Public key cipher encrypting and decrypting method based on neural network chaotic attractor
A technology of chaotic attractor and neural network, which is applied to the public key of secure communication, user identity/authority verification, digital transmission system, etc., and can solve problems such as inappropriate long message encryption, slow public key encryption speed, and low security level
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
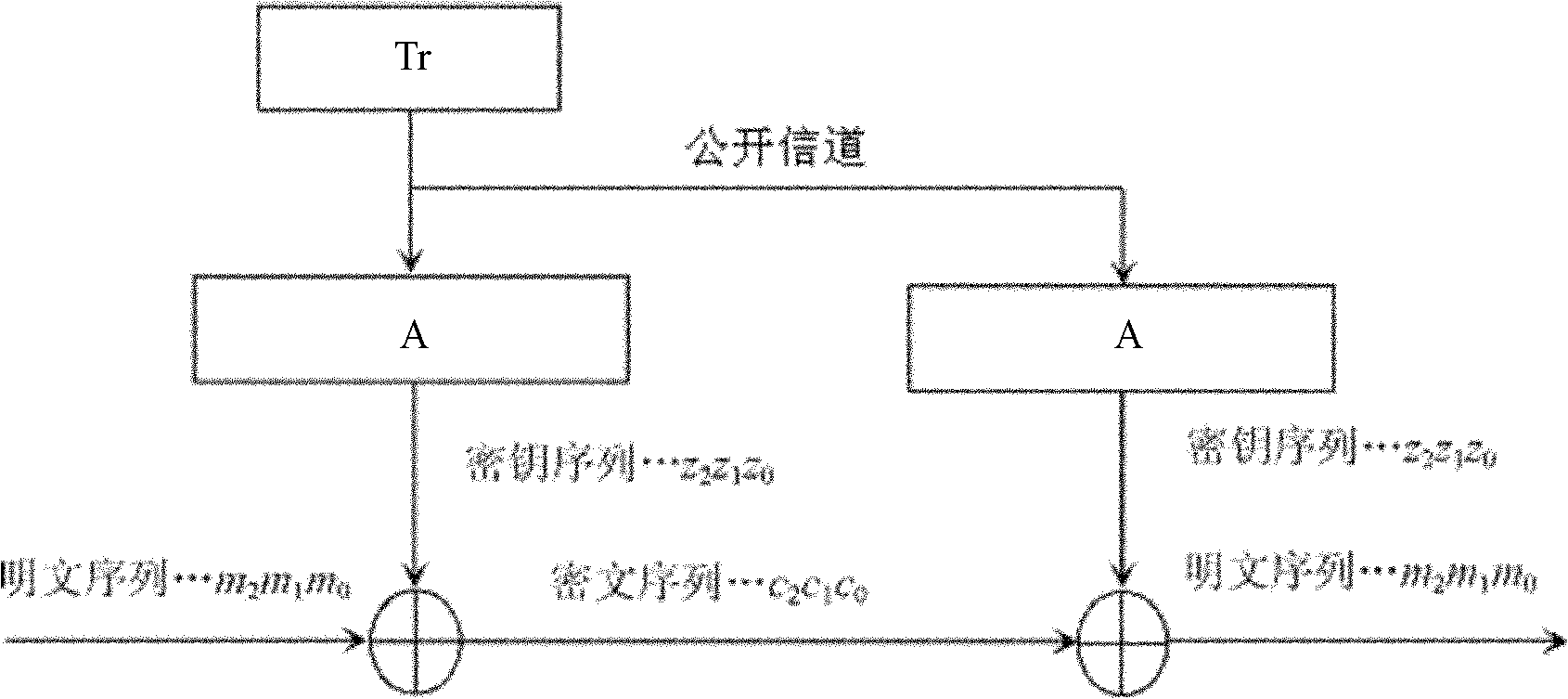
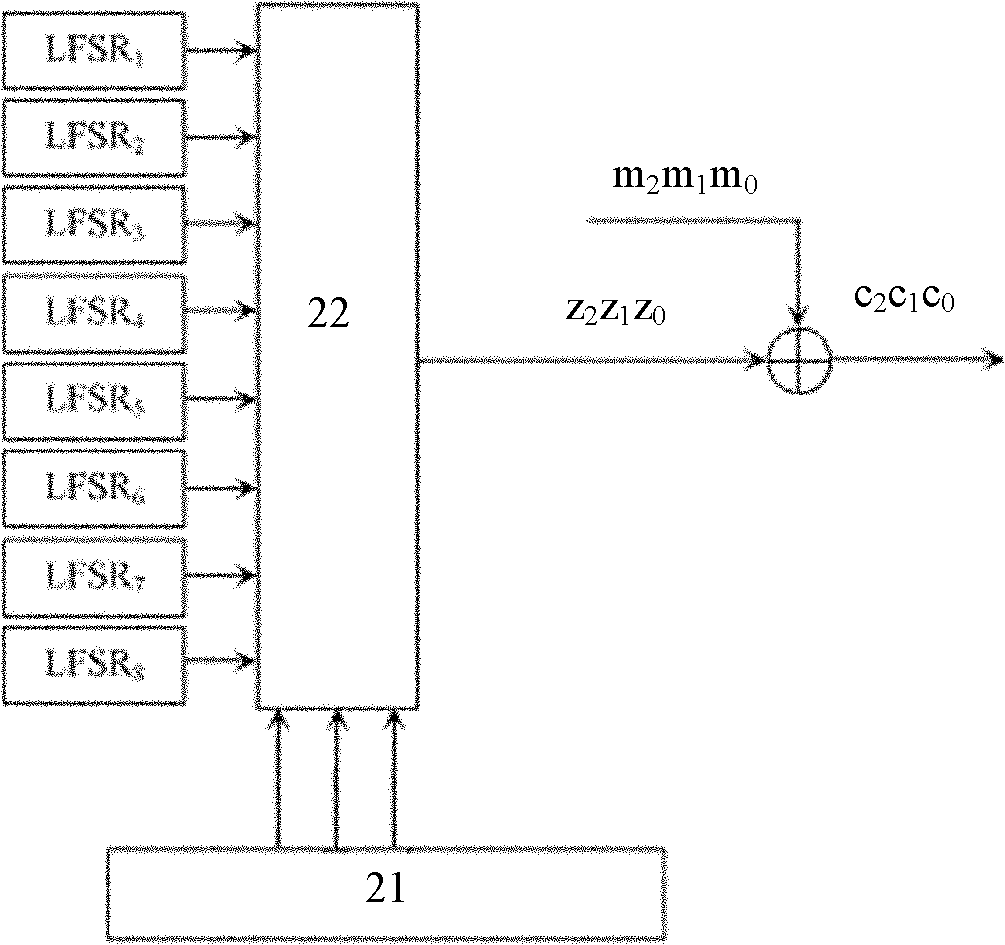
[0035] One, encryption and decryption method of the present invention:
[0036] The present invention is a kind of public key cryptographic encryption and decryption method based on neural network chaotic attractor, comprising the following steps:
[0037] 1) Key generation and distribution
