Physical layer secure transmission method based on an asymmetric key
A physical layer security, asymmetric key technology, applied in the field of physical layer security transmission methods and systems based on asymmetric keys, can solve problems such as difficulty in managing and storing keys
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0125] Below, the present invention will be further described in conjunction with the accompanying drawings and embodiments.
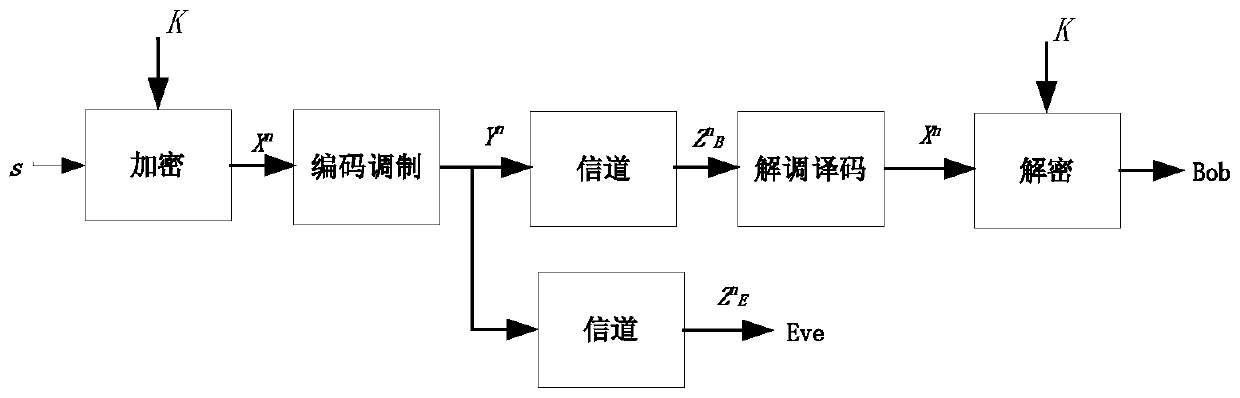
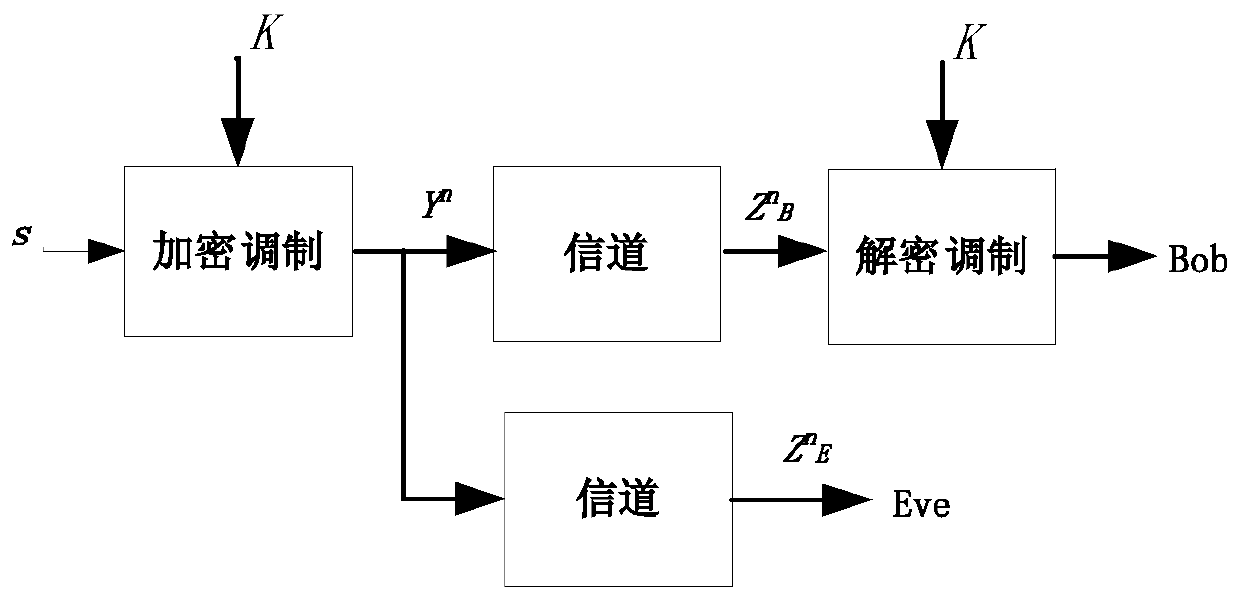
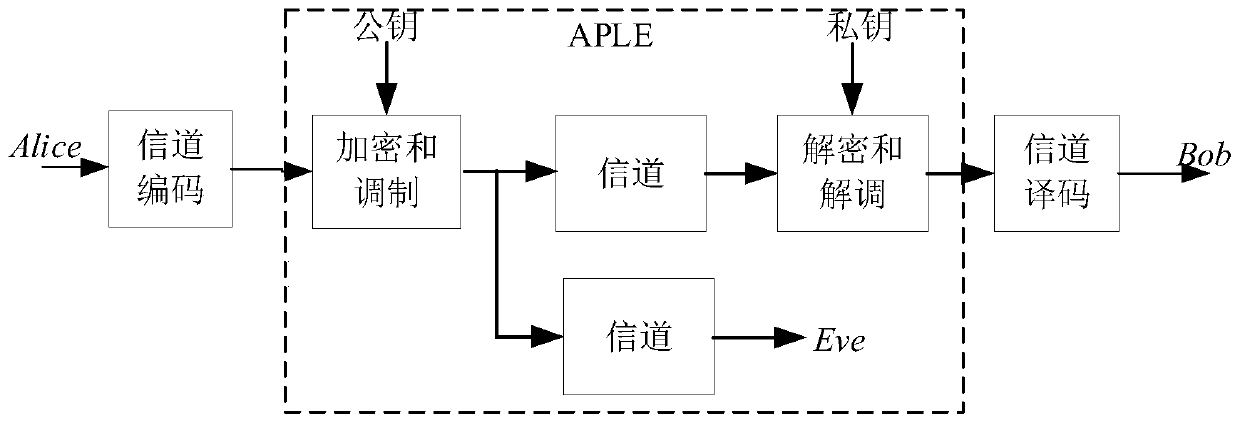
[0126] Such as Figure 4 As shown, a physical layer security transmission method based on asymmetric key,
[0127] The sender sends the binary information S b Mapping into a complex vector signal X,
[0128] Encrypt by security matrix U, convert complex vector signal X into complex vector signal Y, Y=UX,
[0129] The complex vector signal Y is sequentially processed by the IFFT module, adding the cyclic prefix module, and the DAC module, and then sent out by the radio frequency module;
[0130] The receiver receives the signal through the radio frequency module, processes it through the ADC, removes the cyclic prefix module, and FFT transformation module to obtain the complex vector signal Y', decrypts it through the security matrix, obtains the complex vector signal X', and further restores the binary signal through demapping information.
[0131...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com