A Method for Identifying Critical Attack Paths in Business Systems
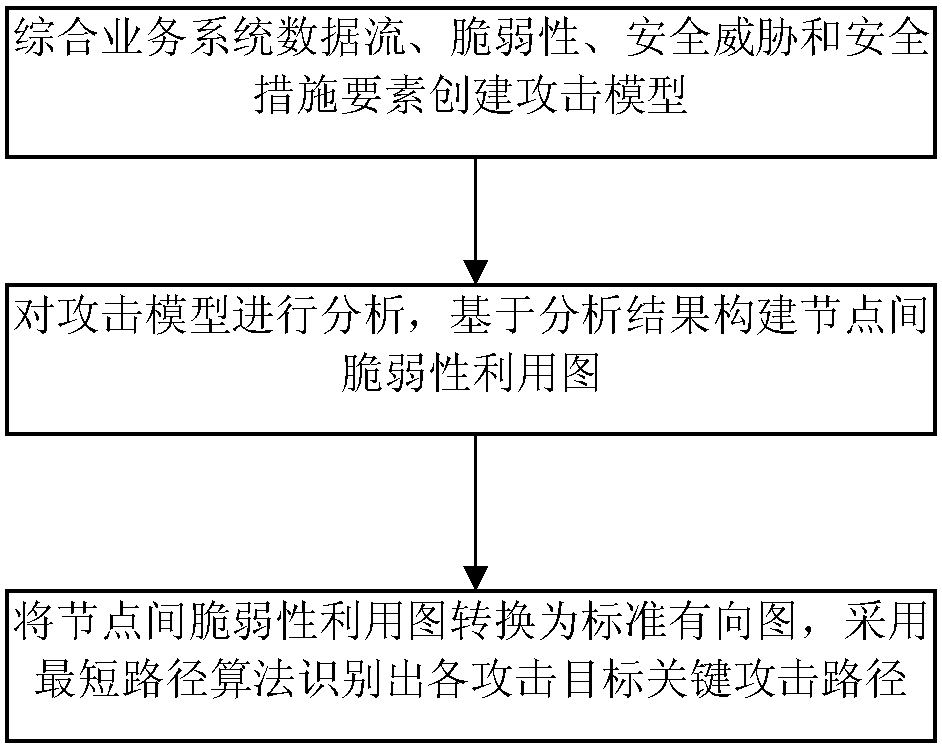
A business system and attack path technology, applied in the field of network information security, can solve problems such as high complexity, unsuitable attack path identification, unavailable key attack path identification methods, etc., and achieve good scalability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0108] The experimental environment of the WEB application business system referred to in this embodiment is as attached Figure 9 As shown, the following security policy is configured: the firewall deployed at the boundary of the network trust zone divides the network into three security zones: the Internet, the intranet, and the DMZ zone. The WEB server deployed in the DMZ provides WEB services for users. Internal users on the intranet are not allowed to directly connect to the external network to prevent attacks such as external worms from directly entering the internal network and ensure that the WEB server provides external services. The access control strategy between each security domain is as follows: 1) Only Internet users are allowed to access DMZ area H 2 IISWEB service on and H 3 DNS domain name service on the Internet; 2) H in the DMZ area 2 Allow access to H 3 Sendmail service on the Internet and intranet H 4 MYSQL service on; 3) Prohibit H 2 and H 3 Direc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com