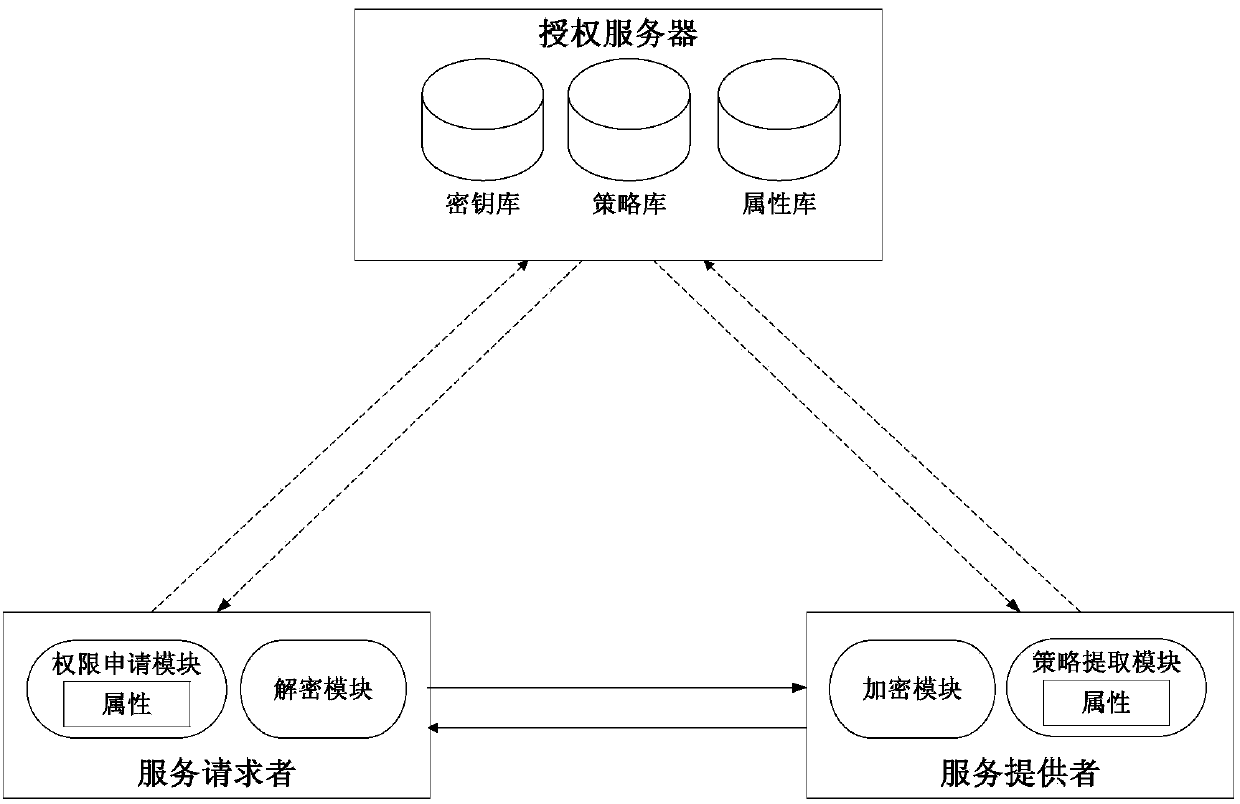
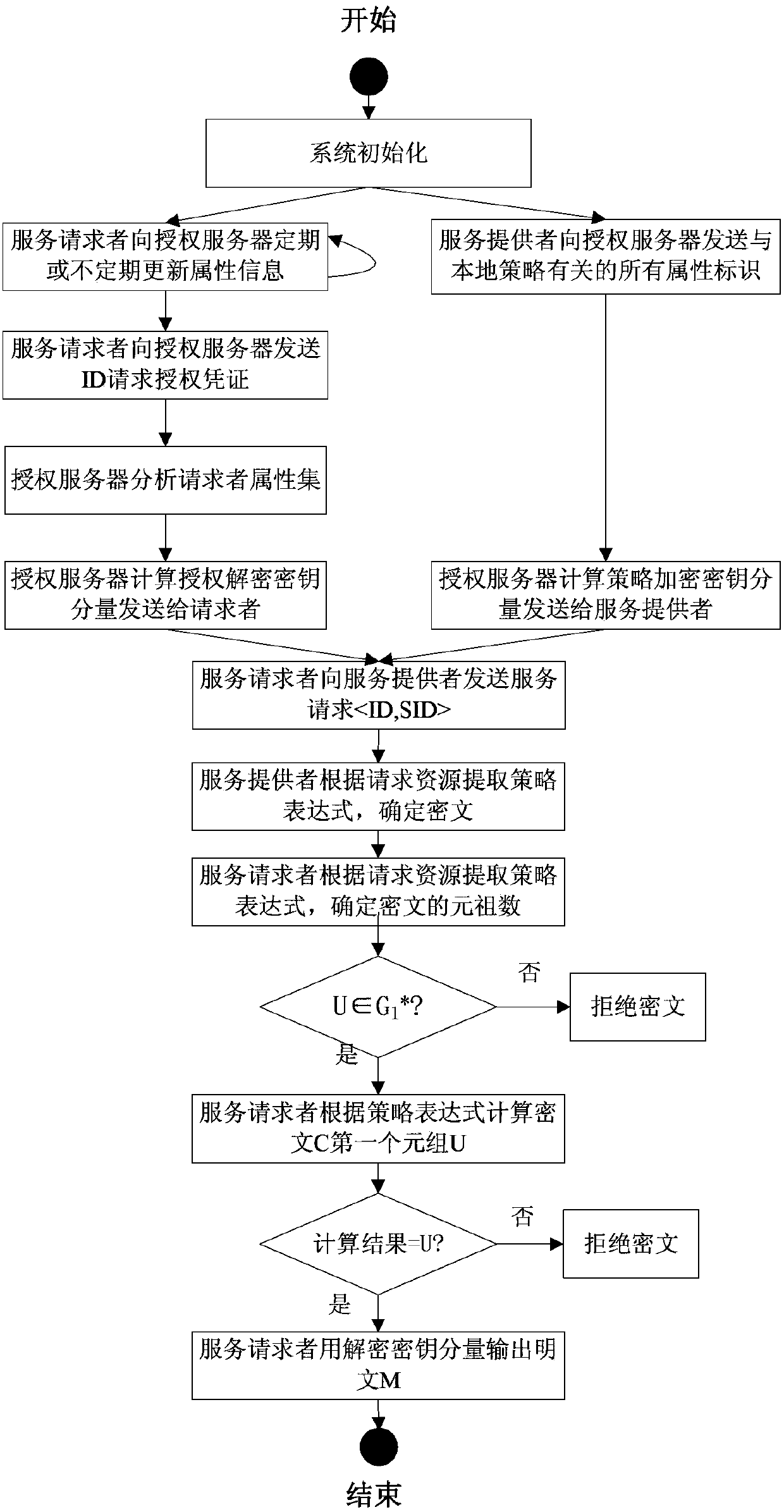
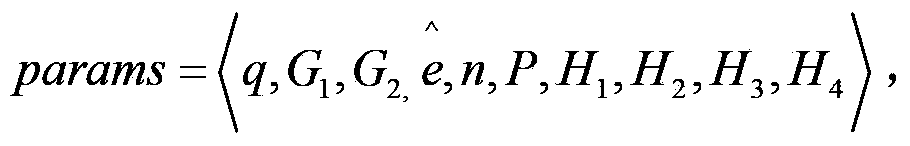
[0058] Based on the access control model, the privacy protection mechanism combines identity-based encryption technology to realize the privacy of cross-domain access control. This mechanism is divided into five parts: system initialization, authorization assignment, policy customization and response, encryption processing, message recovery and verification. This mechanism uses attribute Boolean variables to describe policy expressions, transforms policy expressions into disjunctive paradigms, and forms a mapping between access control decisions and policy Boolean expression values. The service provider encrypts the information with the policy implied in the public key, and the requester decrypts the message with the decryption key that implies the authorization assignment, and only if the requester has the private key c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com