Bidirectional authentication method and system based on encrypted two-dimensional code
A technology of two-way authentication and two-dimensional code, applied in the field of two-way authentication method and system based on encrypted two-dimensional code, can solve problems such as security loopholes, and achieve the effect of improving information security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
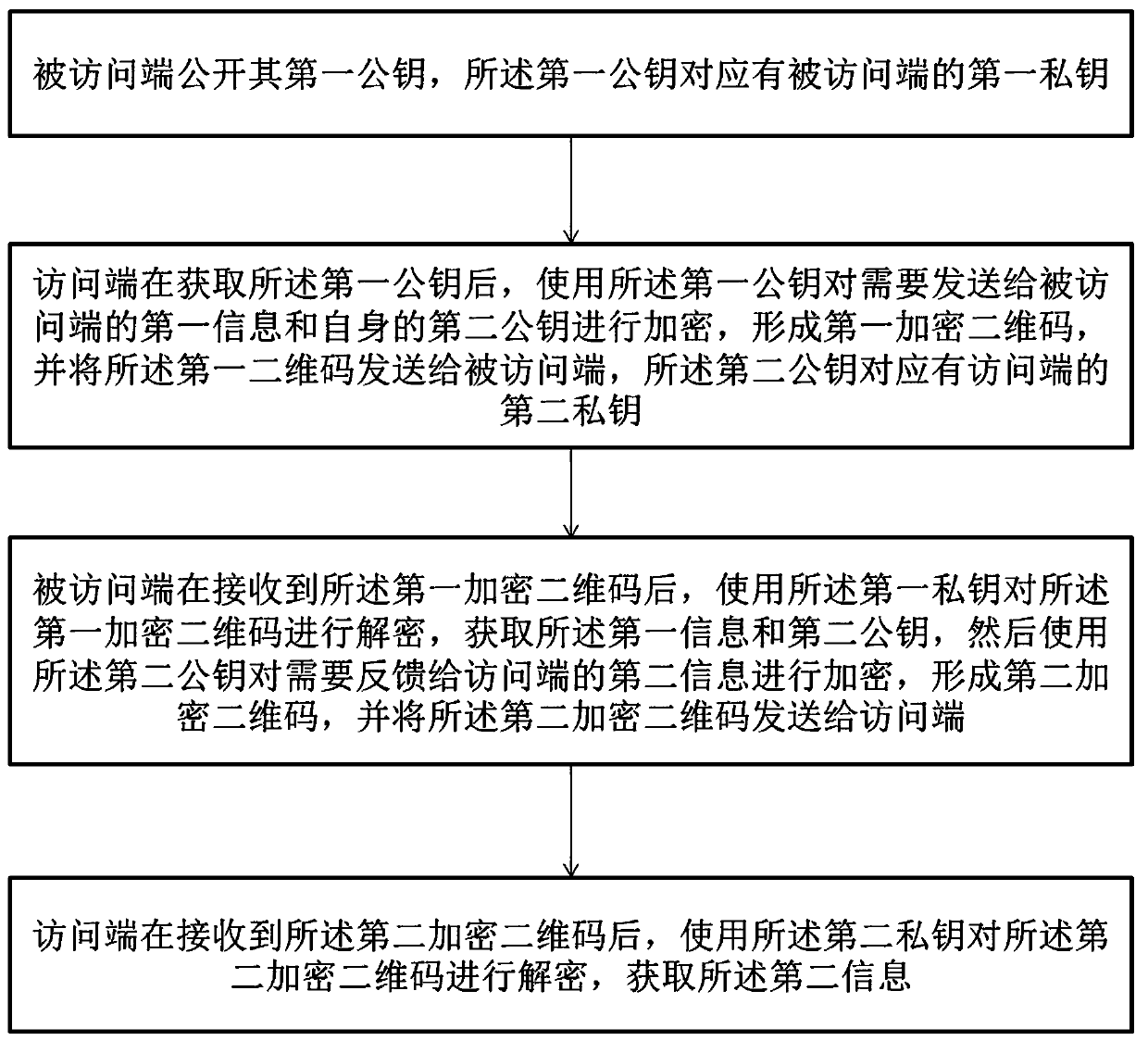
Method used
Image
Examples
Embodiment 2
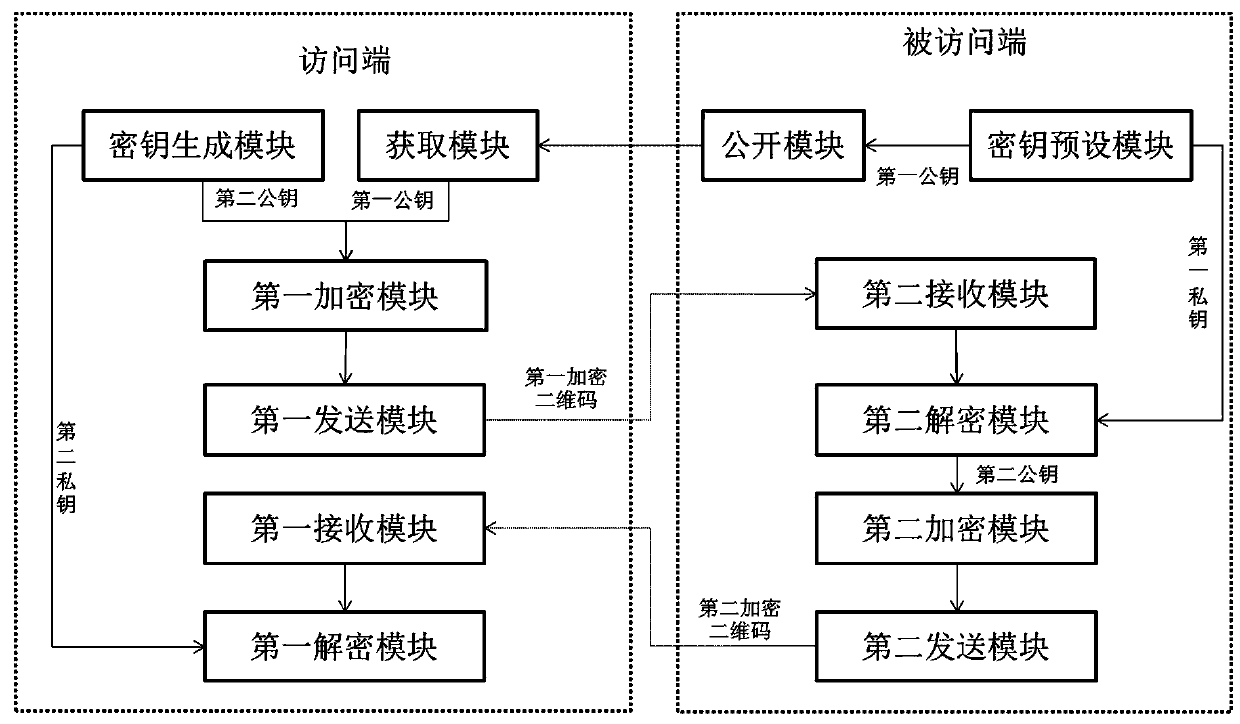
[0049] Such as figure 2 As shown, a two-way authentication system based on an encrypted two-dimensional code is applied to the method described in Embodiment 1. The system includes the access terminal and the accessed terminal, among which
[0050] Access terminals include:
[0051] An acquisition module, configured to acquire the first public key disclosed by the accessed terminal, preferably acquire the first public key from the public key two-dimensional code by scanning codes, and the first public key corresponds to the accessed terminal's first private key;
[0052] A key generation module, configured to randomly generate the second public key and the second key;
[0053] The first encryption module is configured to use the first public key to encrypt the first information that needs to be sent to the accessed terminal and its own second public key to form a first encrypted two-dimensional code, and the second public key corresponds to The second private key of the a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com