Privacy protection method and system based on cp-abe ciphertext in fog computing environment
A CP-ABE, privacy protection technology, applied in the field of access control based on CP-ABE ciphertext, can solve the problem of not knowing the ciphertext
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] Below in conjunction with accompanying drawing and specific embodiment, further illustrate the present invention, should be understood that these examples are only for illustrating the present invention and are not intended to limit the scope of the present invention, after having read the present invention, those skilled in the art will understand various aspects of the present invention All modifications of the valence form fall within the scope defined by the appended claims of the present application.
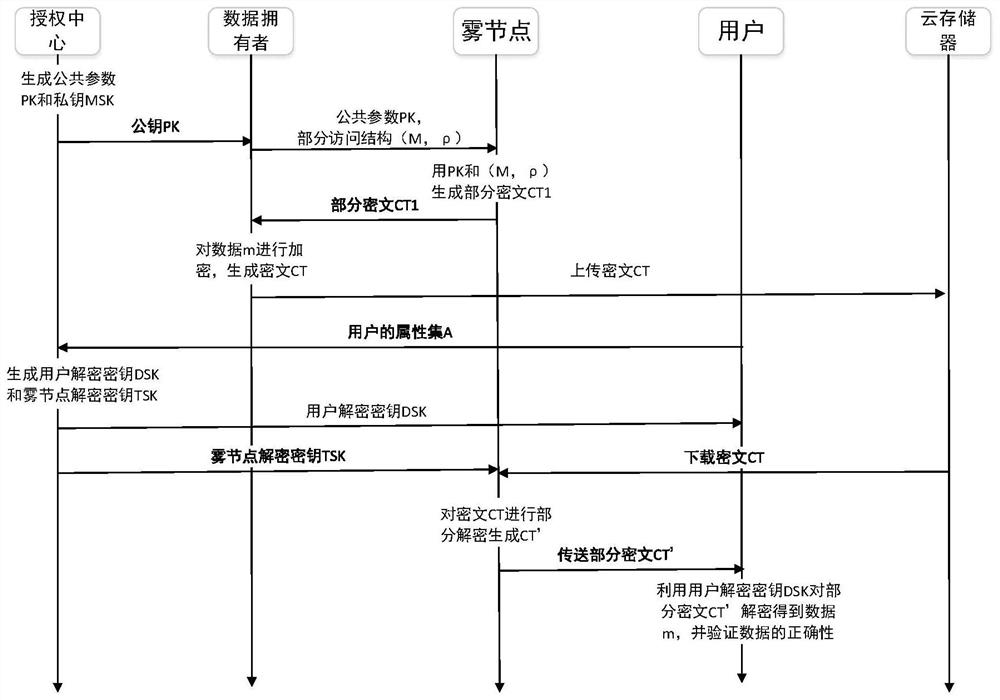
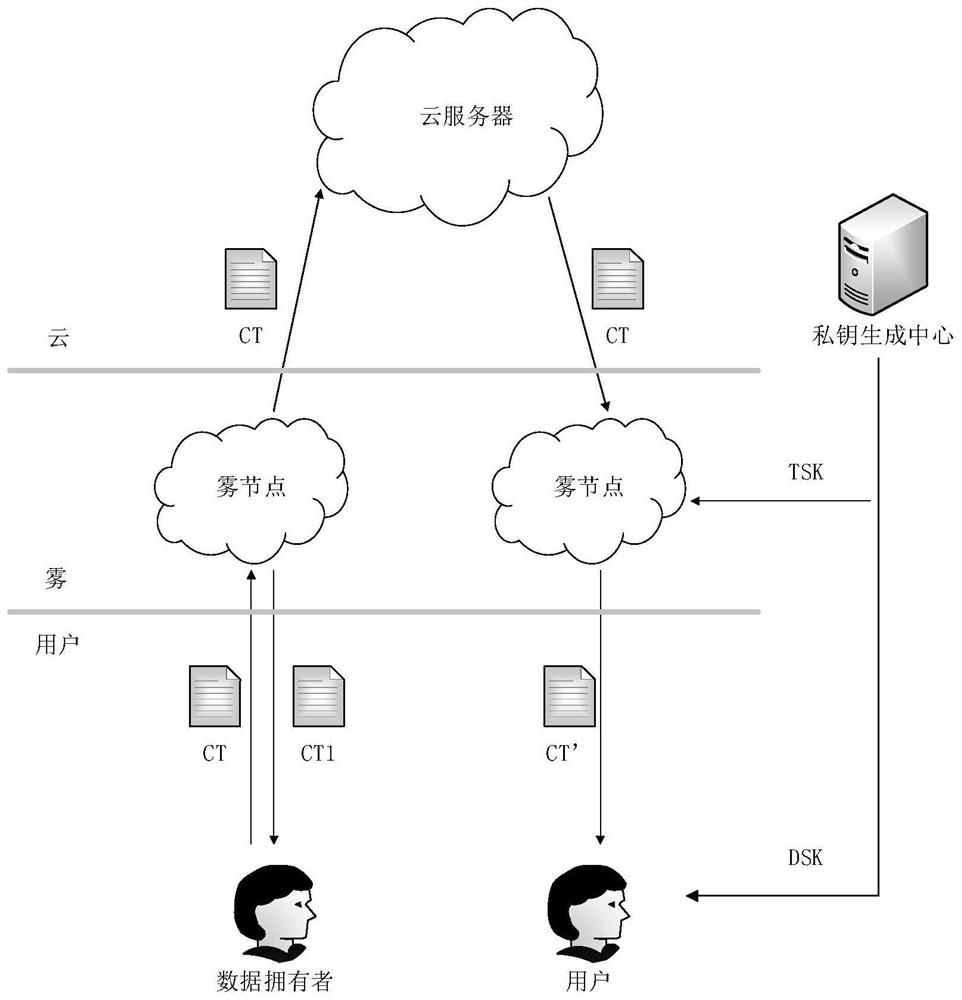
[0058] A privacy protection system based on CP-ABE ciphertext access control in a fog computing environment, such as Figure 1-2 As shown, it includes an initialization module, a private key generation module, an encrypted data module, and a decrypted ciphertext module. The encrypted data module includes a fog node encryption module and a data owner encryption module. The decrypted ciphertext module includes a fog node decryption module, User decryption module, where...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com