Data security protection method and data security protection device
A technology of data security and protection device, applied in the computer field, can solve the problems of data encryption key being easily obtained illegally, reducing the performance of computer system, low security, etc., so as to improve data security, reduce performance and ensure security Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] The principles and features of the present invention are described below in conjunction with the accompanying drawings, and the examples given are only used to explain the present invention, and are not intended to limit the scope of the present invention.
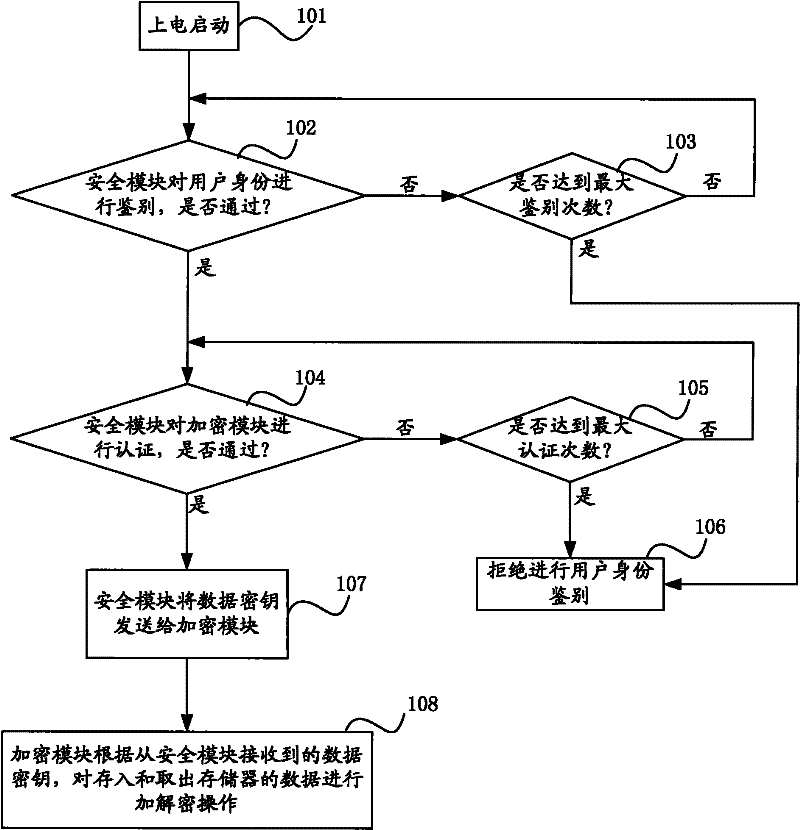
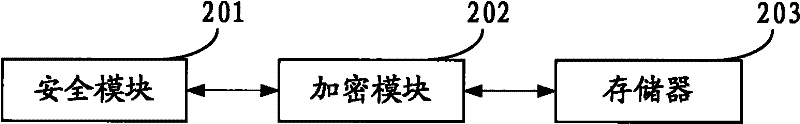
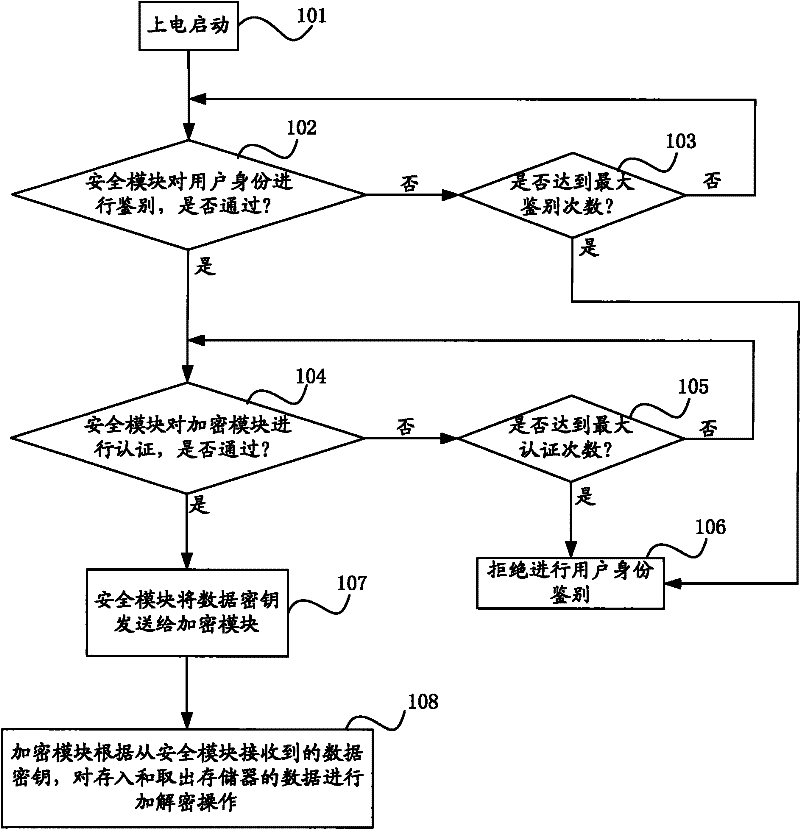
[0039] The data security protection method of the present invention comprises the following steps:
[0040] Step A: The security module authenticates the user identity, if the authentication fails, execute step B, otherwise execute step C;
[0041] Step B: The security module judges the number of times of user identity authentication, if the number of times does not reach the limit value, then execute step A, otherwise execute step Z;
[0042] Step C: the security module authenticates the encryption module, and if the authentication fails, execute step D; otherwise, execute step E;
[0043] Step D: The security module judges the number of authentications to the encryption module, if the number of times does not rea...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com