Multi-image encryption method based on three-dimensional scrambling model and fractional Fourier transform
A technology of fractional Fourier and encryption methods, which is applied in image data processing, image data processing, digital data protection, etc., can solve the problems of weak security and low encryption efficiency, and achieve security protection, security improvement, The effect of improving the encryption effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The implementation process of the present invention will be further described in detail below in conjunction with specific drawings and examples.
[0034] Figure 4 is the encryption flowchart of this method.
[0035] The programming software used is Matlab R2016a, select Figure 5 Nine images of size 512×512 are shown as the original image set. Using this method, Alice's encryption process is detailed as follows.
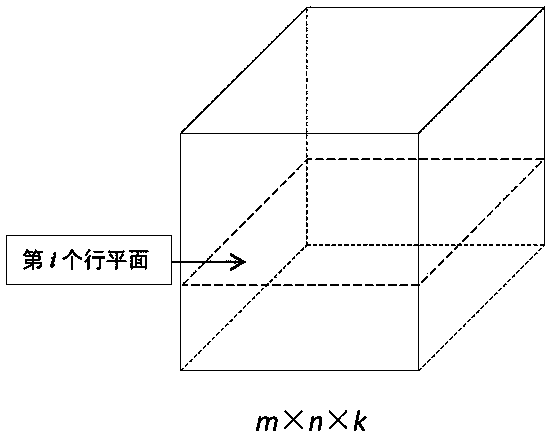
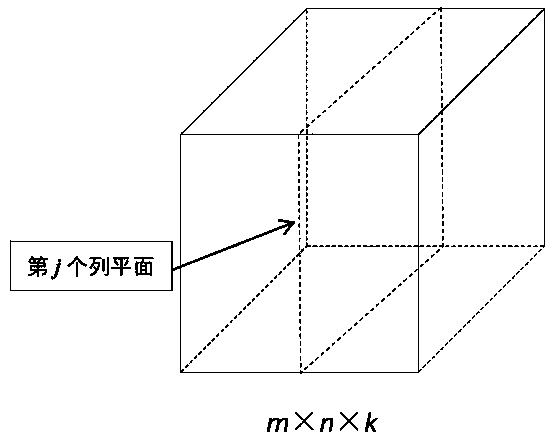
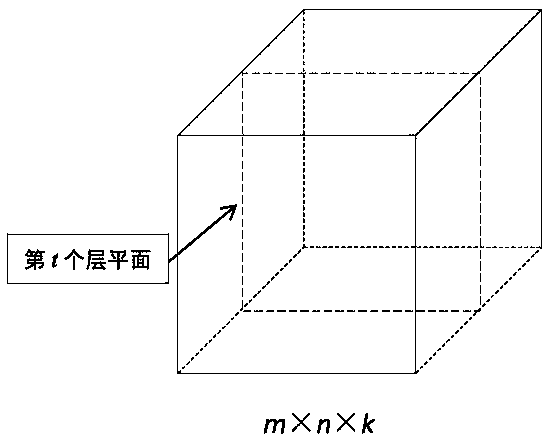
[0036] Step 1: Image cube construction: Let the 9 original images be I 1 1 , I 1 2 , …, I 1 9 , the size of which is 512×512, the 9 original images are superimposed into a 9-layer image cube B 1 , with a size of 512×512×9.
[0037] Step 2: Randomly select the initial value of the five-dimensional hyperchaotic system x 1 =0.236542532712, y 1 =0.361425721124, z 1 =0.625121457935, u 1 =0.152365227495 and v 1 =0.812165374593; Iterate the system 262144 times to obtain 5 chaotic sequences X ={ x i} 262144 , Y ={ y i} 262144 , Z ={ z ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com