Method for monitoring industrial control system information security domain
An industrial control system and information security technology, applied in the field of monitoring industrial control system information security, can solve problems such as incomplete details
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
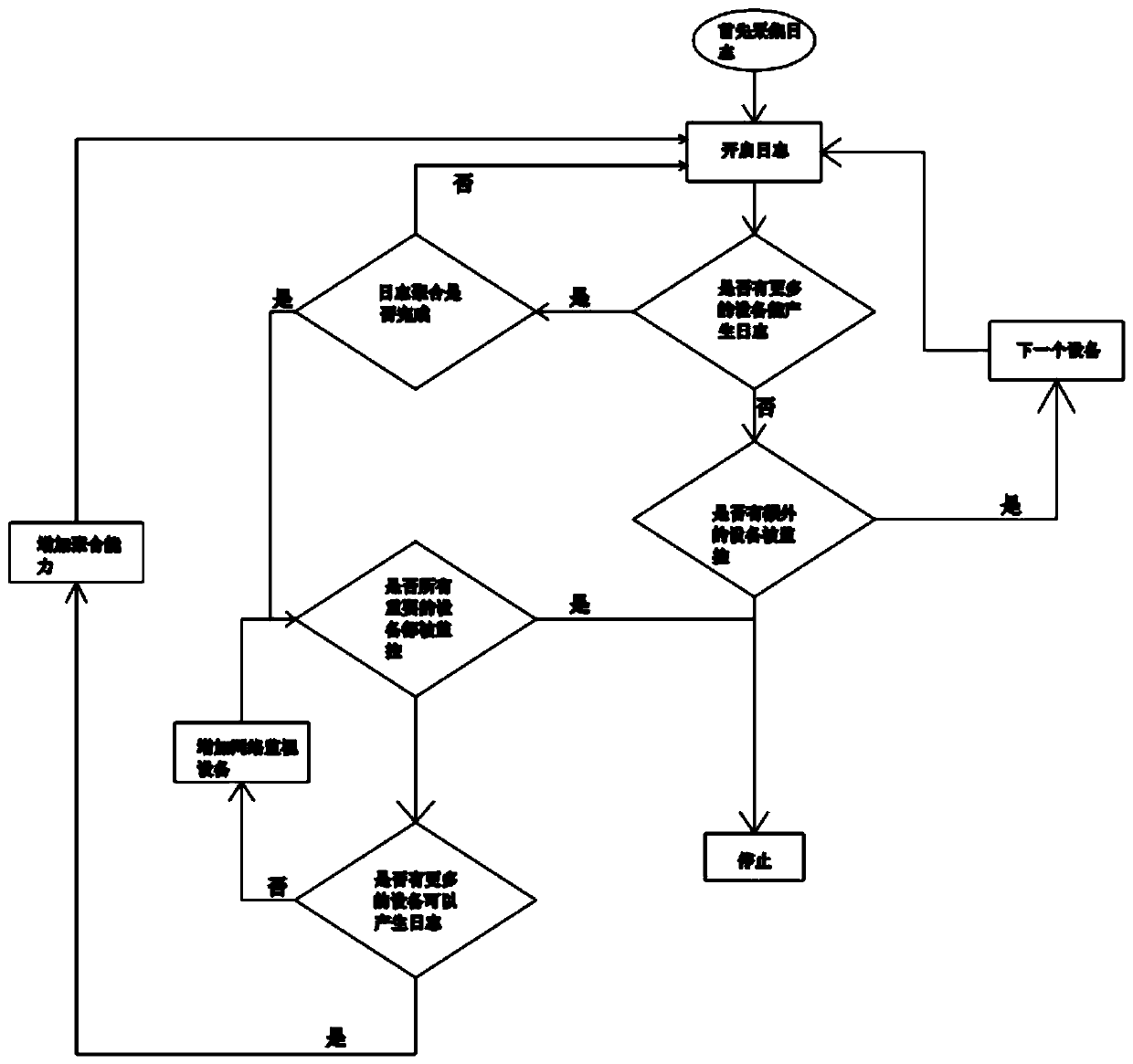
[0019] The present invention will be described in further detail below in conjunction with the accompanying drawings.
[0020] (1) Log collection
[0021] Log collection refers to collecting data from all possible sources of data generation, that is, guiding and outputting log information to a log collection node and using a network storage device. If the events are stored in a local database instead of a log file, the event information needs to be reprocessed locally by software agents such as snare and transmitted through standard system logs. The collected logs are used to view user activities, including user configuration changes, statistics of users who log in and out, login operations performed by users, and logout operations performed by users. By analyzing the collected logs, if abnormal phenomena are detected, such as the increase of illegal new users, sensitive user operations, etc., a warning will be issued.
[0022] (2) Direct monitoring
[0023] Since some syst...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com