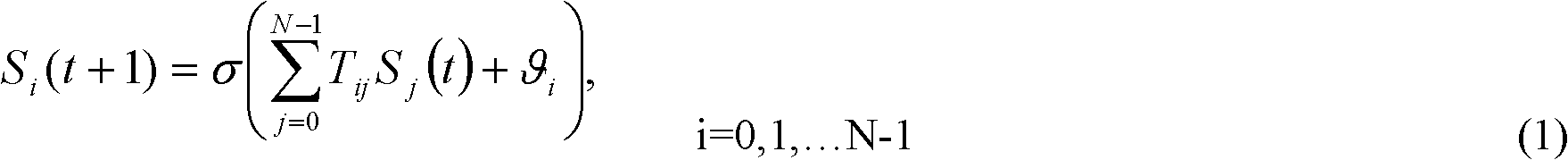
[0038] (1) A group of users who need confidential communication share a carefully selected synaptic connection matrix T 0 , each user randomly selects a different transformation matrix in the nth-order square matrix exchange family;
[0039] (2) Each user saves his own public key, together with other information such as user name and address, in the public key repository of the certification center by means of digital signature, and obtains the public key certificate issued by the certification center. Before the second data encryption communication, the identity authentication of both communication parties is carried out through the public key certificate;
[0040] (3) Use the authent...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com