Method and system for providing password resources and host machine
A host machine and cipher machine technology, applied in the field of cipher processing, to achieve the effect of easy security control and compliance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
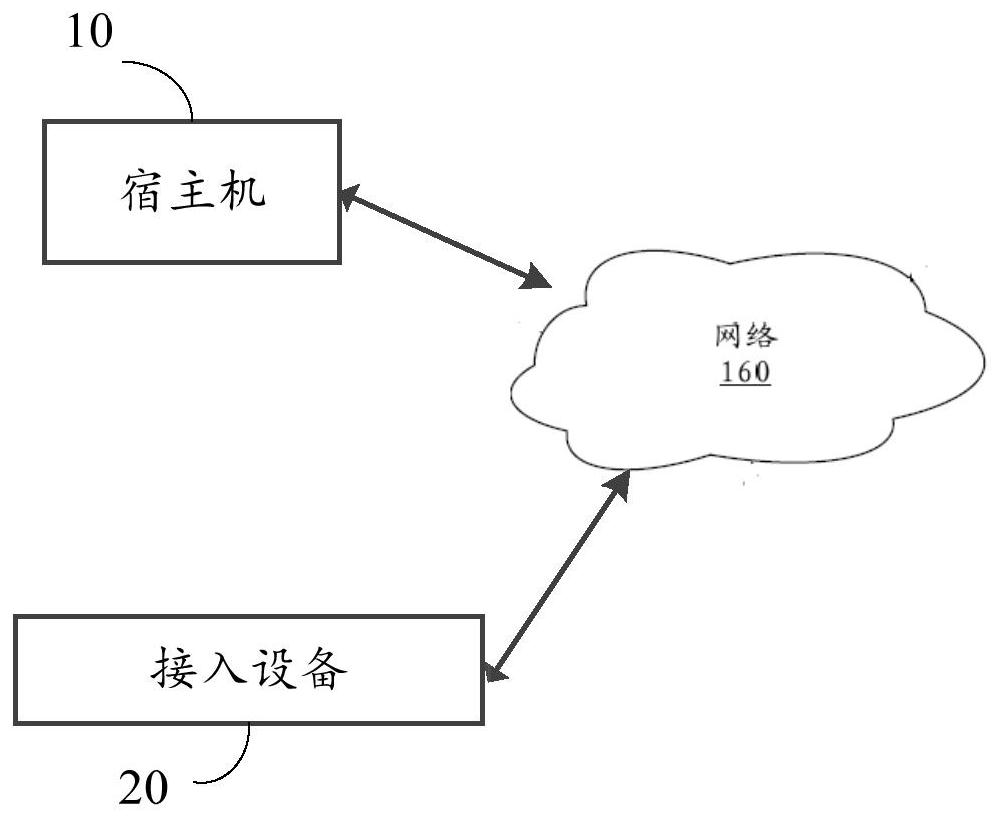
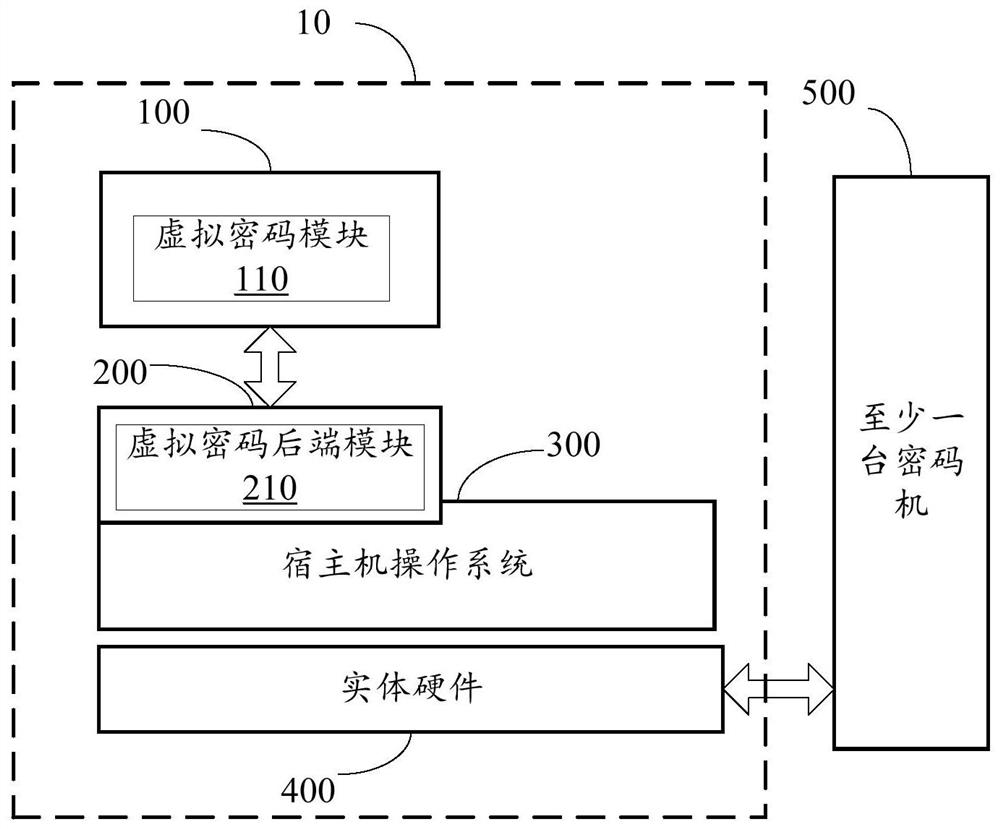
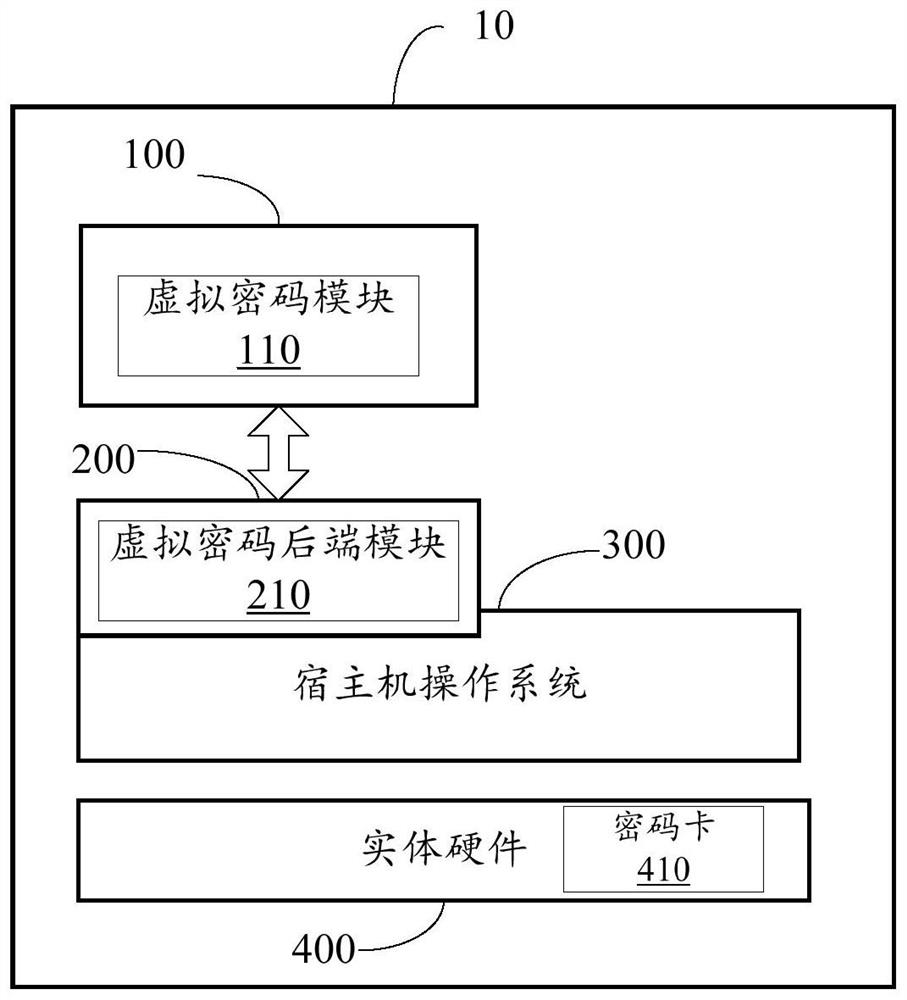
[0038] The technical solutions in the embodiments of the present application will be described below with reference to the drawings in the embodiments of the present application.
[0039]It should be noted that like numerals and letters denote similar items in the following figures, therefore, once an item is defined in one figure, it does not require further definition and explanation in subsequent figures. Meanwhile, in the description of the present application, the terms "first", "second" and the like are only used to distinguish descriptions, and cannot be understood as indicating or implying relative importance.
[0040] The related technology and the defects in the related technology are introduced below. Usually, there are several ways to protect business applications on virtual machines of cloud services using cryptographic technology: 1) Cloud cipher machine method, cloud cipher machine is on the physical cipher machine, through the underlying hardware and software v...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com