A method and a device for providing and acquiring security identity information
A technology of identity information and identity, which is applied in the direction of data processing applications, instruments, sensing record carriers, etc., and can solve the problems of face verification breaches (attacks against real-name and real-person verification, etc.)
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
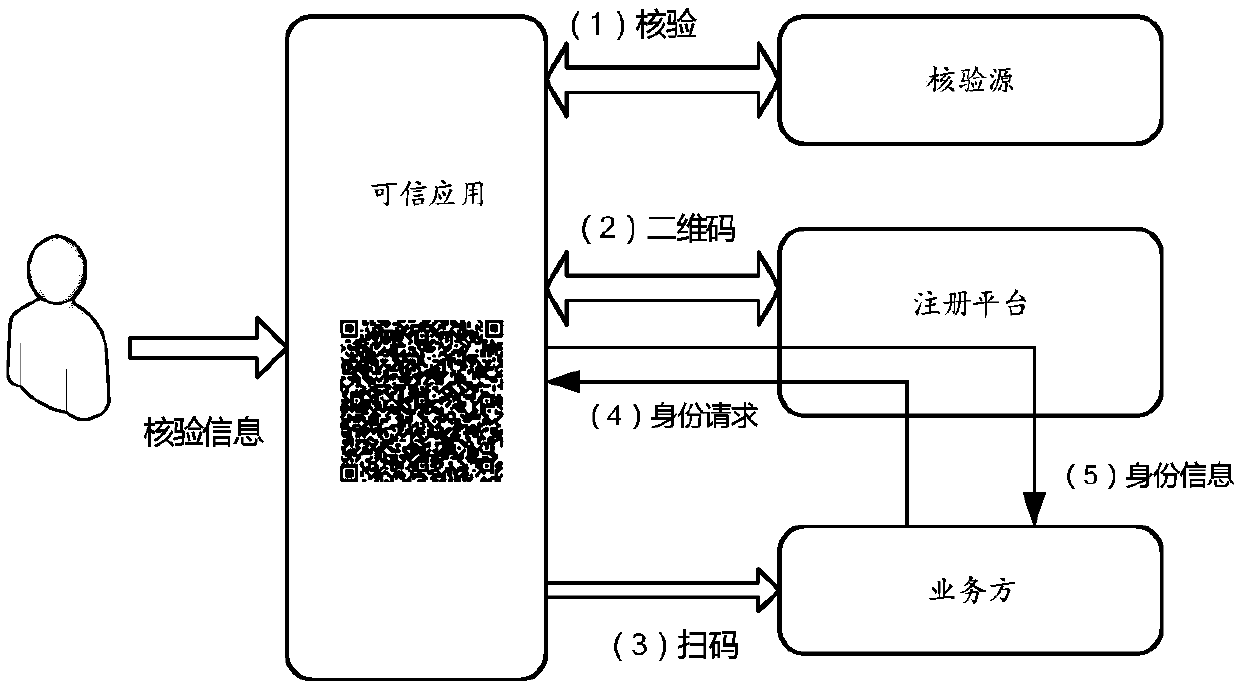
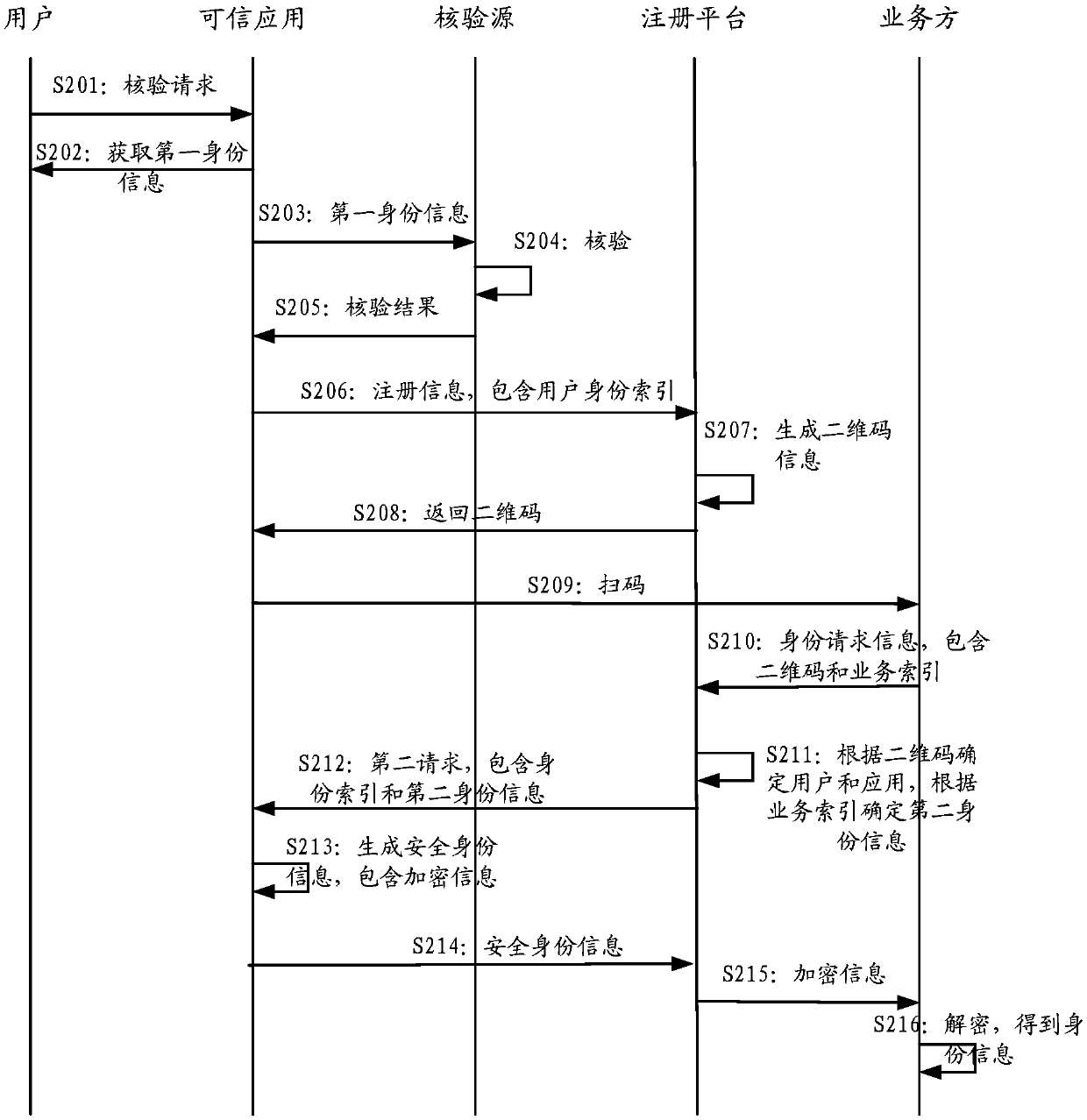
Method used
Image
Examples
Embodiment approach
[0206] According to an implementation manner, the third-party trusted verification source includes a first verification source and a second verification source; the credential acquisition unit 50 is configured to:
[0207] Obtaining the first verification information and the second verification information as verification identity information;
[0208] sending the first verification information to the first verification source, and sending the second verification information to a second verification source;
[0209] receiving a first credential from the first verification source and a second credential from the second verification source;
[0210] The first credential and the second credential are combined to generate the trusted credential.
[0211] In one embodiment, the device 500 further includes a registration information generating unit (not shown), which generates an identity index in the following manner:
[0212] using the verified first identity information as the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com