Method for extracting malicious code behavior characteristic
A malicious code and feature extraction technology, applied in the field of network security, can solve the problems of huge feature library, low feature accuracy, and inability to extract, and achieve the effect of enhancing anti-interference, eliminating feature changes, and small size of the feature library.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
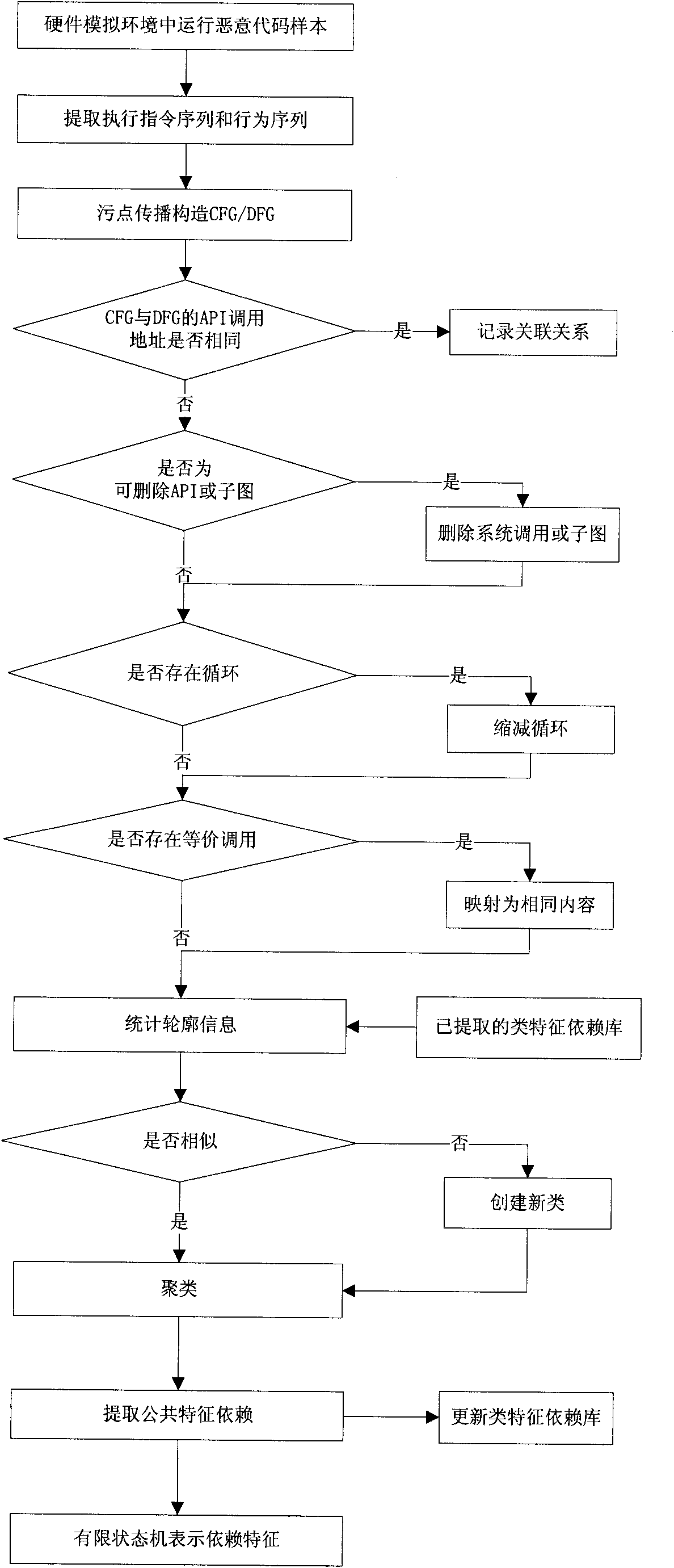
[0066] The technical scheme of the present invention is described in detail below in conjunction with accompanying drawing:
[0067] like figure 1 As shown, a malicious code feature extraction method based on control dependence and data dependence, including steps:
[0068] 1. Extract the execution instruction sequence and behavior sequence of the malicious code.
[0069] The malicious code is executed in the environment of the hardware simulator by adopting the method recorded in the translation layer of the hardware simulator. By adding a disassembly engine at the translation level, all instructions and register information executed by malicious code samples are recorded after the instructions are translated and before execution. For the extraction of the behavior sequence, it is necessary to obtain the API address and parameters. After the process is loaded and before the code is executed, the present invention reads the memory of the process through the virtual machine, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com